OLOID + Ping Identity
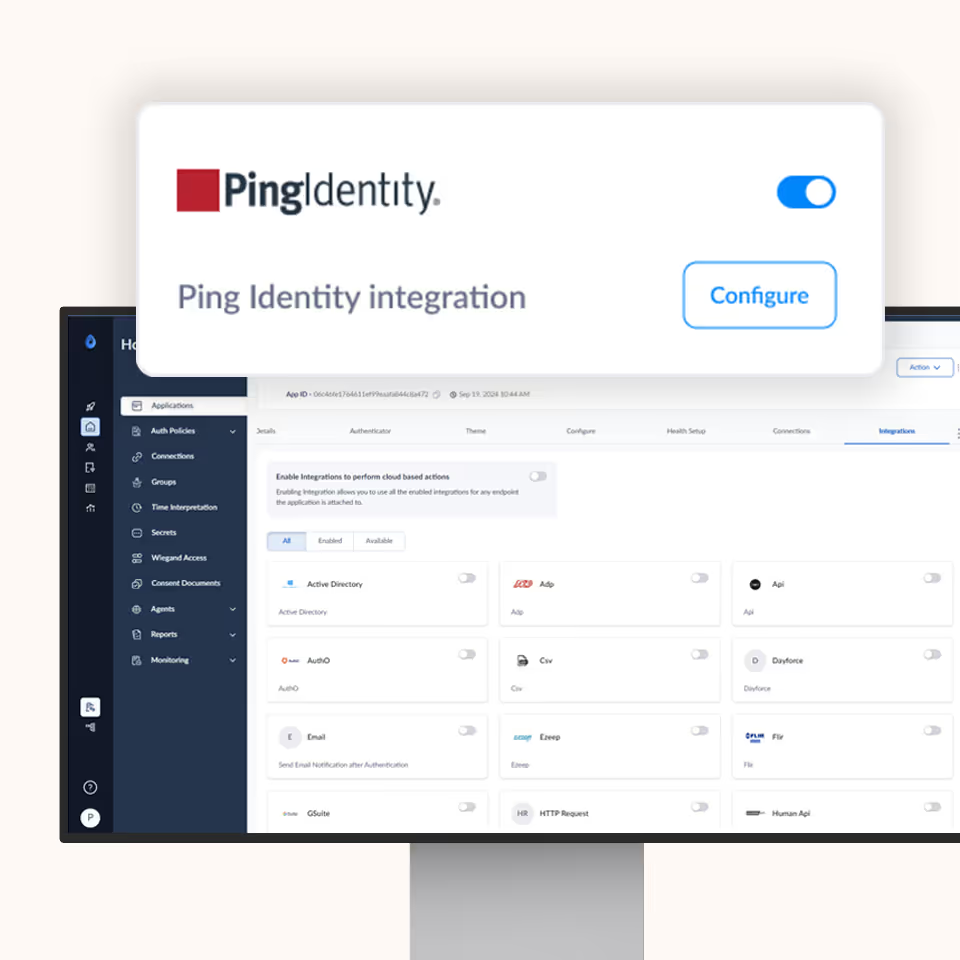
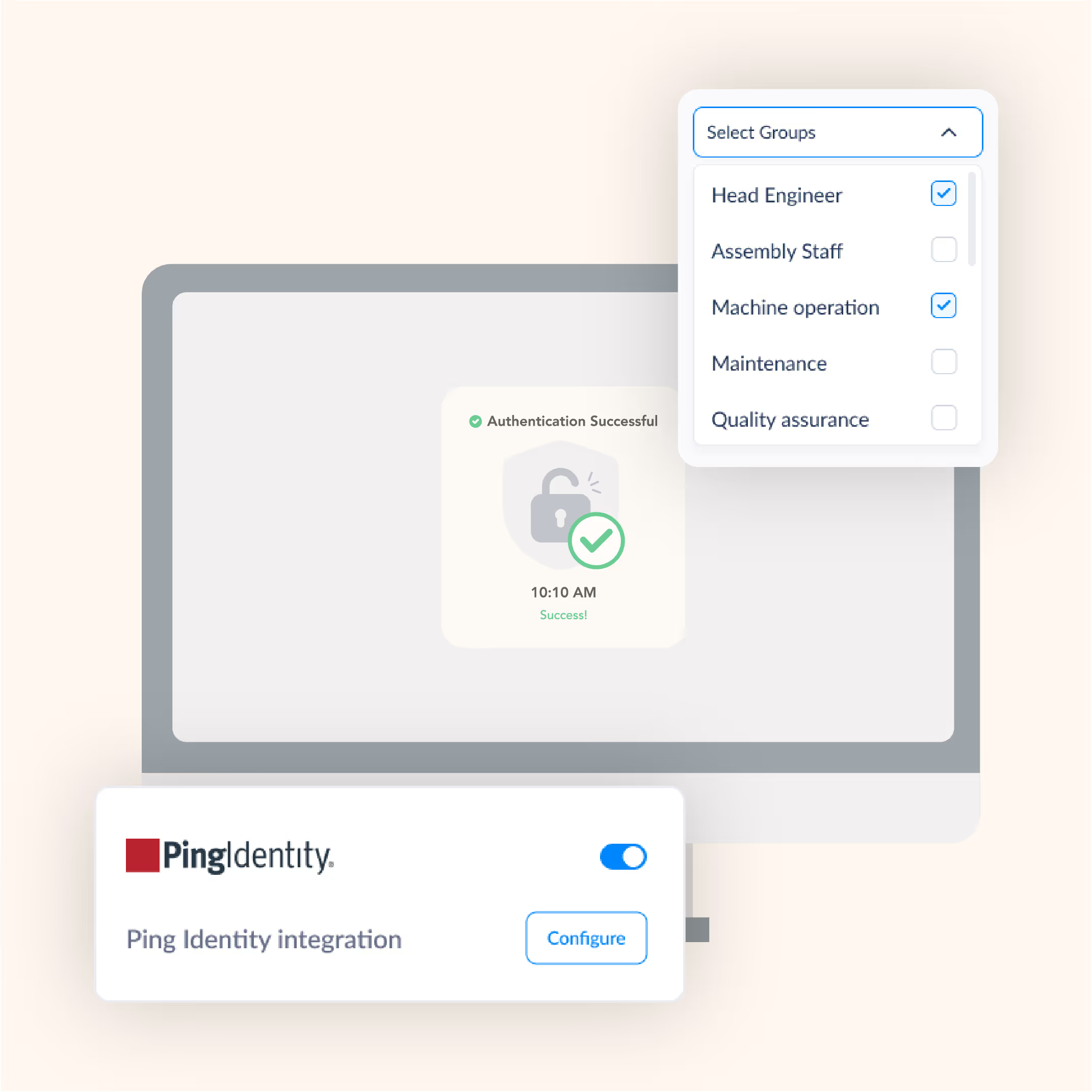
OLOID integrates with Ping Identity to deliver seamless, passwordless multi-factor authentication (MFA) for frontline workers using shared devices. This integration enhances security, reduces login friction, and improves workforce productivity across industries like retail, healthcare, and manufacturing.
Features & benefits
Multiple modes for establishing identity at your workplace Modern physical access for smartphone & non-smartphone users
Secure and Efficient Access with OLOID + Ping Identity
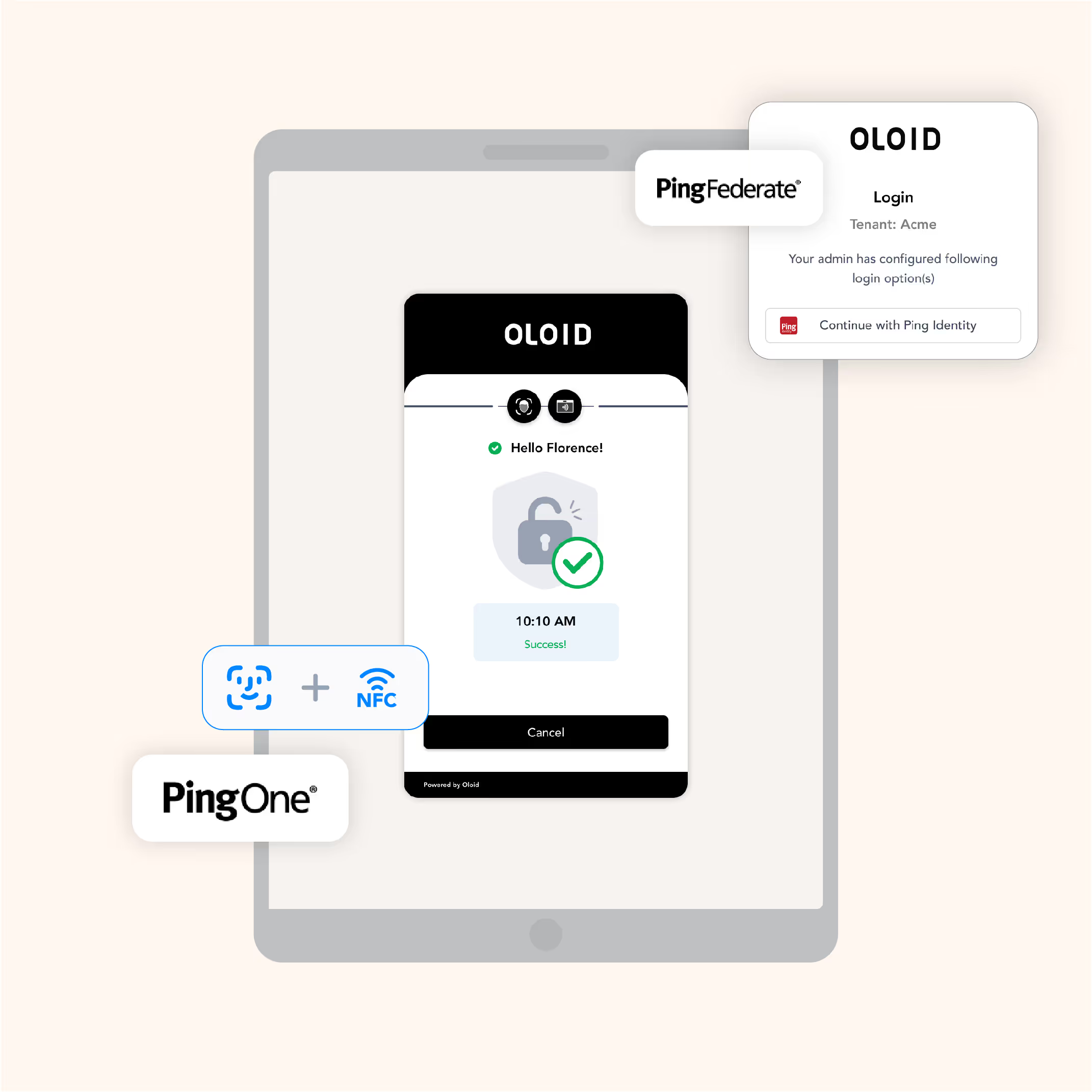
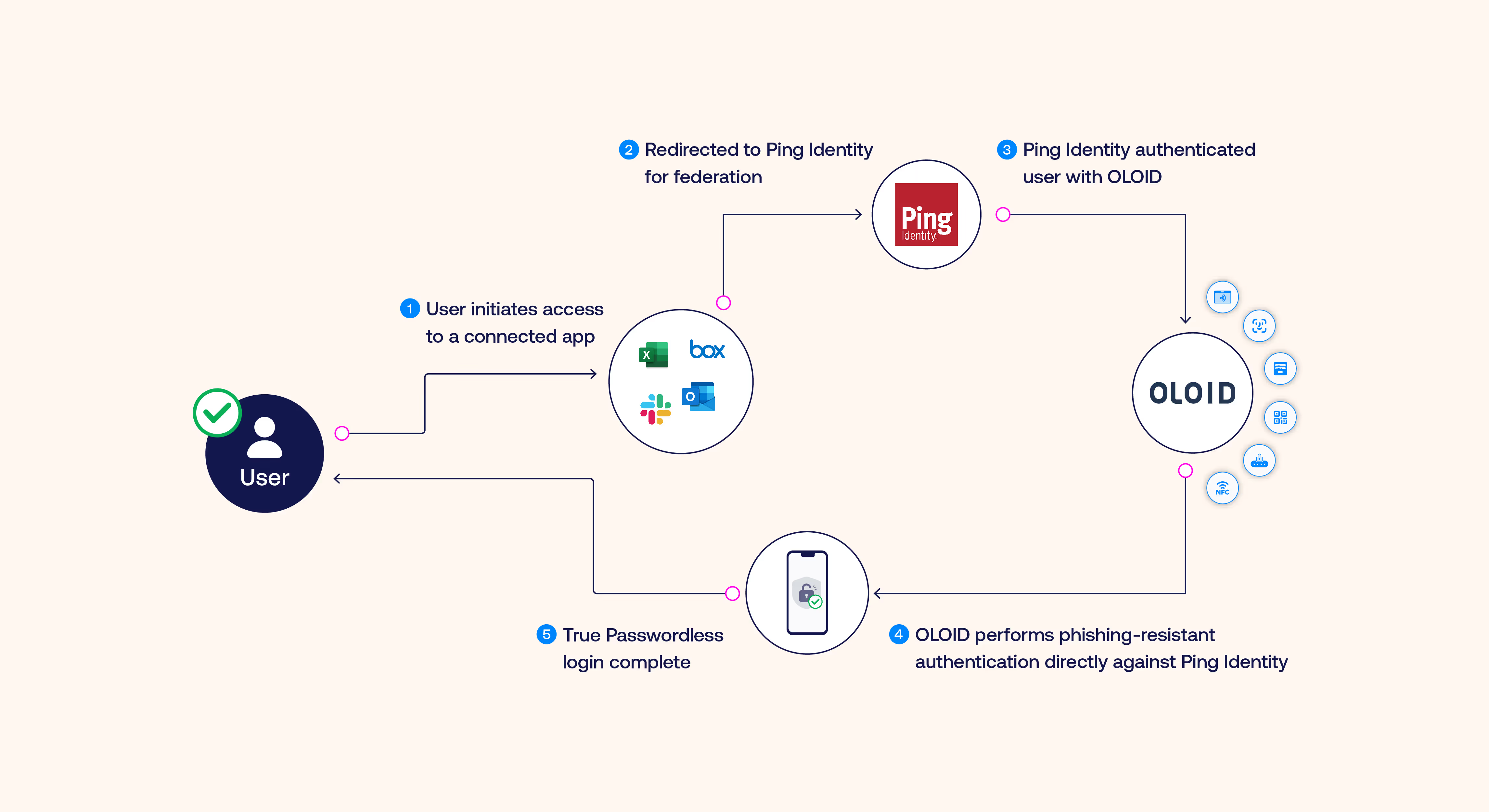
- Passwordless MFA with PingOne for Workforce: OLOID integrates with PingOne for Workforce, enabling phishing-resistant, passwordless MFA across shared and personal devices. Users benefit from fast and secure access without the hassle of passwords.
- Single Sign-On with PingFederate: OLOID works with PingFederate to deliver passwordless Single Sign-On (SSO), allowing workers to authenticate once and access all Ping-connected applications seamlessly.
- Centralized Identity with PingDirectory: OLOID’s integration with PingDirectory ensures centralized, passwordless identity management across all devices and applications, making it easy to apply security policies consistently.
Simplified Security and User Experience
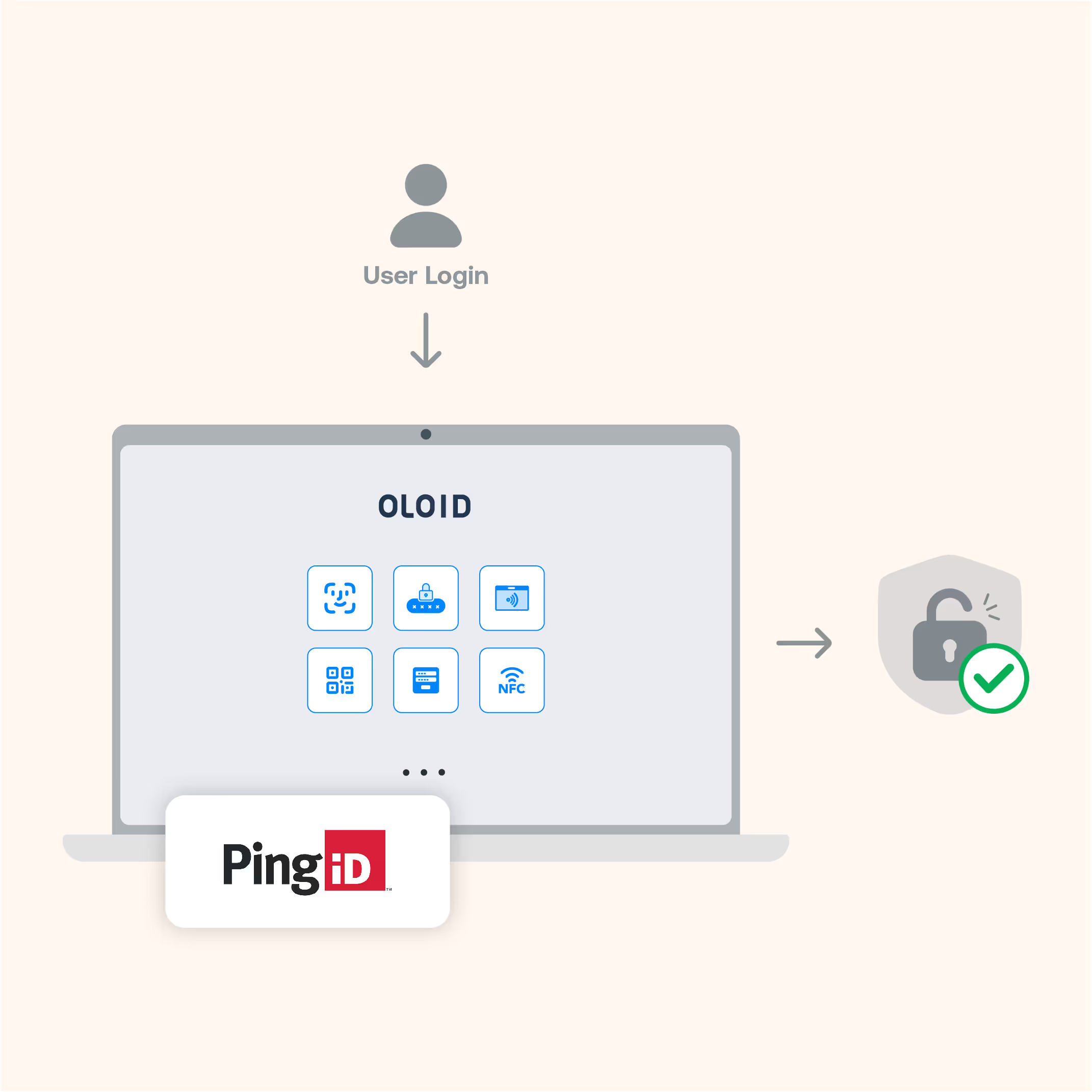
- PingID MFA: Combine OLOID’s passwordless MFA with PingID, offering flexible authentication methods such as biometrics, push notifications, and passkeys, enhancing security for shared devices.
- Cross-Platform Passwordless Login: OLOID extends passwordless login to multiple platforms, enabling secure access to Windows, Android and IOS devices.
- Adaptive Authentication: OLOID enhances Ping’s Adaptive Authentication, dynamically adjusting security based on real-time risk signals like location and behavior, ensuring frictionless access for users while strengthening security.
- Automatic Identity Pass-Through: When users authenticate with OLOID’s passkeys on a desktop, their identity is automatically passed to PingFederate, allowing access to all Ping-connected applications without additional steps unless further verification is needed.
Enhanced Security with OLOID + Ping Identity
- PingAccess Integration: OLOID integrates with PingAccess to provide passwordless, role-based access control for applications and APIs. This ensures that only authorized users can access sensitive resources securely.
- Protection Against Modern Threats: OLOID’s passwordless authentication defends against credential-based attacks, such as phishing and credential stuffing, offering full protection from man-in-the-middle (MitM) and push bombing attacks.
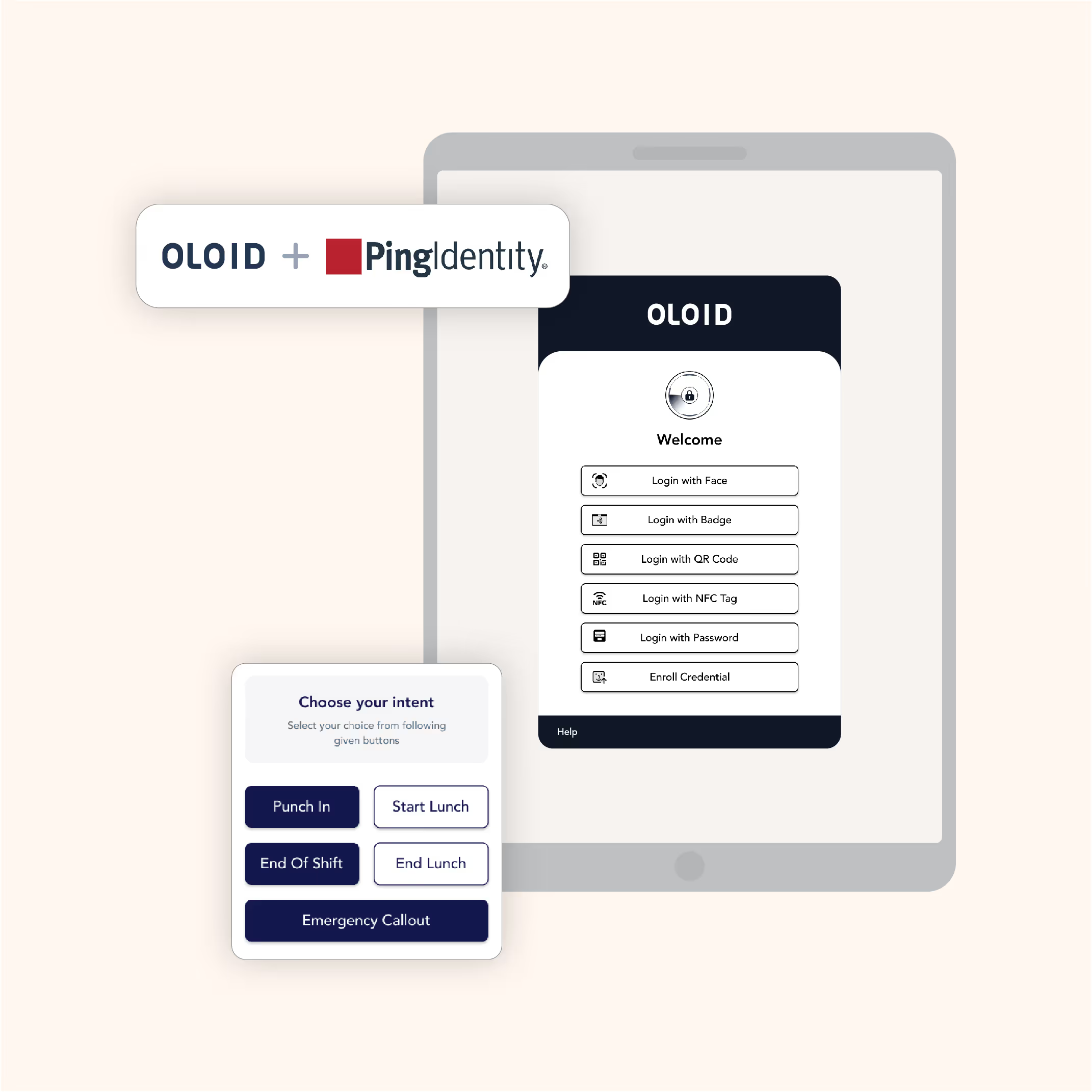
Built for Frontline Workers: OLOID + Ping Identity
- Fast, Touchless Login with PingID: OLOID enables fast, touchless authentication via PingID, using passkeys, biometrics, or mobile devices for seamless login to shared devices.
- Seamless Shift Transitions: OLOID and Ping simplify shift changes by allowing workers to log in and out of shared devices quickly without entering passwords, reducing downtime.
- Unified Access Across IT and OT Systems: OLOID extends Ping’s identity management capabilities to both IT and operational technology (OT) systems, ensuring secure, passwordless access for all roles in your workforce.



Ping Architecture Diagram
A visual representation of OLOID + PING Architecture

Benefits You Can Quantify
Save Time
Save 45–60 seconds per authentication & reclaim hours of clinician time every week
Reduce IT Burden
80% fewer password‑reset tickets means IT teams focus on higher‑value work
Stronger Security
Phishing‑resistant factors and real‑time policy controls
Happier Clinicians
Frictionless login keeps attention on patient care, not passwords

Compliance & Certifications

EPCS

Security & Privacy Rules
Authenticator Assurance
Level 2/3
Level 2/3

Audited infrastructure
Related posts


10 Best SSO Solutions for 2026 [Expert Comparison]
Modern Single Sign-On solutions deliver secure, seamless access across enterprise applications while reducing password fatigue and identity risks. This comprehensive comparison of the 10 best SSO platforms examines authentication protocols, integration capabilities, and real-world performance. From Okta to Microsoft Entra ID and OLOID, discover which SSO solution aligns with your organization's security, compliance, and user experience priorities.


SAML Authentication Explained: How It Works, Benefits, and Enterprise Use Cases
SAML remains a backbone for enterprise authentication, enabling secure workforce access and browser-based Single Sign-On across business applications. The article explains how SAML works through Identity Providers, Service Providers, and assertions, showing why organizations still rely on it for stable identity operations. It presents SAML as relevant today, balancing where it performs strongly and where newer identity models may work better. The piece places SAML within the modern identity landscape alongside zero trust, passwordless authentication, and identity orchestration.


Federated Identity Management: Complete Guide to Secure Cross-Domain Authentication
Federated Identity Management enables secure authentication across multiple organizations without creating separate accounts for each system. This blog explores how FIM works, key protocols like SAML and OAuth, implementation steps, real-world use cases, and best practices. Learn how enterprises use federation to reduce password fatigue, enhance security, and streamline access across cloud applications and partner ecosystems.
Making every day-in-the-life of frontline workers frictionless & secure!
Get the latest updates! Subscribe now!
Thank you! Your submission has been received!
Oops! Something went wrong while submitting the form.