Biometrics vs Face Recognition for Identity Authentication
This blog explores the differences between biometrics and facial recognition technologies for identity authentication in modern access control systems. It explains how organizations are adopting these technologies for security, convenience, and contactless access in workplaces and industries. Gain insights into the strengths, limitations, and best-use cases of each approach to determine the most suitable authentication method for your organization.
Secure access control is of primary importance as organizations worldwide transition back to the workplace after remote work. The global COVID-19 pandemic has reshaped security needs, emphasizing the necessity for contactless features integrating biometric and facial recognition technologies.
Recent technological advancements support a cloud-based access control system, enabling any smart device to function as an access control reader. By 2026, the access control market is projected to grow to a $13.1 billion USD industry, with an expected CAGR of 8.7%.
According to Future Market Insights, the "rising adoption of security and access control devices along with the rising trends towards multi-modal or hybrid biometric systems are accelerating the growth of the fingerprint biometrics market." The fingerprint biometrics market is expected to reach US $67.1 Billion by 2023.
Passwordless authentication is the most preferred type of identity authentication among consumers, with 63% expressing a preference for passwordless authentication methods (Source: Mastercard Biometric Authentication Survey 2022).
Multi-factor authentication (MFA) stands as the most effective way to prevent unauthorized access to accounts, with MFA reducing the risk of successful account takeover attacks by 99% (Source: Microsoft Security Intelligence Report 2022).
Biometric authentication is the most secure type of identity authentication, with biometric authentication systems achieving accuracy rates of over 99% in many cases (Source: National Institute of Standards and Technology).
Biometrics Access Control
Biometrics access control combines advanced security with unparalleled convenience. It grants access based on the user's unique biometric traits, eliminating the risk of losing critical access control objects.
- Fingerprint Access: Synonymous with biometrics, fingerprint access control is widely recognized. It is one of the oldest biometrics used for signing and authenticating confidential documents. Modern systems are cost-effective and widely produced, even integrated into smartphones for owner authentication.
- Palm Vein Biometrics: A relatively new technology, palm vein biometrics identifies users based on vein and blood flow patterns in their palms. As an internal biometric, it offers higher security. Reverse engineering palm veins without advanced hacking systems is extremely challenging. It boasts the lowest false rejection and acceptance rates among biometric technologies.
- Iris Biometrics: This system authorizes users based on the unique pattern of their iris. It captures a higher number of data points, making it one of the most accurate biometric systems. To enhance security, both eyes can be scanned.
- Voice Biometrics: Useful in call centers, voice biometrics identifies individuals based on their voice. While helpful, voice can be easily duplicated. For advanced security, a combination of voice recognition and other biometrics is recommended.
- Handwriting: Common in judicial and banking systems, users are authorized based on their signatures. Touchscreen devices can be modified for handwriting recognition, primarily used as a low-level security measure.
Pros of Biometrics
- Unique to the user
- Difficult to duplicate
- Easy permission management
- Accurate access control
- No need to remember access codes
- Always available
- Efficient and quick access
- Reduced need for security personnel
- No replacement cost
Cons of Biometrics
- Susceptible to wear and damage
- Changes in fingerprints due to cuts or bruises can make identification difficult
- Requires physical contact, which can be unhygienic
- Vulnerable to duplication through 3D printing and fingerprint analysis technologies
- Iris scanners can capture images from a distance, raising privacy risks
- Voice-based systems may not address privacy concerns and are less effective in noisy environments
- Inconsistent signatures can make authorization challenging
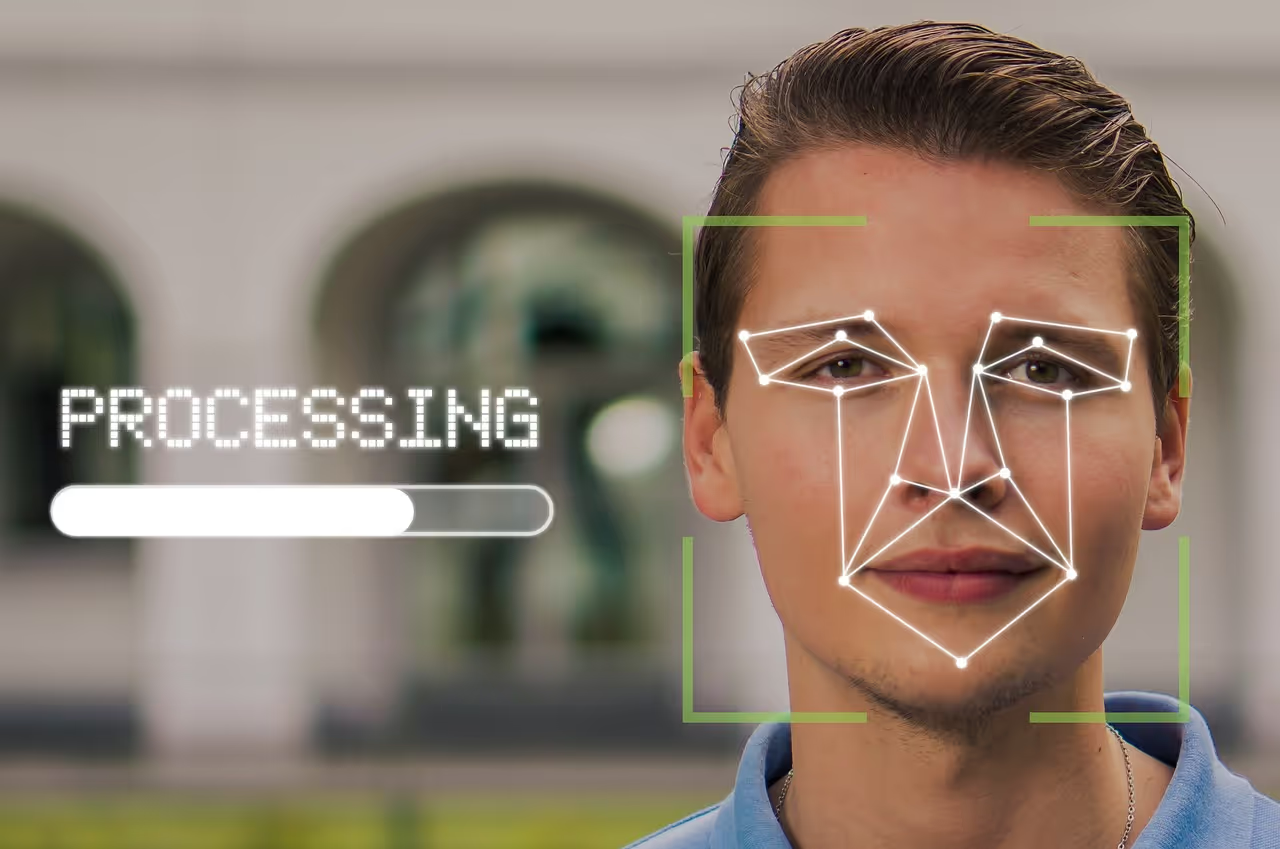
Facial Recognition-based Access Control
Facial recognition is another widely used biometric access system. It authorizes individuals based on facial vectors and features. For instance, iPhones use Face ID for heightened smartphone security, surpassing fingerprint-based authentication. The banking sector has also adopted facial recognition for Electronic Know Your Customer (e-KYC) and employee attendance. These systems can be adapted to verify health measures, such as using face masks or body temperature scanning. Smart advertising systems additionally employ facial recognition for targeted advertising.
Pros of Facial Recognition
- Requires minimal interaction
- Completely contactless
Cons of Facial Recognition
- Facial expressions may lead to recognition errors
- Facial accessories may result in authentication failure
- Facial features can be captured from far away, making the system vulnerable to security risks
- Privacy concerns include recognition without consent
The right security authentication system for your organization depends on your security needs. To maximize authorization when restricting access to heavy machinery, confidential documents, financial vaults, or proprietary research, consider a combination of biometrics like palm-vein analysis, iris scans, and more. Facial recognition automates attendance and payroll management, eliminating the need for manual checks. In many organizations, biometrics and facial recognition technologies are used in parallel depending on the security and vulnerability risks involved.
Which Access Control is Best for Your Organization?
Biometrics-based systems are useful for authenticating users for restricted access. Employees can be assigned different levels of access to the same center based on their permissions, eliminating the need for key cards, strip cards, or passwords to enable restricted access.
ePassports are now widely used to prevent counterfeit and duplicate documents. Biometric technology has simplified attendance and company payroll systems. Similarly, financial institutions incorporate biometrics involving bodily features to ensure customer authenticity.
Facial recognition systems are useful when identification is more critical than authentication, as in law enforcement. Accurate facial mapping technologies can identify a person even with makeup.
Facial emotion recognition has significantly enhanced the use of facial recognition systems. It is instrumental in marking attendance during meetings since a single image can identify all the participants. The incorporation of AI technology results in better facial recognition algorithms that can continuously learn. They are used to quickly locate missing people based on CCTV footage.
Various countries and institutions use FR systems for identification, authentication, and authorization for purposes beyond granting access. For example, China plans to employ facial recognition systems for its social credit system. Airports use facial recognition to expedite security procedures. Voter identification in Brazil's electoral systems also relies on facial recognition.



Get the latest updates! Subscribe now!


