Authentication & Passwordless
Articles on how modern passwordless authentication is replacing passwords.

Featured
What is a YubiKey and How Does It Work? The Complete Guide
YubiKey is a hardware security key that uses cryptographic authentication instead of passwords. The blog highlights how traditional methods like passwords, SMS, and authenticator apps fail against modern threats like phishing and credential theft. The guide breaks down how a YubiKey works, including its secure chip, authentication flow, and supported protocols like FIDO2 and OTP. It compares YubiKey with other authentication methods to show why it offers stronger, phishing-resistant security. It also covers real-world use cases, enterprise deployment, and its limitations in frontline and shared device environments.

10 Multi-factor Authentication Trends to Watch Out for in 2026
Multi-factor authentication (MFA) is evolving to meet rising cybersecurity challenges. Emerging trends such as biometrics, behavioral and contextual authentication, AI-driven systems, and passwordless methods are making MFA more secure and user-friendly. These advancements aim to reduce friction, prevent breaches, and align with Zero Trust principles. As businesses and individuals adopt these modern MFA solutions, they strengthen their defense against increasingly sophisticated threats.

How to Use a Passkey Solution for Shared Devices: A Comprehensive Guide
Traditional passkeys fail in shared device environments because they're designed for 1:1 user-device binding, leaving frontline workers who can't use personal phones stuck with weak passwords on shared terminals. This guide explains how innovative shared device passkey solutions overcome WebAuthn limitations through multi-tenant credential stores and enterprise IAM integration, enabling phishing-resistant authentication for manufacturing, healthcare, and retail workers on shared workstations while maintaining individual accountability and FIDO2 compliance.

How Face Recognition Login Works in Manufacturing: A Complete Guide
Manufacturing workers lose valuable production time struggling with passwords while wearing PPE, leading to shared credentials on factory terminals that create compliance risks and endless IT support tickets. This guide demonstrates how face recognition login solves these challenges by working seamlessly with safety equipment, providing individual accountability for regulatory compliance, and delivering proven ROI through faster shift changes and reduced IT costs, all while integrating with existing systems like ADP, Workday, and Okta.

A Complete Guide to Passwordless MFA Without Mobile Devices
Traditional smartphone MFA fails in regulated industries due to safety restrictions and device bans. Learn seven deviceless authentication solutions - biometric scanners, hardware keys, badge systems, and proximity wearables - that provide enterprise security for frontline teams without requiring personal phones or creating compliance violations.
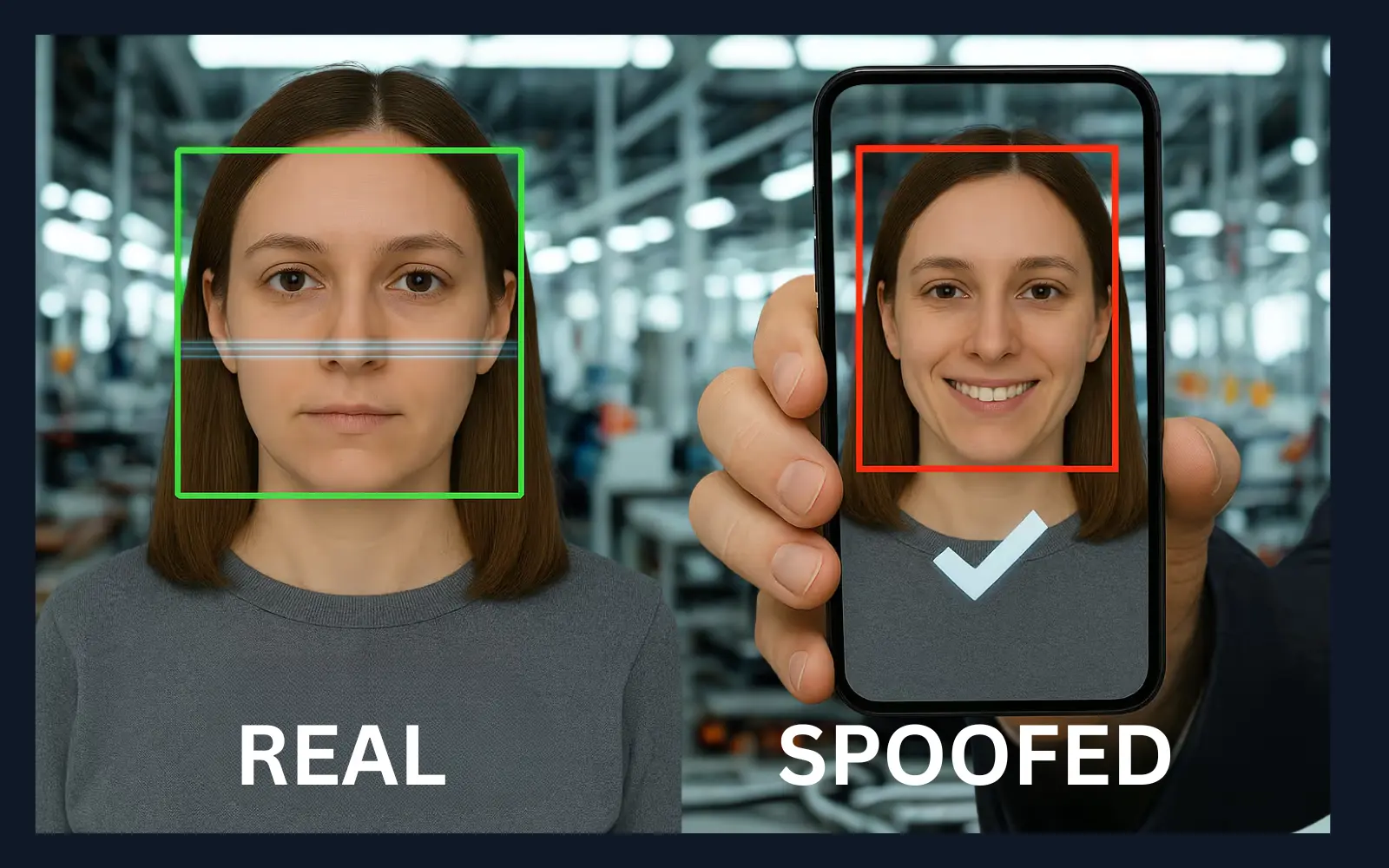
Liveness Detection Guide: Protecting Digital Identity 2026
Learn how liveness detection is revolutionizing digital identity verification in 2026. Discover the technology behind preventing spoofing attacks like deepfakes, photos, and masks. Understand its role in securing transactions, improving compliance, and enhancing security across industries such as finance, healthcare, and manufacturing.

Biometrics by the Numbers: Trends, Adoption & Challenges
This post explores how biometric technologies are transforming identity verification and data security. It highlights key statistics on adoption, market growth, and consumer trust. Gain insight into privacy, accuracy, and regulatory challenges shaping the future of biometrics.

Passwordless vs Traditional Logins: Which Is Better?
As cyber threats grow more advanced, traditional password systems struggle to keep up due to vulnerabilities like phishing and password reuse. Passwordless authentication—using biometrics, security tokens, or one-time codes—offers stronger security, a better user experience, and reduced IT overhead. While traditional methods are simpler to implement, passwordless solutions scale better and future-proof organizational security. A hybrid approach can ease the transition. With support from tech giants, passwordless is rapidly becoming the new standard in cybersecurity.

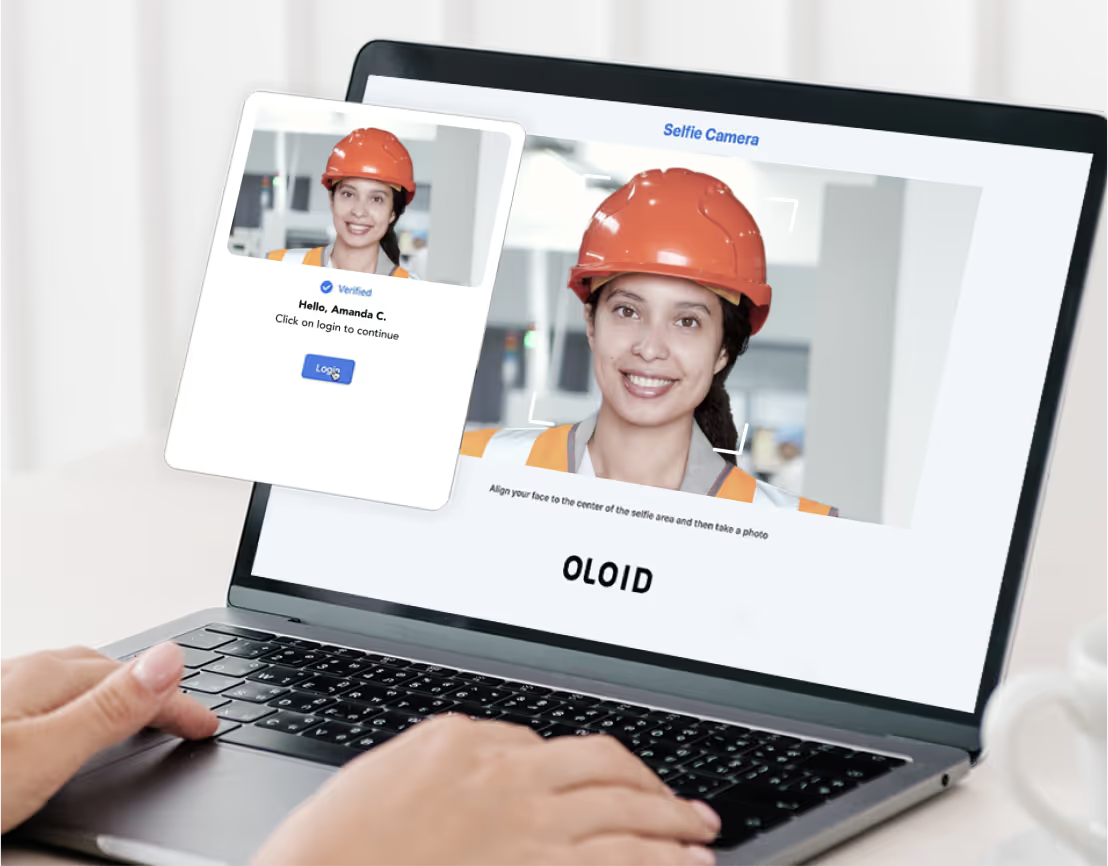
OLOID's Facial Recognition for Ethical, Passwordless Access
OLOID’s facial recognition is more than just tech; it’s built around ethics, consent, and inclusivity. It solves real workplace access challenges while protecting privacy and avoiding bias. With a focus on fairness and future-proofing against regulation, OLOID ensures that authentication works for everyone, safely and securely.
How OLOID Supports Deskless Workers Daily
OLOID offers a passwordless and usernameless authentication platform tailored for deskless and frontline workers, helping CISOs and CIOs reduce insider threats, improve workforce productivity, and strengthen cybersecurity. The platform integrates with SSO systems, simplifies onboarding, enables secure shared device access, and supports multi-factor authentication without requiring phones or hardware keys. With solutions like Cloud Key for physical access and Time Clock for attendance, OLOID enhances operational efficiency, minimizes IT support costs, and ensures compliance. It's designed for high-turnover environments and industries with strict safety and hygiene standards.

Why Passwords Are Obsolete and How Passwordless Works
This post explores why traditional passwords are becoming ineffective in protecting digital identities and how passwordless authentication is transforming security. It highlights the vulnerabilities and user frustrations tied to passwords while explaining modern alternatives like biometrics, security keys, and magic links. Learn how passwordless solutions enhance security, simplify access for frontline workers, and reduce IT overhead across organizations.

Secure Web Apps with Passwordless Authentication
This blog highlights the growing need for stronger security in web applications and introduces passwordless authentication as a superior alternative to traditional passwords. By using biometrics, magic links, or security tokens, it enhances security, user experience, and reduces IT costs. OLOID's deviceless MFA solution further extends these benefits to frontline workers using shared devices, offering secure access through face, PIN, access cards, or QR codes. The future of digital identity is passwordless—and OLOID is leading the way.

SSO vs MFA: What’s the Difference and Which One Do You Need?
This blog explains the key differences between SSO and MFA authentication technologies. SSO focuses on user convenience while MFA prioritizes security through multiple verification layers. Organizations achieve the best results by combining both technologies rather than choosing one over the other. Get practical implementation guidance and learn the combined benefits of enhanced security and improved user experience.

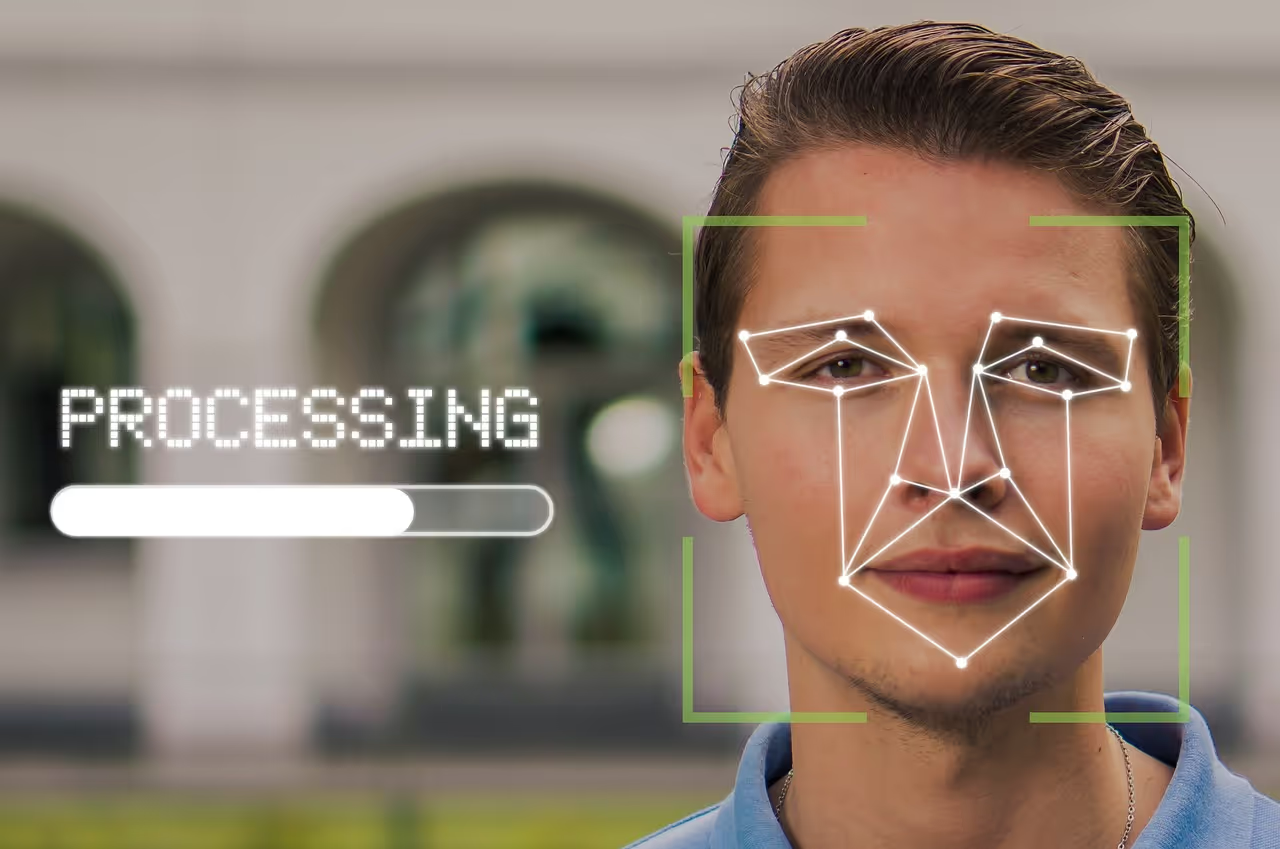
Advancing Security with Face-Based Authentication
Face-based authentication combines facial recognition with multi-factor authentication to offer a secure, convenient, and user-friendly login experience. By using unique facial features, it reduces the risks of password theft, improves user efficiency, and minimizes fraud. While it enhances security, organizations must also address privacy concerns, accessibility challenges, and accuracy limitations to ensure effective implementation.

Exploring FIDO vs FIDO2: Evolution in Secure Authentication
FIDO and FIDO 2 are modern passwordless authentication standards designed to replace traditional, vulnerable password systems. FIDO uses public-key cryptography and supports biometric and hardware key-based login, enhancing both security and user experience. FIDO 2 builds on this foundation with WebAuthn and CTAP, offering even greater interoperability, flexibility, and phishing resistance across devices and platforms. As cyber threats grow, adopting FIDO 2 helps organizations and individuals secure digital identities while simplifying access.

Integrating Passwordless Authentication into IT Strategy
This post explores the increasing significance of passwordless authentication in modern IT strategies as organizations seek stronger security and better user experiences. Discover different passwordless approaches, such as biometrics and cryptographic keys, along with their security, scalability, and cost-saving advantages, plus best practices for smooth integration. The post also details key challenges, emerging trends, and practical steps for enabling a secure and seamless authentication environment.

What Is FIDO Authentication and How Does It Work?
Passwords are costing your organization millions in resets and breach risks. Learn how FIDO authentication eliminates these vulnerabilities with cryptographic, phishing-resistant security. Explore step-by-step implementation strategies, real-world use cases across industries, and the measurable benefits of one-tap biometric login.

How do RFID cards work?
This guide explains what RFID cards are and how they function as contactless tools for secure identification and access. It covers the working principles of RFID cards, their benefits over traditional password-based systems, and common real-world applications across industries. Learn how to choose the right RFID card solution, compare them with mobile access, and explore their role in enhancing security and efficiency.

The Evolution of Authentication: Embracing Passwordless Security
This blog discusses the shift from traditional password-based authentication to passwordless security methods as a response to growing cybersecurity threats. Learn why passwords are now considered inadequate, how technologies like biometrics and multi-factor authentication offer safer alternatives, and the benefits of adopting these advanced solutions. Gain insights into practical steps for implementing passwordless systems and highlights their advantages in terms of security, user experience, and operational efficiency.

Facial Recognition in Law Enforcement: Security vs Privacy
This post explores the use of facial recognition technology in law enforcement, focusing on the debate between enhancing security and protecting privacy. It covers how the technology aids crime prevention, investigations, and public safety, while also addressing challenges like bias, privacy invasion, and regulatory gaps. The article emphasizes the need to balance these concerns and highlights innovative solutions that aim to align security with individual rights protection.

Facial Recognition and Data Privacy: Striking the Right Balance
This blog explores the growing role of facial recognition technology and the pressing need to balance its benefits with data privacy concerns. It examines major privacy risks such as biometric data misuse, misidentification, and lack of consent while highlighting innovative strategies like anonymization, privacy-by-design, and strong regulatory compliance. Gain insights into how businesses and policymakers can adopt responsible practices to ensure facial recognition technology is both effective and ethically implemented.

RFID vs NFC vs BLE: Best Access Tech for Your Business
This post explores the differences between RFID, NFC, and BLE technologies to help businesses choose the best access and connectivity solution. It explains how each technology works, compares their range, speed, security, and cost, and highlights ideal use cases for various applications. Gain insights into which option suits your needs for asset tracking, payments, IoT devices, or long-range communication.
Multi-Factor Authentication (MFA): A Complete Guide to Strengthening Security
Multi-Factor Authentication (MFA) enhances cybersecurity by requiring users to verify their identity through multiple methods—like biometrics, access cards, or PINs—making it harder for attackers to gain access. MFA reduces phishing risks, protects against password fatigue, improves compliance, and builds user trust. While challenges like user resistance, integration effort, and cost exist, the benefits far outweigh them. OLOID’s passwordless MFA solution offers a seamless, secure login experience—especially for frontline and mobile workers—by combining physical and digital authentication methods.
Biometrics vs Face Recognition for Identity Authentication
This blog explores the differences between biometrics and facial recognition technologies for identity authentication in modern access control systems. It explains how organizations are adopting these technologies for security, convenience, and contactless access in workplaces and industries. Gain insights into the strengths, limitations, and best-use cases of each approach to determine the most suitable authentication method for your organization.

Face-Based Authentication in Identity Verification Explained
Face-based authentication is rapidly transforming identity verification across industries by using biometric facial features for secure and seamless access. Common in smartphones, workplaces, airports, and healthcare, this contactless method enhances security, reduces fraud, and improves user convenience. From tracking attendance and locating missing persons to securing borders and reducing retail crime, face-based authentication is becoming integral to modern security frameworks. As adoption grows, it promises faster processes, accurate verification, and a more secure digital-first world.

The Passwordless Era: A New Shift in Security
This article explores the transition to passwordless authentication, a security shift eliminating traditional passwords in favor of more advanced methods like biometrics and multifactor authentication. Learn about the vulnerabilities of conventional passwords, the mechanics and benefits of passwordless solutions, and the urgent need for such innovation amid rising cyber threats and costs. Gain practical insights into improving digital security, enhancing user experience, and aligning with compliance requirements by adopting passwordless authentication.

Facial Recognition Tech: Uses, Impact & Growth Trends
This blog explores facial recognition technology, detailing its evolution, applications, and the growing role it plays across industries. Learn how it is transforming areas like security, law enforcement, retail, and personal device authentication while also addressing ethical concerns such as privacy, bias, and surveillance. The article also examines future growth trends, challenges to accuracy, and the importance of responsible implementation to maximize benefits while safeguarding individual rights.

What are the advantages and disadvantages of using Proximity Cards?
Proximity cards are contactless access control devices using RFID technology, widely adopted for their convenience, security, and ease of use. They offer benefits like improved employee access, accurate attendance tracking, and cost-effective scalability. However, challenges such as limited range, skimming risks, card cloning, and system dependency must be considered. When properly implemented and maintained, proximity cards provide a secure and efficient solution for controlling access in various organizational settings.

Facial Authentication vs Facial Recognition: Key Differences
This blog explores the differences between facial authentication and facial recognition, two similar yet distinct technologies that analyze facial features using computer algorithms. It explains how facial authentication focuses on one-to-one identity verification, while facial recognition identifies individuals from larger databases or crowds. Gain insights into their unique applications, accuracy factors, privacy concerns, and the ethical debates surrounding their use.

Biometric ID Guide: Secure Your Digital Identity
Biometric identification uses unique physical or behavioral traits like fingerprints, facial features, or voice to verify identity. Common methods include facial recognition, fingerprint scanning, and voice recognition. These solutions offer enhanced security, accuracy, and convenience compared to traditional passwords. As costs decline, even small businesses can adopt biometric systems to improve access control and protect against threats.

Biometric Access Control: Types, Benefits & Risks
This blog explores biometric access control systems, which use unique biological features like fingerprints and facial recognition to verify identity and secure access. It explains different types of biometric technologies, their advantages and drawbacks, and how they are applied across industries like finance, healthcare, and law enforcement. Learn how to choose the right biometric system for their needs, balancing security benefits with privacy and implementation challenges.
Making every day-in-the-life of frontline workers frictionless & secure!
Get the latest updates! Subscribe now!



