AI-powered continuous authentication
For industries where devices and systems remain active for extended periods, continuous authentication using AI-powered computer vision ensures that only the intended user maintains access. By leveraging presence detection, organizations can prevent unauthorized access and mitigate security risks without disrupting workflows.

Industry use cases
Effortless, Secure Access for Frontline Workers with SSO
Manufacturing
Enhance security by locking devices on the production floor when operators leave, ensuring no tampering or accidental inputs.

Retail
Prevent unauthorized access to POS systems during unattended shifts by automatically logging out absent users.
Healthcare
Automatically lock workstations if a healthcare worker steps away, safeguarding sensitive patient data in EHRs.

Pharmaceuticals
Ensure lab systems and sensitive production equipment remain accessible only when authorized personnel are present, safeguarding intellectual property and compliance.

Contact Centers
Maintain compliance by ensuring agents stay logged in only when present at their desks, protecting sensitive customer data.

Enhance security with real-time user verification





Ongoing User Verification
Continuously authenticate the user in the background using methods like face recognition or presence detection.
- Automated continuous verification
- Seamless presence detection
- Ease of access

Session Timeout on Absence
Automatically lock devices or log out users when presence is no longer detected.
- Auto logout when no one is detected
- Approval workflow as needed
- Conditional access

Integration with Access Policies
Tailor authentication behavior to comply with role-based or contextual security requirements.
- Advanced encryption
- Role-based or contextual security
- Meet industry regulations

Real-Time Security Alerts
Notify administrators if unauthorized access attempts occur during a session. Setup alert rules based on your business needs.
- Instant alerts sent to managers
- Create alert rules
- Location tracking
Schedule a demo
Flexible and secure authentication that fits well
Choose amongst many form factors. Allow your staff to unlock any smart device with the same credentials.

Leading BPO Organization Secures Customer Data and Ensures Compliance with OLOID
Problem:
A top-tier BPO organization faced significant challenges in maintaining data security and compliance, especially with a remote workforce and high agent turnover. Password-based logins exposed customer data to potential risks, including unauthorized access by proxy workers and difficulties managing compliance due to agents sharing login credentials. Additionally, when agents left the organization, there was an ongoing risk of password misuse, complicating offboarding.
Solution:
OLOID’s passwordless authentication platform provided secure, facial recognition- and RFID-based access for agents across both remote and in-office settings. Continuous presence detection ensured that screens locked automatically when agents left their stations, while geo-fencing restricted data access to authorized regions. Real-time alerts and dashboards allowed supervisors to monitor agent activity and address potential security risks promptly.
Impact:
The BPO achieved a 40% reduction in unauthorized access incidents, improving data security and reducing the risk of proxy workers. Compliance costs decreased by 30% as the passwordless approach eliminated the need for traditional MFA devices and simplified regulatory adherence. By ensuring that agents were never exposed to passwords, the organization reduced the risk of credential misuse upon agent departure, strengthening its overall security posture and simplifying off-boarding. Supervisors reported improved productivity, as OLOID’s dashboards provided an efficient way to monitor agent activity and compliance in real time.


"OLOID's innovation has the potential to transform the hardware-centric access control industry into a software-as-a-service model with minimal capital expenditure."
Related posts
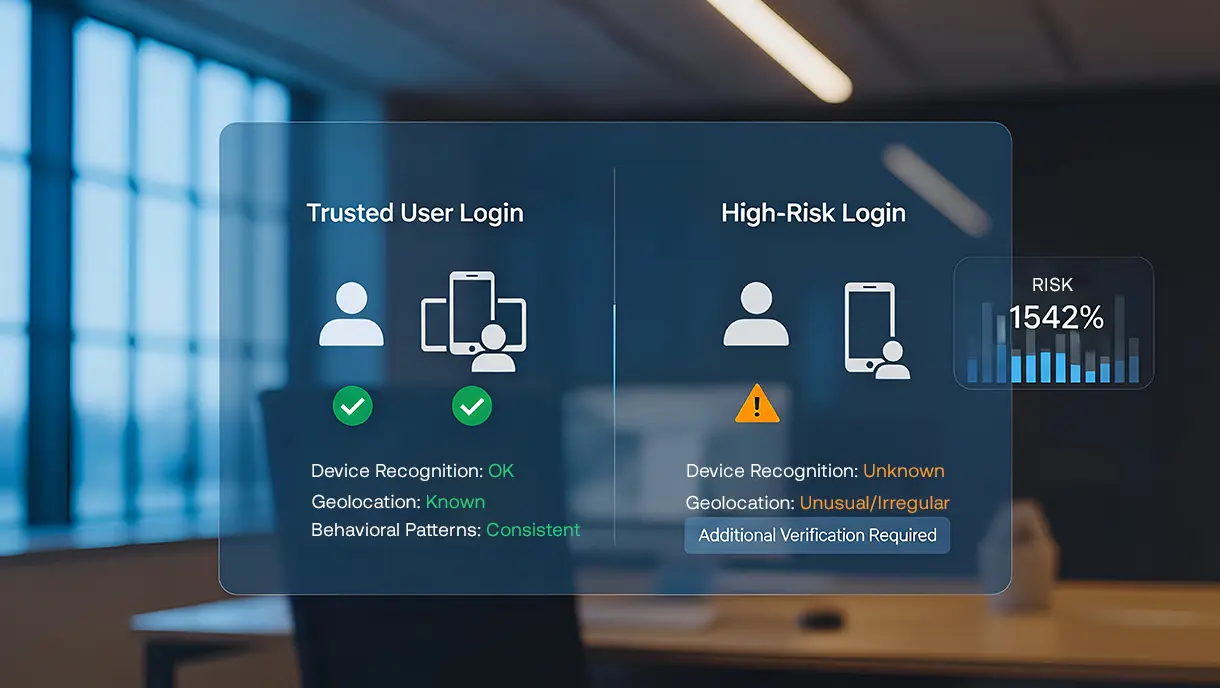
What Is Risk-Based Authentication? Benefits, Use Cases & How It Works
Risk-based authentication evaluates threat indicators and user behavior patterns before enforcing authentication requirements. Traditional static authentication applies the same verification regardless of the actual risk levels. This guide explains how risk-based systems calculate scores, analyze signals, and make dynamic decisions. Learn implementation strategies, regulatory compliance requirements, and best practices for deploying intelligent, risk-aware authentication.

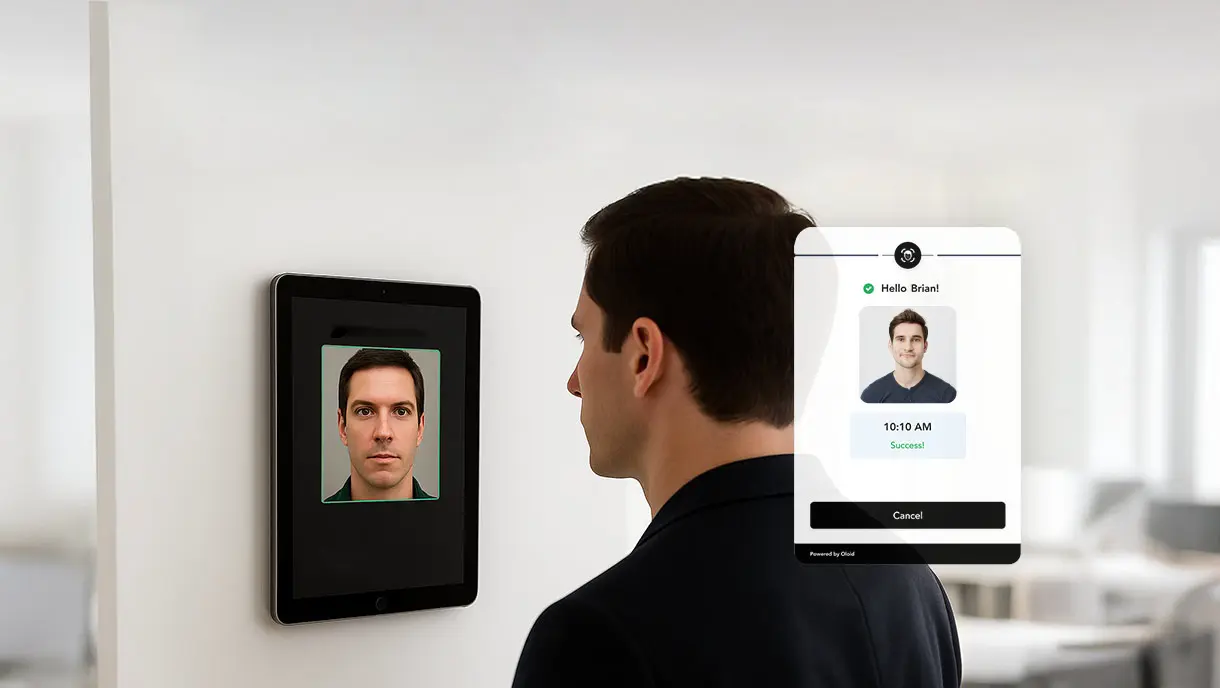
Continuous Authentication: What It Is, How It Works, Benefits & Best Practices
Continuous authentication represents a fundamental shift in identity security. Traditional login methods verify users once and grant lasting access. This approach leaves systems vulnerable to session hijacking and credential theft. This guide explores the definition, core components, implementation strategies, real-world applications, and best practices of continuous authentication. Learn how behavioral biometrics, contextual signals, and machine learning enable real-time identity verification.
Passwordless Authentication for Zero-Trust: Modern Security Without Compromise
Passwordless authentication is transforming enterprise security by eliminating passwords, reducing vulnerabilities, and enhancing user experience. This blog explores methods, implementation steps, and key considerations for adopting passwordless authentication while supporting Zero-Trust principles. OLOID’s platform offers a secure, scalable solution to help organizations modernize access management effectively.
FAQs on AI-powered continuous authentication for frontline systems
What is continuous authentication and presence detection?

Continuous authentication and presence detection use AI-powered computer vision to verify that the authenticated user remains physically present throughout an active session—not just at login. If the system detects that the user has stepped away, it can automatically lock the screen or log the session out to prevent unauthorized access.
How does presence detection protect unattended workstations?

Presence detection continuously monitors whether the verified user is still at the device. If the user leaves or is no longer detected, OLOID automatically locks the session. If another individual approaches the workstation, the system can also trigger security responses such as session lock or alerts, helping prevent unauthorized access to sensitive systems and data.
Does continuous authentication interrupt normal workflows?

No. Continuous authentication operates in the background without disrupting productivity. It verifies user presence passively and only takes action when policy conditions are met, such as inactivity, user absence, or detection of an unauthorized individual.
Can session behavior and alerts be customized?

Yes. Organizations can define policy-based controls for session duration, absence thresholds, automatic lock timing, and response actions. OLOID can also generate real-time alerts for security teams when absence violations or suspicious activity are detected, enabling faster incident response.
How does continuous authentication support compliance and remote work security?

Continuous authentication strengthens session integrity by ensuring that only the verified user remains logged in, whether in clinical, enterprise, or remote environments. Automatic lockouts, audit logs, and real-time monitoring help organizations meet access control and session management requirements across regulatory and security frameworks.
Making every day-in-the-life of frontline workers frictionless & secure!
Get the latest updates! Subscribe now!
Thank you! Your submission has been received!
Oops! Something went wrong while submitting the form.



