Authentication & Passwordless
Articles on how modern passwordless authentication is replacing passwords.

Featured
What is a YubiKey and How Does It Work? The Complete Guide
YubiKey is a hardware security key that uses cryptographic authentication instead of passwords. The blog highlights how traditional methods like passwords, SMS, and authenticator apps fail against modern threats like phishing and credential theft. The guide breaks down how a YubiKey works, including its secure chip, authentication flow, and supported protocols like FIDO2 and OTP. It compares YubiKey with other authentication methods to show why it offers stronger, phishing-resistant security. It also covers real-world use cases, enterprise deployment, and its limitations in frontline and shared device environments.

Continuous Authentication: What It Is, How It Works, Benefits & Best Practices
Continuous authentication represents a fundamental shift in identity security. Traditional login methods verify users once and grant lasting access. This approach leaves systems vulnerable to session hijacking and credential theft. This guide explores the definition, core components, implementation strategies, real-world applications, and best practices of continuous authentication. Learn how behavioral biometrics, contextual signals, and machine learning enable real-time identity verification.

Smart Card Authentication: A Complete Guide
Smart card authentication delivers hardware-backed identity verification for high-security workforce access. This comprehensive guide examines the operation, architecture, and implementation considerations of smart cards. Learn the benefits, practical use cases, and implementation best practices for deploying smart card authentication.

Is Passwordless Authentication Safe for Modern Businesses? Expert Insights
Passwordless authentication replaces traditional passwords with cryptographic keys, biometrics, and device-based verification methods. Organizations adopt these systems to eliminate credential theft, reduce phishing attacks, and remove password management overhead. This guide explains how passwordless authentication is safer than traditional passwords. Get a comparison of different passwordless methods and learn which approach best suits specific use cases.
What Is Single Sign-On (SSO) and How Does It Work?
Single Sign-On (SSO) transforms how organizations manage user authentication across multiple applications and services. This comprehensive guide explores what SSO is, how it works, and why it matters for modern enterprises. Learn about different SSO types, implementation protocols, and the key advantages of adopting SSO solutions. The guide also covers practical use cases, step-by-step implementation processes, and expert advice on choosing the right SSO provider.

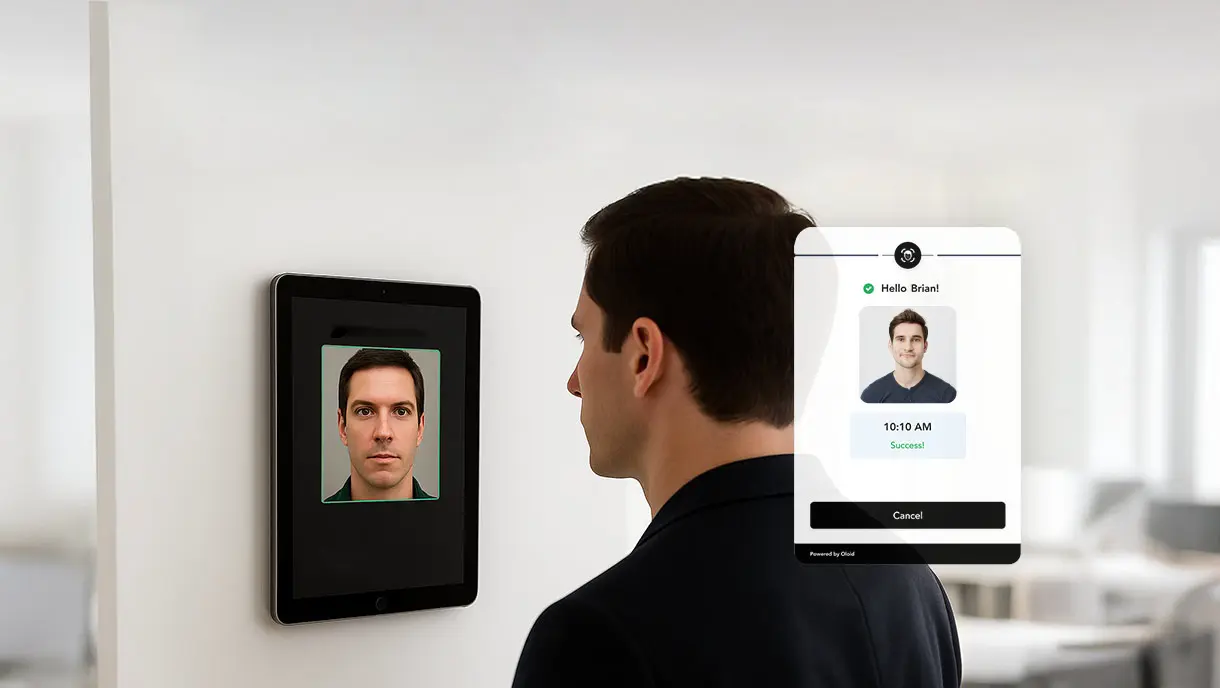
What Is Biometric Authentication And How Does It Work?
Biometric authentication has transformed how organizations verify identity and secure access. This technology uses unique physical or behavioral traits like fingerprints, facial features, or voice patterns to replace vulnerable password-based systems. This guide covers the fundamentals of biometric authentication, including how the technology works and the various types available. You'll find practical implementation strategies, real-world industry applications, and key benefits for enterprises.

Final Thoughts on Two-Factor Authentication
Two-factor authentication (2FA) adds a critical security layer beyond passwords to protect your digital accounts. This comprehensive guide explores what 2FA is, how it works, and why it matters for both individuals and enterprises. Learn common authentication methods, key benefits, real-world applications, and best practices for implementation.

What Is Passwordless MFA? A Complete Guide to Secure and Frictionless Authentication
Passwordless MFA eliminates traditional passwords while maintaining multi-factor security through biometrics, security keys, and device-based authentication. This comprehensive guide explores what passwordless MFA is, its business benefits, implementation strategies, and best practices for overcoming common challenges. Learn how leading organizations are adopting passwordless multi-factor authentication to strengthen security, improve user experience, reduce IT costs, and meet compliance requirements.

What Is Multimodal Biometric Authentication and How Does It Work?
Multimodal biometric authentication combines multiple biometric traits to create highly secure identity verification systems. This comprehensive guide examines how these advanced systems operate, their key advantages, and practical implementation strategies. Learn about different biometric modalities, fusion techniques, industry applications, and best practices for deployment.

A Step-by-Step Guide for Implementing Passwordless Authentication
How to move beyond passwords and implement passwordless authentication without disrupting users? What does it take to implement passwordless authentication securely and at scale? This blog breaks down a 7-step implementation process, common challenges enterprises face, and best practices for smooth adoption.
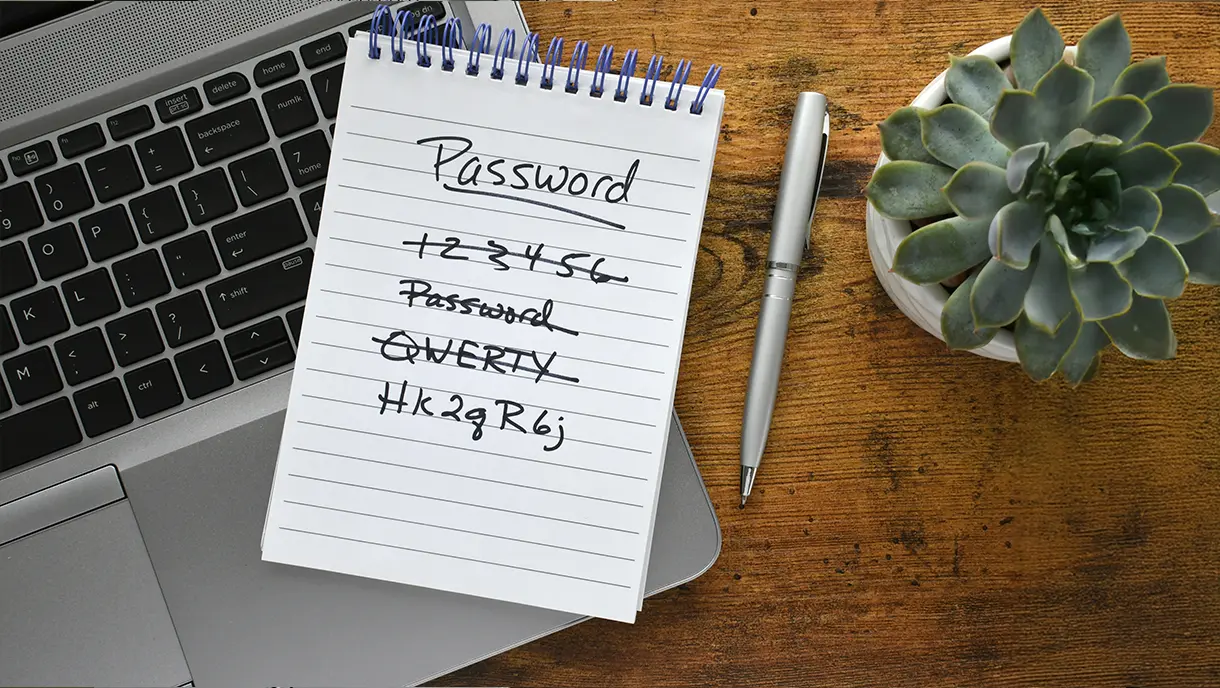
Top 10 Password Alternatives: What’s Replacing Passwords in 2026?
Organizations are shifting away from traditional passwords toward passwordless methods such as biometrics, passkeys, and SSO. This guide explores 10 leading password alternatives transforming authentication. Examine each alternative's security level, key highlights, and ideal use cases.

6 Types of Two-Factor Authentication (2FA) Methods
Two-factor authentication (2FA) serves as an additional security layer that prevents intruders from accessing your account even if they steal your credentials. This guide walks you through every major 2FA method, explaining how each works in real-life scenarios, where they are most effective, and how to choose the right protection for your specific situation.

Passwordless Authentication: What It Is and How It Works
Passwordless authentication replaces traditional passwords with secure, user-friendly methods like biometrics, passkeys, and magic links. This blog explores how it works, its key benefits, and why it’s becoming essential for modern identity security. Learn how platforms like OLOID enable seamless, password-free access across the workforce.
A Complete Guide to Contactless Authentication for Modern Workplaces
Contactless authentication is reshaping how organizations secure access without compromising hygiene or user experience. This guide breaks down everything you need to know, from biometric technologies and mobile credentials to real-world applications across healthcare, manufacturing, and finance. Get practical insights on avoiding common pitfalls and implementing solutions that actually work.

Contactless Biometrics: The Future Of Secure And Hygienic Authentication
Struggling with hygiene risks, security vulnerabilities, and operational bottlenecks from traditional authentication systems? This guide explains how contactless biometrics solves these critical workplace challenges. Learn why leading organizations abandon touch-based fingerprint scanners for AI-powered facial recognition and palm vein technology.

Facial Authentication Explained: How It’s Transforming Digital Security
Facial authentication is transforming digital security by replacing passwords with secure biometric verification using AI-powered algorithms. This guide explains how facial authentication works, from detection to verification. Explores its benefits, including enhanced security, contactless convenience, and operational efficiency.

Enterprise SSO: The Key to Secure, Seamless Access Management for Modern Businesses
Enterprise SSO simplifies secure access by allowing employees to log in once and use multiple business applications without having to re-enter their credentials. This blog examines how Enterprise SSO operates, its key benefits for security, compliance, and productivity, and the challenges organizations encounter during implementation. It also outlines best practices and guidance on selecting the right SSO solution.
![10 Best SSO Solutions for 2026 [Expert Comparison]](https://cdn.prod.website-files.com/669022e11afe3d75b7a05794/69009aaea31a0ccf03076c62_sso-solutions.webp)
10 Best SSO Solutions for 2026 [Expert Comparison]
Modern Single Sign-On solutions deliver secure, seamless access across enterprise applications while reducing password fatigue and identity risks. This comprehensive comparison of the 10 best SSO platforms examines authentication protocols, integration capabilities, and real-world performance. From Okta to Microsoft Entra ID and OLOID, discover which SSO solution aligns with your organization's security, compliance, and user experience priorities.

Top 12 Industries Using Facial Authentication
Facial authentication is revolutionizing operations across various industries. This guide examines how sectors like manufacturing, healthcare, retail, banking, pharmaceuticals, and energy, among others, are leverage biometric technology. Explore specific use cases, implementation strategies, and tangible benefits, including enhanced security, fraud prevention, and operational efficiency.
![10 Best Multi-Factor Authentication Solutions of 2026 [Latest Rankings]](https://cdn.prod.website-files.com/669022e11afe3d75b7a05794/68f0bfd7e94d6540eb1a836a_multi-factor-authentication-solutions.webp)
10 Best Multi-Factor Authentication Solutions of 2026 [Latest Rankings]
Modern MFA solutions combine context-aware policies, biometric verification, and seamless integrations to prevent credential theft and unauthorized access. This detailed comparison of the 10 best MFA tools for 2026 examines each platform’s unique strengths, deployment options, and ROI. From Microsoft Entra ID to OLOID and Okta, you’ll discover which authentication solution aligns best with your organization’s growth, compliance, and Zero Trust security strategy.

Step-By-Step Guide to Seamless MFA Implementation
Effective MFA implementation is crucial for protecting organizations against password breaches and unauthorized access. This blog offers a step-by-step guide to deploying multi-factor authentication, from assessing infrastructure to training users and optimizing performance. Learn about common implementation pitfalls, their solutions, and best practices to simplify multi-factor authentication adoption while strengthening overall security.
Passwordless Authentication for Zero-Trust: Modern Security Without Compromise
Passwordless authentication is transforming enterprise security by eliminating passwords, reducing vulnerabilities, and enhancing user experience. This blog explores methods, implementation steps, and key considerations for adopting passwordless authentication while supporting Zero-Trust principles. OLOID’s platform offers a secure, scalable solution to help organizations modernize access management effectively.

What Is RFID Authentication and How Does It Work?
RFID authentication uses radio frequency technology to enable secure, contactless identity verification. It works through RFID tags and readers to grant quick and reliable access, making it a strong alternative to traditional methods like passwords or PINs. This blog explores how RFID authentication works, its applications, benefits, challenges, and best practices for effective implementation.

Phishing-Resistant MFA: Complete Guide to Modern, Secure Authentication
Traditional multi-factor authentication fails against modern phishing attacks. Phishing-resistant MFA uses cryptographic technology and hardware-bound credentials to eliminate vulnerabilities that attackers exploit. This guide covers how it works, key technologies like FIDO2 and security keys, implementation steps, and real-world attack scenarios it blocks. Learn the benefits, including faster logins and stronger security.

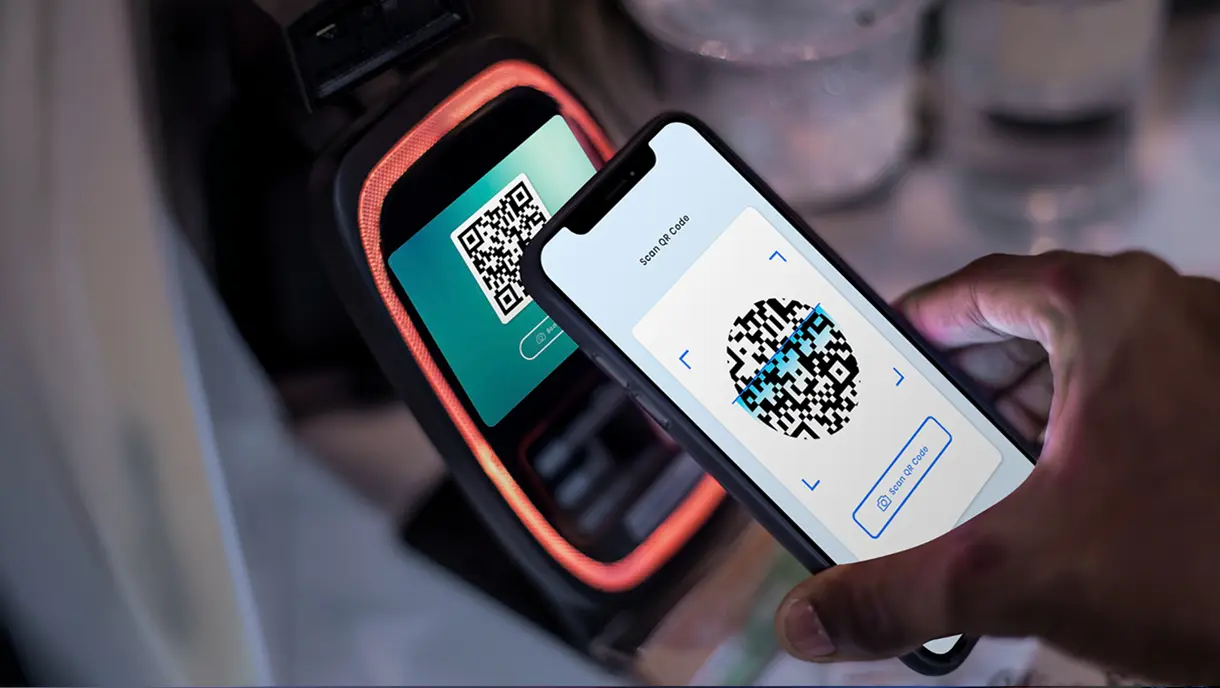
The Ultimate Guide to QR Code Authentication for Modern Security
QR code authentication revolutionizes organizational security by eliminating password vulnerabilities. This comprehensive guide covers passwordless authentication through scannable codes, comparing static versus dynamic implementations, and demonstrating superior security over traditional methods. Learn implementation methodology, security best practices, compliance requirements, risk management strategies, and real-world solutions for addressing modern authentication challenges.

NFC Authentication: Basics, Benefits, Models, and Implementation
NFC authentication revolutionizes workplace security by eliminating password vulnerabilities. It is a short-range wireless technology that verifies identity within a contactless interaction distance of four centimeters. This blog provides a comprehensive understanding of what Near Field Communication (NFC) authentication is, why it is a great alternative to traditional passwordless-based authentication, and how businesses can implement it.

PIN Authentication: How It Powers Modern Business Security
PIN authentication revolutionizes workplace security by eliminating password vulnerabilities while providing instant access for frontline workers using shared devices. This technology offers superior phishing resistance through local validation and integrates seamlessly with comprehensive passwordless solutions that combine biometric verification, badge access, and NFC cards. Explore how PIN authentication works and how it can improve your security in this detailed guide.

10 Key Passwordless Authentication Best Practices to Streamline Access Management
Passwordless authentication eliminates security vulnerabilities while improving user experience across organizations. This guide explores 10 essential passwordless authentication best practices. Following these proven strategies enables organizations to deploy secure, user-friendly authentication systems that reduce costs and enhance their security posture.
![10 Best Passwordless Authentication Solutions of 2026 [Latest Rankings]](https://cdn.prod.website-files.com/669022e11afe3d75b7a05794/68f236069554ac4369a98ae4_best-passwordless-authentication-solutions.webp)
10 Best Passwordless Authentication Solutions of 2026 [Latest Rankings]
Passwordless authentication has evolved from a security trend to a business necessity, with organizations seeking alternatives to traditional password-based systems that create vulnerabilities and operational inefficiencies. This comprehensive guide examined 10 leading passwordless authentication solutions, each designed for different organizational needs and use cases.
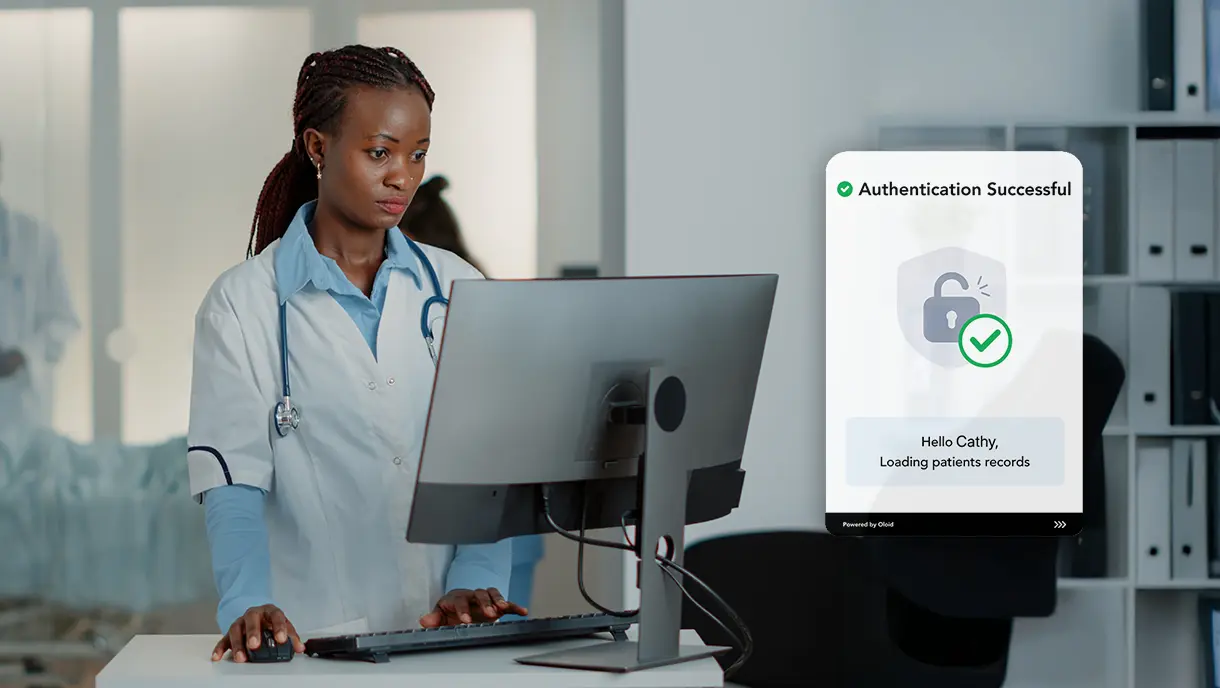
SSO for Healthcare: Simplifying Access While Strengthening Security
The write-up explains how Single Sign-On (SSO) simplifies access to multiple healthcare systems, reducing password fatigue, improving clinical efficiency, and strengthening data security. It highlights unique compliance needs, key features of healthcare-focused SSO, implementation best practices, and how OLOID’s passwordless authentication platform enhances security, streamlines workflows, and supports HIPAA and DEA EPCS compliance for modern healthcare environments.

Biometrics in Healthcare: Transforming Patient Security and Care
Biometric technologies like fingerprint, facial, iris, and voice recognition are revolutionizing healthcare by improving patient identification, security, and operational efficiency while ensuring regulatory compliance. This blog on biometrics in healthcare highlights real-world uses, implementation challenges, and how platforms like OLOID streamline passwordless authentication for safer, faster, and more patient-friendly care.
Making every day-in-the-life of frontline workers frictionless & secure!
Get the latest updates! Subscribe now!



