Palm authentication
Palm Authentication leverages unique palm vein patterns and prints for secure, touch-free access, offering advanced biometric recognition for login or multifactor authentication (MFA).

Re-imagine the authentication processes with palm as a factor
.webp)
Liveness Detection
Prevents presentation attacks by verifying that a real, living palm is being scanned. Works reliably despite minor movements or changes, such as scars or lighting variations.
.webp)
Offline Authentication
Palm templates can be stored locally for offline authentication. Data automatically syncs with the server when connectivity is restored.
.webp)
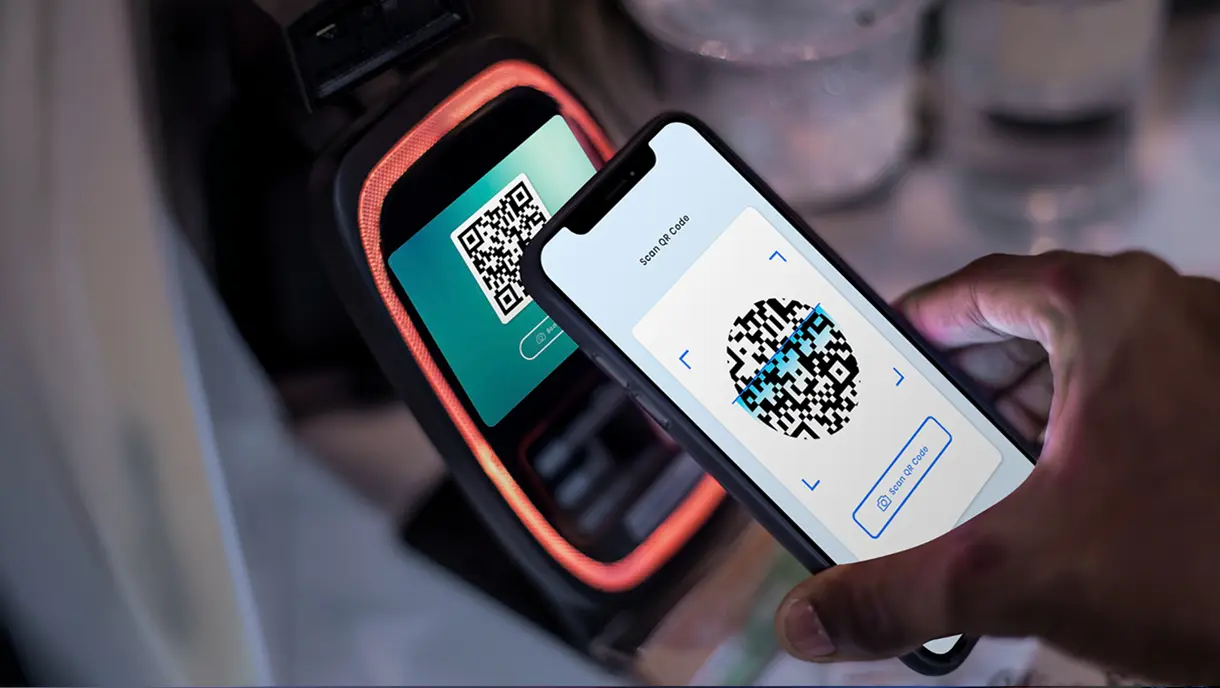
Supplemental Factors
QR codes can be combined with other factors, such as NFC, PIN, or biometric authentication, for flexible and secure MFA configurations.
Palm authentication
OLOID’s palm-based authentication provides a non-contact, hygienic biometric solution ideal for modern workplaces. Utilizing advanced imaging and vein-mapping technologies, this method ensures high accuracy and security while delivering a seamless user experience.
- Dual Methods of Authentication: Supports palm image recognition using standard cameras & vein-mapping via IR cameras.
- Non-Contact Interaction: Touch-free authentication enhances hygiene, making it suitable for PPE-required environments.
- High Accuracy: Leverages unique palm vein patterns and prints to provide reliable and secure authentication.
- Fast and Intuitive: Delivers sub-second authentication for seamless user experiences.

.webp)
.webp)
.webp)
.webp)
.webp)

OLOID’s Palm authentication ensures secure, rapid credential capture and verification
Here's how the Palm authentication works:
- The user hovers their palm over a standard or IR camera.
- The system captures either a palm print or vein map, depending on the camera type.
- Liveness detection verifies the palm’s authenticity, and credentials are securely validated in under a second.
- Enhanced Usability: Palm authentication is touch-free, reducing wear and tear on devices while ensuring a hygienic user experience in environments like healthcare and manufacturing.
.webp)
Supports a wide range of devices, systems and applications
Palm authentication integrates effortlessly with modern hardware and platforms. Fully compatible with Windows, iOS, Android, and web platforms, offering a consistent experience across devices.
- Tablets
- Kiosks
- Windows PCs
- Thin Clients
- Web & Native Applications
.webp)
Credential lifecycle management
OLOID simplifies the management of palm-based credentials through robust lifecycle management tools:
- Assisted Onboarding: Administrators can guide users through the palm enrollment process to ensure accuracy and security.
- Self-Onboarding Options: Users can enroll their palm credentials independently using step-by-step prompts.
- Centralized Management: Ensures palm credentials are securely stored, with the ability to update or revoke access as needed.
.webp)
Privacy, security & compliance
Palm authentication adheres to rigorous standards for biometric data privacy and security:
- End-to-End Encryption: Biometric data is securely encrypted during transmission and at rest.
- No Image Retention: Palm data is converted into secure templates that cannot be reverse-engineered.
- Liveness Detection: Prevents spoofing attempts, ensuring the authenticity of each interaction.
- Global Compliance: Fully adheres to GDPR, HIPAA, and other data protection regulations, ensuring secure implementation.
- SOC 2 Type II Certification: Meets industry standards for operational effectiveness and data security, making it reliable for enterprise deployments.
.webp)
Ideal usage scenarios
Palm authentication is ideal for:
- Hygiene-Critical Environments: Perfect for industries like healthcare, food processing, and manufacturing where touch-free workflows are essential.
- High-Security Areas: Provides robust biometric security for sensitive access points.
- Flexible Deployment Needs: Works seamlessly with standard or IR cameras to meet diverse operational requirements.
- Enhanced Security Configurations: Combine palm authentication with other factors like NFC, QR codes, or PINs for robust MFA solutions.
Sign up for a Free Trial
Featured integrations
OLOID platform seamlessly integrates with your existing infrastructure for easy install & ongoing management.
Related posts

Biometric ID Guide: Secure Your Digital Identity
Biometric identification uses unique physical or behavioral traits like fingerprints, facial features, or voice to verify identity. Common methods include facial recognition, fingerprint scanning, and voice recognition. These solutions offer enhanced security, accuracy, and convenience compared to traditional passwords. As costs decline, even small businesses can adopt biometric systems to improve access control and protect against threats.

What Is Biometric Authentication And How Does It Work?
Biometric authentication has transformed how organizations verify identity and secure access. This technology uses unique physical or behavioral traits like fingerprints, facial features, or voice patterns to replace vulnerable password-based systems. This guide covers the fundamentals of biometric authentication, including how the technology works and the various types available. You'll find practical implementation strategies, real-world industry applications, and key benefits for enterprises.
A Complete Guide to Contactless Authentication for Modern Workplaces
Contactless authentication is reshaping how organizations secure access without compromising hygiene or user experience. This guide breaks down everything you need to know, from biometric technologies and mobile credentials to real-world applications across healthcare, manufacturing, and finance. Get practical insights on avoiding common pitfalls and implementing solutions that actually work.
FAQs on palm authentication for frontline systems
What type of palm authentication does OLOID support?

OLOID supports palm vein–based biometric authentication, a contactless method that verifies identity using the unique vein patterns inside a user’s palm. Near-infrared imaging captures these internal patterns and converts them into encrypted biometric templates for secure login. Because vein structures are internal and highly distinctive, palm vein authentication delivers strong accuracy and resistance to forgery.
What hardware and devices are required for palm authentication?

Palm authentication requires a palm vein sensor equipped with near-infrared imaging technology to capture internal vascular patterns. These sensors are typically mounted near shared workstations, kiosks, or access control points and integrate securely with OLOID through supported SDKs or APIs. Compatible environments include enterprise PCs, rugged terminals, kiosks, and dedicated biometric stations.
How secure is palm vein authentication?

Palm vein authentication is highly secure because it relies on internal vascular patterns that are not visible or easily replicated. Near-infrared illumination captures living tissue characteristics, making spoofing attempts significantly more difficult than with surface-based biometrics.
OLOID protects biometric data using encrypted template storage and secure matching protocols, reducing the risk of replay attacks or template theft while maintaining strong authentication assurance.
OLOID protects biometric data using encrypted template storage and secure matching protocols, reducing the risk of replay attacks or template theft while maintaining strong authentication assurance.
Does palm authentication work offline?

Palm biometric deployments can be configured to support offline-tolerant verification when network connectivity is intermittent. Local devices securely cache required templates and authentication policies, allowing authorized users to continue authenticating. Once connectivity is restored, systems synchronize with backend identity platforms based on the configured architecture.
Is palm authentication suitable for hygiene-critical and high-security environments?

Yes. Palm vein authentication is fully contactless—users hold their hand near the sensor without touching shared hardware, supporting hygiene protocols in environments such as healthcare and food processing.
For higher-assurance workflows, palm authentication can also be combined with additional factors such as a PIN, badge/NFC credential, or mobile token to meet elevated security or regulatory requirements.
For higher-assurance workflows, palm authentication can also be combined with additional factors such as a PIN, badge/NFC credential, or mobile token to meet elevated security or regulatory requirements.
Making every day-in-the-life of frontline workers frictionless & secure!
Get the latest updates! Subscribe now!





























