Passwordless authentication for BPO & contact center agents
Strengthening Security, Compliance, and Productivity for Remote and In-Office Agents.
In the BPO and contact center industry, securing customer data, maintaining regulatory compliance, and optimizing agent productivity are top priorities. Agents handle sensitive customer information daily, and traditional password-based systems introduce risks, especially in environments with high turnover. Passwords can lead to security vulnerabilities, especially when agents transition out of the organization, potentially exposing both company and customer data.
Quick, secure access tailored foragent workflows
.webp)
Eliminate Proxy Worker Risks
Facial recognition and RFID-based authentication verify each agent’s identity, reducing unauthorized access and improving accountability.
.webp)
Enhance Data Security for Agents
Geo-fencing, anomaly detection, and biometric verification protect customer data and meet data protection regulations, even in remote work settings.
.webp)
Streamline Supervisor Monitoring
OLOID’s real-time alerts, dashboards, and continuous authentication tools support effective supervisor oversight, helping to maintain quality and security across all agent interactions.
Why OLOID?
OLOID’s passwordless authentication platform is designed specifically for BPO environments, eliminating the need for passwords through facial recognition, RFID-based authentication, and presence detection. This approach not only streamlines access but ensures that agents are not exposed to any company or customer passwords, reducing the security risks associated with staff transitions. By seamlessly integrating with BPO workflows, OLOID empowers organizations to protect sensitive data, mitigate proxy worker risks, and ensure compliance with industry regulations like PCI-DSS.
- MFA Compliance Without Mobile Devices: Secure customer data access without relying on mobile devices or physical tokens, meeting PCI-DSS and other regulatory requirements.
- Reduced Security Risks During Staff Turnover: Agents are not exposed to passwords, minimizing the risk of data exposure when agents transition out of the organization.
- Mitigating Security Risks During Off-boarding: As agents are never exposed to company or customer passwords, it mitigates the risk of credential misuse, and simplifies off boarding.




.webp)

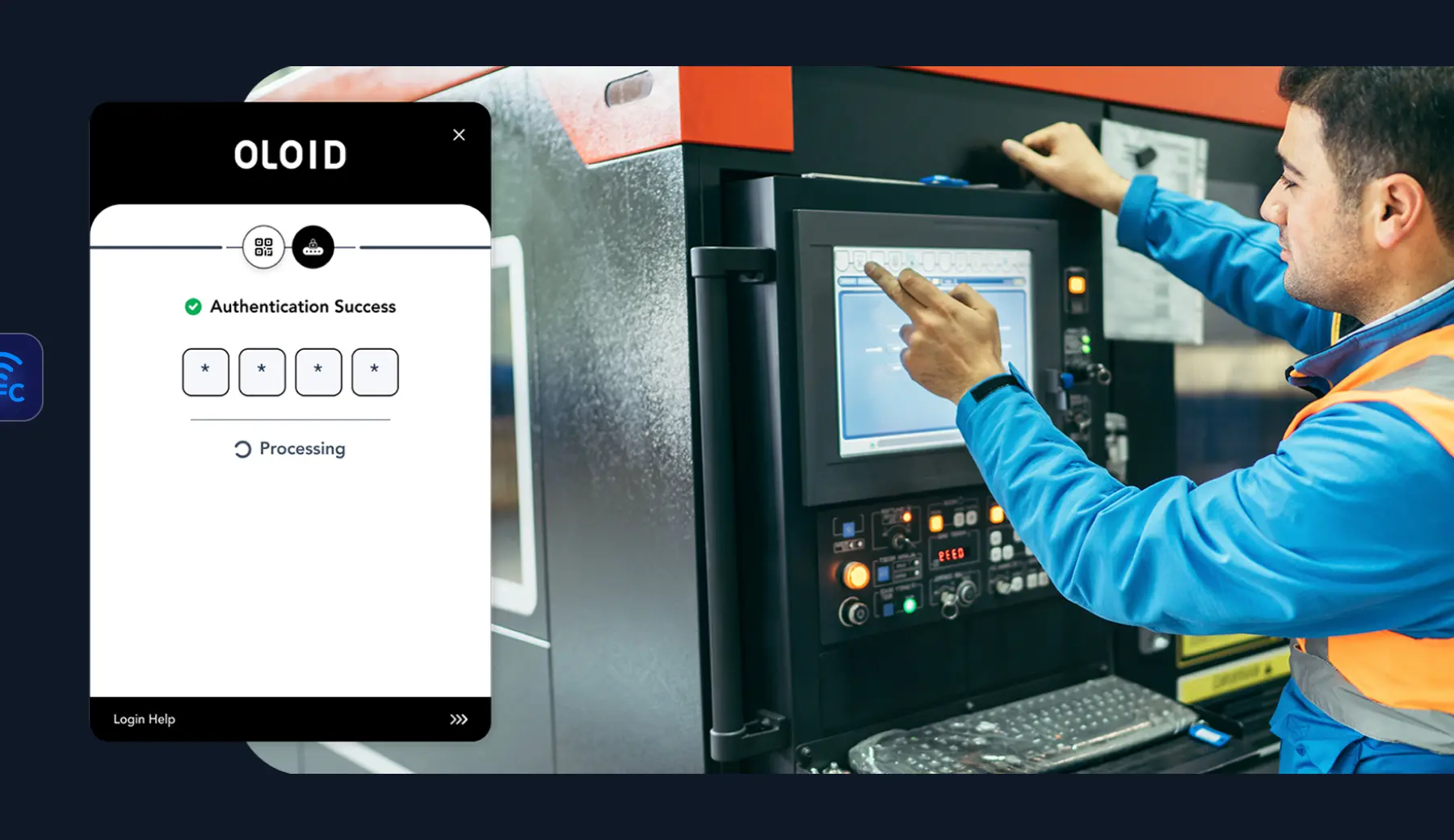
Seamless Login with Facial Recognition and RFID Access Card based MFA
OLOID’s facial recognition and RFID-based login options enable agents to quickly and securely access customer service applications and shared devices without needing passwords. This approach protects data while simplifying the login experience, allowing agents to focus fully on customer interactions and quality of service.

Compliance-Focused Authentication for Regulated Data Access
MFA Compliance Without Dependence on Mobile Devices or Hardware Keys
To meet regulatory requirements like PCI-DSS, OLOID provides a passwordless, multi-factor authentication solution based on facial recognition and RFID, removing the need for mobile phones or physical security keys, which are often impractical in BPO settings. This ensures that agents can securely access sensitive customer data, keeping compliance straightforward and reducing the administrative burden of managing authentication devices.

Geo-Fencing and Anomaly Detection for Remote Work Security
Data Security with Location-Based Access Controls
OLOID’s geo-fencing and geo-anomaly detection features allow organizations to enforce location-based access restrictions, ensuring that sensitive data is only accessible from approved regions. This is particularly valuable in remote work environments, where strict location-based controls help meet data protection laws and prevent unauthorized access.
.webp)
Continuous Presence Detection and Screen Lock for Secure Sessions
Automatic Screen Locking and Real-Time Supervisor Alerts
OLOID’s continuous presence detection technology automatically locks screens when agents step away and alerts supervisors to potential security issues, such as additional faces or unauthorized devices near workstations. This feature ensures that customer data remains secure and that supervisors have the necessary tools to monitor agent activity effectively, increasing both security and accountability.
Schedule a demo
Featured integrations
OLOID platform seamlessly integrates with your existing infrastructure for easy install & ongoing management.
Related posts

Continuous Authentication: What It Is, How It Works, Benefits & Best Practices
Continuous authentication represents a fundamental shift in identity security. Traditional login methods verify users once and grant lasting access. This approach leaves systems vulnerable to session hijacking and credential theft. This guide explores the definition, core components, implementation strategies, real-world applications, and best practices of continuous authentication. Learn how behavioral biometrics, contextual signals, and machine learning enable real-time identity verification.

Workforce Authentication: The Key to Securing Modern Workplaces
Modern workplaces face unprecedented cyber threats, with traditional password systems creating massive security gaps. This comprehensive guide explores workforce authentication fundamentals, from traditional methods to cutting-edge passwordless solutions. Learn about implementation challenges, compliance requirements, and best practices for securing your workforce.
Securing Shared Devices Without Shared Passwords
Shared devices are vital in frontline work, but shared passwords and legacy MFA can’t meet the demands of shift-based, high-turnover environments. Modern security needs contactless, passwordless solutions that scale, ensuring secure access, individual accountability, and fast ROI.
FAQs on passwordless authentication for BPO & contact center agents
How does OLOID prevent proxy worker and credential sharing risks?

OLOID eliminates usernames and passwords and replaces them with identity-based authentication factors such as face recognition, badges, NFC, QR codes, or PINs. Because agents do not know or share reusable credentials, each login is uniquely tied to a verified individual. This prevents proxy logins, credential sharing, and unauthorized reuse.
How does OLOID protect customer data and support PCI-DSS compliance?

By replacing traditional passwords with phishing-resistant, passwordless authentication, OLOID strengthens access controls for systems handling sensitive customer data. Integration with existing identity and SSO systems ensures secure authentication workflows that align with PCI-DSS requirements and enterprise data protection standards.
How does OLOID secure remote and hybrid contact center environments?

OLOID enforces strong, passwordless authentication regardless of location. Access policies and contextual controls ensure that only verified agents can access customer systems from approved devices and environments. This reduces the risk of unauthorized remote access and protects sensitive information outside traditional office settings.
How does presence detection improve agent session security and supervision?

OLOID’s presence detection continuously verifies that the authenticated agent remains at the workstation. If the system detects absence, multiple faces, or unrecognized individuals, it can automatically lock the session and trigger alerts to supervisors or administrators. This provides real-time visibility and helps prevent shoulder surfing, observation attacks, and unauthorized access.
How does OLOID reduce security risk in high-turnover contact centers?

In environments with frequent staff changes, OLOID centralizes provisioning and deprovisioning through integration with HR and identity systems. When an agent leaves, access is immediately revoked without needing to reset shared passwords or credentials. This reduces administrative overhead and significantly lowers the risk of lingering access or credential misuse.
Making every day-in-the-life of frontline workers frictionless & secure!
Get the latest updates! Subscribe now!
Thank you! Your submission has been received!
Oops! Something went wrong while submitting the form.





























