Workforce & Frontline Security
Articles on securing access for frontline workers in Healthcare, Manufacturing, Retail, etc.

Featured
What is Endpoint Security? A Complete Guide for Modern Organizations
Endpoint security has moved well past antivirus. With 90% of successful cyberattacks originating at endpoint devices, every laptop, shared workstation, server, and IoT sensor on your network is a potential entry point. This guide breaks down what endpoint security is, how EPP, EDR, and XDR work together, and why Zero Trust and compliance requirements make device-level protection non-negotiable. It also addresses the specific risks that shared-device and frontline environments introduce, where standard endpoint tooling consistently falls short.

Top 10 Challenges Faced by Frontline Workers and How to Overcome Them
Frontline workers encounter unique obstacles that impact their performance, satisfaction, and well-being. This comprehensive guide explores the top ten challenges faced by frontline workers across industries. It includes workplace stress, lack of recognition, limited resources, safety risks, and retention issues. Each challenge is accompanied by practical, actionable solutions organizations can implement to support their workforce and drive operational success.

Workforce Authentication: The Key to Securing Modern Workplaces
Modern workplaces face unprecedented cyber threats, with traditional password systems creating massive security gaps. This comprehensive guide explores workforce authentication fundamentals, from traditional methods to cutting-edge passwordless solutions. Learn about implementation challenges, compliance requirements, and best practices for securing your workforce.

How Passwordless Login Solves Access Challenges for Factory Workers with Diverse Language Backgrounds
Multilingual factory teams struggle under English-only password systems that slow access, drive risky credential sharing, and overwhelm IT with resets. Passwordless login using facial recognition, badges, and QR codes transcends language barriers, delivering sub-second authentication, stronger security, improved worker productivity, better compliance, and lower IT costs while integrating seamlessly with existing factory systems across all shifts and facilities.

How to Configure Microsoft External Domain for Frontline Workers: Best Practices and Implementation
Microsoft Entra ID works well for office employees but struggles with frontline workers who share devices, can't use personal phones for MFA, and include high-turnover contractors needing temporary access. This guide explains how to configure external domains in Microsoft Entra ID to extend authentication to frontline staff, covering setup procedures, conditional access policies, automated lifecycle management, and integration with physical access system.

How Can Manufacturing Facilities Enable Unlimited Users on Shared Devices: A Guide
Manufacturing facilities lose productivity to password bottlenecks during shift changes and per-user licensing costs. This guide covers unlimited user authentication solutions using face recognition, badge tap, and NFC methods that eliminate passwords, reduce IT burden, and enable seamless access for thousands of workers on shared devices.

The Security Risks of Shared Passwords in Manufacturing and How Passwordless Prevents Them
Generic credentials and sticky-note passwords create massive security gaps in manufacturing environments. This comprehensive guide covers the business risks of shared logins, why they persist despite vulnerabilities, and how modern passwordless authentication delivers individual accountability while working seamlessly with existing industrial systems and workflows.

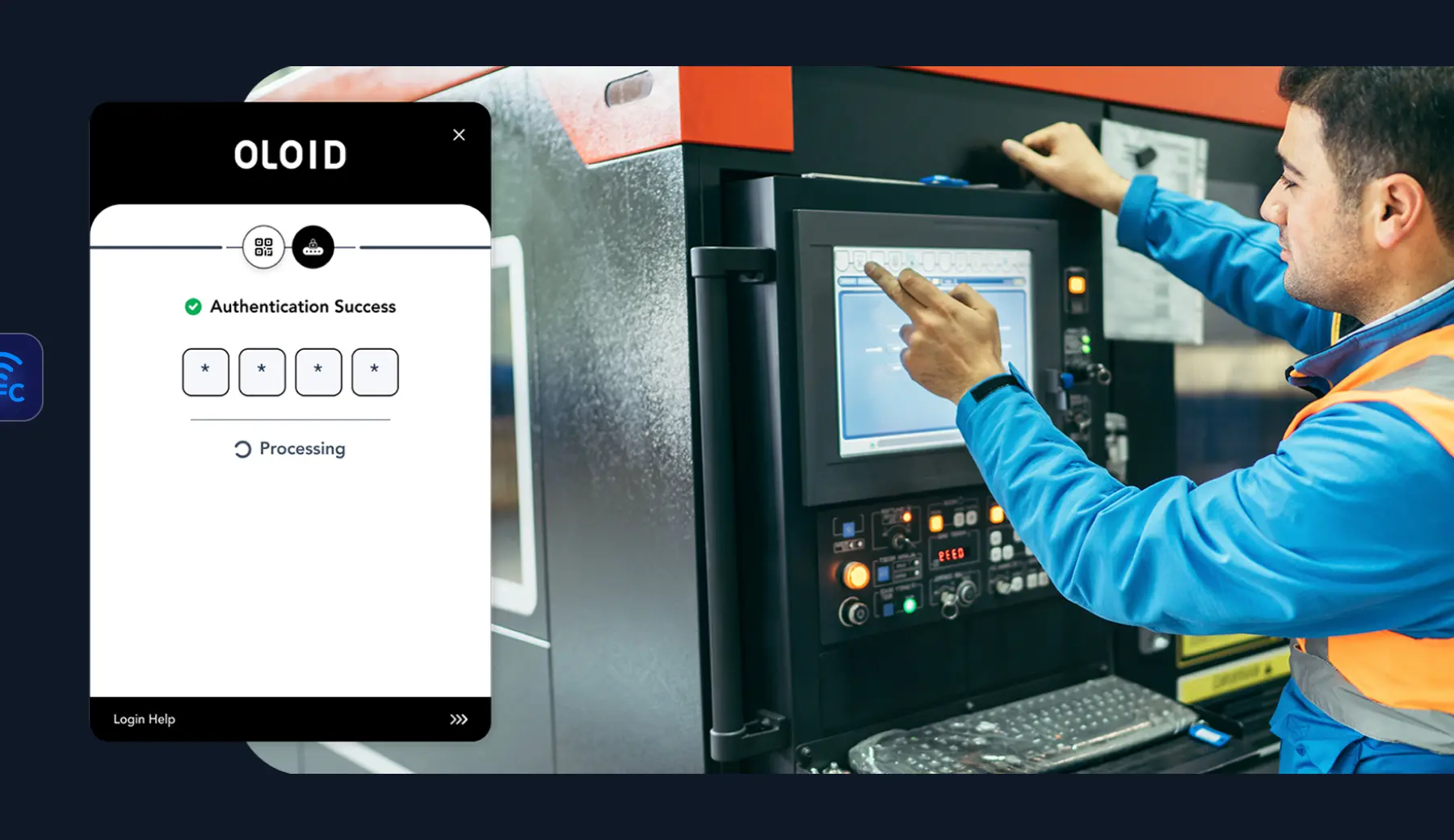
The Complete Guide to Frontline IAM for Manufacturing
Manufacturing facilities struggle with shared passwords, authentication delays, and compliance gaps on factory floors. This guide explores specialized Frontline IAM solutions that enable seamless, secure access for industrial workers while integrating with OT systems and delivering measurable productivity gains.
Securing Shared Devices Without Shared Passwords
Shared devices are vital in frontline work, but shared passwords and legacy MFA can’t meet the demands of shift-based, high-turnover environments. Modern security needs contactless, passwordless solutions that scale, ensuring secure access, individual accountability, and fast ROI.

Onboarding Deskless Workers: Go Passwordless for Security
This blog explores how going passwordless can transform the onboarding process for deskless workers by enhancing security and simplifying access. It explains the challenges traditional methods face—like limited device access, time constraints, and password vulnerabilities and how passwordless authentication solves them through biometrics, tokens, and multi-factor authentication. Learn the security benefits, ROI advantages, and best practices for implementing passwordless solutions to create a faster, safer, and more user-friendly onboarding experience.

Top 11 Authentication Challenges Frontline Workers Face Using Shared Devices
Frontline workers in manufacturing, retail, healthcare, and other deskless environments often struggle with authentication challenges, including PPE interference, forgotten passwords, limited MFA options, language barriers, and fragmented admin systems. These issues slow down workflows, increase security risks, and reduce accountability on shared devices. OLOID solves these challenges with a frictionless, passwordless authentication approach using facial and palm biometrics, access badges, and passwordless SSO.

Shared Devices: How Frontline Workers Use Them to Authenticate
This post explains how frontline workers use shared devices like tablets, kiosks, and computers to access work systems securely. It highlights key authentication methods such as biometrics, smart cards, and role-based access control for convenience and safety. Learn how OLOID’s Passwordless Authenticator simplifies login with facial recognition and MFA, improving compliance and efficiency.

Tyson Foods: How OLOID and Okta Transformed Frontline Login
At the recently concluded identity event; Oktane22, OLOID successfully presented a unique solution of converging the physical identity with digital credentials to give a passwordless means to deskless workers to login into employee applications and other interfaces.
Making every day-in-the-life of frontline workers frictionless & secure!
Get the latest updates! Subscribe now!



