The Passwordless Era: A New Shift in Security
This article explores the transition to passwordless authentication, a security shift eliminating traditional passwords in favor of more advanced methods like biometrics and multifactor authentication. Learn about the vulnerabilities of conventional passwords, the mechanics and benefits of passwordless solutions, and the urgent need for such innovation amid rising cyber threats and costs. Gain practical insights into improving digital security, enhancing user experience, and aligning with compliance requirements by adopting passwordless authentication.

The traditional password-based authentication system is challenging today’s digital landscape. While it offers security to our online accounts, it also requires us to manage multiple complex passwords, risking data and digital safety. The Verizon data breach incident report for 2022 states that human error accounts for 82% of all attack vectors, including social engineering, phishing, and mistakes.
A 2023 study by the National Cyber Security Alliance, found that 52% of Americans reuse the same password for multiple accounts, significantly increasing the risk of compromise if one account is breached.
A shift towards passwordless authentication is emerging. This approach seeks to enhance security by removing passwords. This blog delves into passwordless authentication and its benefits.
Limitations of password authentication
Using passwords online has its challenges. Here are some issues with the conventional password method:
- Weak passwords: Employees often create passwords that are easy to remember but simple to crack, like ‘ilovefamily’ or birthdays. This exposes corporate accounts to brute-force attacks.
- Password reuse: Reusing passwords for multiple accounts can lead to security breaches, amplifying the risk of shared passwords in manufacturing and other environments.
- Phishing: Hackers use phishing to trick individuals into revealing passwords, risking company data.
- Insider threats: Malicious employees can misuse their access, compromising security.
- Complexity and effort: Managing multiple passwords can be stressful, leading some to adopt unsafe practices like sharing or noting them down.
- Support costs and account lockouts: Lost passwords can increase IT support costs.
- Shared account security threats: Monitoring actions and ensuring accountability are tough when multiple employees use the same credentials.
Below is a visual representation of Password Weaknesses:
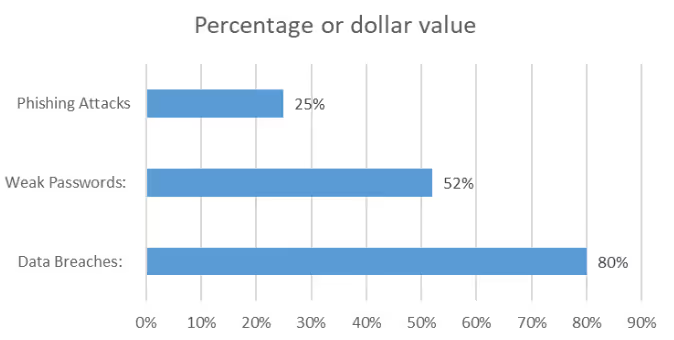
The above bar graph paints a concerning picture of the limitations surrounding password-based authentication. Each bar highlights a significant vulnerability:
- Data Breaches: A staggering 80% of breaches involve stolen credentials, showcasing the ease of compromising passwords.
- Weak Passwords: Shockingly, 52% of Americans reuse passwords, creating a domino effect if one account falls victim.
- Cost of Data Breaches: The average cost of a breach is a hefty $4.24 million, with password-related incidents playing a major role.
This emphasizes the urgent need for exploring more robust and secure authentication methods.
What is passwordless authentication?
Passwordless authentication is a forward-thinking security method that eliminates the traditional reliance on passwords. Doing so addresses some of the most common vulnerabilities associated with password use, such as weak password choices and reuse. The advantages of this approach are manifold, including a significant reduction in password-related risks and an enhanced user experience, as users no longer need to remember or manage multiple passwords. Furthermore, this method is adaptable; its implementation and features can vary, tailored to the specific requirements of different platforms or services. As cyber threats evolve, passwordless authentication is a testament to the innovative solutions developed to counteract them.
How does passwordless login work?
- Signing in with biometrics: Biometric authentication uses unique biological traits like fingerprints or voice for verification.
- Two-factor (2FA) and multi-factor (MFA) authentication: These methods combine multiple elements for authentication, reducing password dependency. Examples include:
OTP: Users receive a code via SMS or email for authentication.
Push Notification: Users approve authentication requests sent to their devices.
Security Tokens: Generate unique authentication codes.
Smart Card: Contains cryptographic keys for authentication. - Public Key Infrastructure (PKI): PKI uses public and private cryptographic keys for authentication.
- Authentication Via Mobile Device: Mobile devices offer various verification methods: Mobile Authenticator Apps – Generate OTPs or QR codes, Mobile Device Biometrics – Use fingerprint sensors or facial recognition.
- Fast Identity Online (FIDO) standards: FIDO supports password-free authentication using biometrics or hardware-based methods.
- QR code authentication: Employees scan a QR code for identity verification.
- Behavioral biometrics: This method uses unique user behaviours like typing speed for authentication.
Why is passwordless authentication important?
According to Cybersecurity Ventures, the global cost of cybercrime is projected to escalate to $10.5 trillion by 2025, a significant rise from $3 trillion in 2015. These expenses include data damage, financial losses, diminished productivity, intellectual property breaches, embezzlement, fraud, business disruptions post-attack, forensic investigations, and the restoration of compromised systems. Additionally, the intangible cost of reputational damage should be considered. Given these alarming projections, enhancing your security measures, such as adopting passwordless authentication, becomes imperative. Passwordless authentication offers:
- Enhanced security – Reduces unauthorized access and potential security incidents.
- Password risk reduction – Minimizes risks from reused or weak passwords.
- User experience enhancement – Simplifies the login process, boosting productivity.
- Cost savings – Reduces IT support costs and potential legal fees.
- Compliance and regulatory alignment – Meet data privacy and security regulations.
- Flexibility and scalability – Integrated into various IT environments.
- Better auditing – Links user activities to authentication events, aiding in audits.
Conclusion
Passwordless authentication enhances security, user experience, and compliance and represents a proactive approach to the evolving challenges of the digital age. As cyber threats become more sophisticated, traditional security measures often must catch up. Passwordless authentication paves the way for a more secure future by addressing the escalating costs and consequences of cybercrime. Embracing this technology is a step towards robust security, ensuring that individuals and organizations are better protected in an increasingly interconnected world.
Learn more about OLOID's Passwordless solution!
FAQs
1. What is passwordless authentication?
It’s a method that doesn’t rely on traditional passwords, using alternatives like biometrics for verification.
2. How does it enhance security?
It reduces password-related risks, offering more robust authentication methods.
3. What benefits does it offer for user experience?
It simplifies the login process and reduces password management stress. You can read more about the benefits and challenges related to passwordless authentication in our blog: Exploring the mechanics of Passwordless Authentication: How does it work?
4. What impact does it have on compliance?
It often aligns with data protection regulations.



Get the latest updates! Subscribe now!


