Identity & Access Management
Articles on managing identity and access across complex, shared-device environments.

Featured
Why Shared Devices Break Traditional IAM (And What Comes Next)
Every IAM system sold in the last two decades was built on a quiet assumption: one person, one device. On the frontline, that assumption has never been true.

Care Without Friction: How Verified Trust is Modernizing Clinical Identity
OLOID and Ping Identity's Verified Trust for Clinical Workforce replaces legacy identity infrastructure with a cloud-native framework built for modern care. Verified onboarding cuts enrollment from days to minutes, with portable credentials that travel across facilities. Passwordless Tap-and-Login delivers seamless access to shared workstations and EHRs, with stepped-up assurance only when needed. Self-service recovery closes a leading healthcare attack vector.

Passkey Implementation: A Practical Guide for Engineering Teams in 2026
Most engineering teams know passkeys work. The harder question is how to ship them in production without stalling on the details that actually matter. This guide walks through how passkeys compare to your existing auth stack, the build vs. buy decision, and how to design an account recovery flow that does not reintroduce risk. It also covers a phased rollout approach and why standard passkey assumptions break down in shared device and frontline environments.

How to Evaluate, Strengthen, and Future-Proof Your Identity Provider Security
Identity provider security governs every authentication decision an organization makes: who gets in, what they can access, and whether the system granting that access can itself be trusted. When IdP security is strong, credentials stay centralized, access is auditable, and attackers have no easy path in. When it is weak or poorly configured, a single compromised IdP hands attackers authenticated access to every connected application at once. This guide covers how identity providers work, what securing them actually requires, where most deployments leave gaps, and why environments with frontline workers and shared workstations demand a different approach to IdP security altogether.

What is Identity Proofing? A Complete Guide
Identity proofing governs the foundational question every access decision rests on: Is this person actually who they claim to be? When proofing runs well, only verified individuals get credentials, onboarding is secure, and account recovery cannot be exploited. When it runs poorly, synthetic identities slip through, help desk attacks succeed, and unauthorized access goes undetected for months. This guide covers the NIST proofing process, key verification methods, compliance obligations, and what identity proofing looks like when traditional verification flows break down.
What is User Provisioning and Deprovisioning?
Provisioning and deprovisioning govern the full identity lifecycle, from the moment a user gets access to the moment that access is removed. When these processes run well, the right people get in, and former employees get out, automatically and immediately. When they run poorly, orphaned accounts, privilege creep, and credential exposure fill the gap. This guide covers the JML framework, SCIM automation, compliance obligations across GDPR, HIPAA, and SOX, and the metrics that tell you whether your program is actually working.
What Is LDAP? How It Works and When to Use It
LDAP is the open, vendor-neutral protocol that enterprises have relied on for over 30 years to store user credentials, authenticate identities, and authorize access to resources. It organizes directory data in a hierarchical tree structure and supports two authentication methods: simple authentication and SASL. While LDAP remains foundational for legacy applications, Linux servers, and on-prem infrastructure, its plain-text default transmission and on-prem design create real security and scalability challenges.
RBAC vs ABAC vs PBAC: The Complete Guide to Access Control
RBAC, ABAC, and PBAC are the three primary access control models organizations use to govern who can access what. RBAC is simple and role-driven. ABAC is dynamic and context-aware. PBAC centralizes access logic into organization-wide policies. Most mature organizations layer all three rather than relying on one model alone. Choosing the wrong model, or inheriting one without evaluating it, creates security gaps that compound silently over time. In environments where shared devices and rotating workforces are the norm, the stakes of that decision are even higher.
.webp)
Policy-Based Access Control (PBAC): How It Works and Why It Matters
Policy-based access control is a dynamic authorization model that governs access through centrally defined policies combining user roles, resource attributes, actions, and environmental context. Unlike RBAC, which assigns permissions at the role level, PBAC evaluates every access request in real time against the full context of who is asking, what they want, and under what conditions. While PBAC delivers significant gains in security, auditability, and compliance alignment, it requires disciplined policy governance and careful testing before rollout.
What Is Just-in-Time (JIT) Access? A Complete Guide
Just-in-time access ensures that user access is granted only when needed, instead of relying on permanent access that stays active unnecessarily. It replaces traditional access control methods by introducing time access and moving toward zero standing access across systems. With JIT access, users request temporary access to specific resources such as access to production or other sensitive systems. Access is approved based on defined access control policies and is automatically revoked once the task is completed. This approach helps reduce unnecessary access and minimizes the risk of unauthorized access to privileged accounts.

What is Just-in-Time Provisioning? How It Works & When to Use It
Just-in-time provisioning is a modern approach to user account creation that eliminates delays by provisioning users at login instead of in advance. It relies on identity providers and SSO workflows to assign access instantly based on real-time identity data. While JIT provisioning improves onboarding speed and reduces IT workload, it does not handle the full identity lifecycle. Organizations often combine it with SCIM provisioning to manage updates and deprovisioning.

What is Least Privilege Access? Definition, Benefits, and Implementation
Least privilege access is a security principle that ensures users, applications, and systems receive only the minimum permissions required to perform their tasks. By limiting unnecessary access rights, organizations reduce their attack surface and lower the risk of privilege misuse or credential compromise. The approach helps prevent attackers from escalating privileges or moving laterally across systems after a breach. Least privilege is also a foundational component of modern zero trust security and identity access management strategies.
.webp)
What is Cloud Identity and Access Management (IAM)? A Complete Guide
Cloud identity and access management plays a central role in modern cloud security by verifying identities and controlling access across cloud environments. As enterprises adopt more cloud services, a well-designed IAM system enhances security through role-based access control, lifecycle management, and continuous monitoring while closing gaps in identities and access across frontline and shared environments.
.webp)
What is Zero Trust Network Access? A Complete Guide for Modern Enterprises
This guide explains Zero Trust Network Access (ZTNA), why traditional VPN-based security falls short, and how identity-driven access works in modern enterprises. It walks through ZTNA architecture, core principles, deployment models, and real-world use cases. The article highlights how ZTNA limits lateral movement and secures remote, cloud, and shared environments. It also shows how OLOID strengthens Zero Trust in shared workstation scenarios with continuous identity assurance.

Digital Identity Verification: A Complete Guide to Remote Identity Proofing
Digital Identity Verification enables organizations to confirm user identities remotely without physical presence or passwords. Businesses implement this technology to prevent fraud, accelerate onboarding, and meet global KYC/AML compliance requirements. This guide explores verification methods, implementation strategies, real-world applications, and best practices for success. Compliance officers, fintech executives, and security teams gain actionable frameworks for deploying robust identity verification across digital channels.

What is SCIM? The Complete Guide to System for Cross-domain Identity Management
SCIM, or System for Cross-domain Identity Management, is an open standard protocol that automates user provisioning and deprovisioning across cloud applications. This blog explains how SCIM eliminates manual identity management tasks, reduces security risks, and streamlines employee lifecycle workflows. Learn the implementation strategies, real-world use cases, solutions to common challenges, and best practices for deploying SCIM effectively in your organization.

Federated Identity Management: Complete Guide to Secure Cross-Domain Authentication
Federated Identity Management enables secure authentication across multiple organizations without creating separate accounts for each system. This blog explores how FIM works, key protocols like SAML and OAuth, implementation steps, real-world use cases, and best practices. Learn how enterprises use federation to reduce password fatigue, enhance security, and streamline access across cloud applications and partner ecosystems.

LDAP vs ADFS: Differences, Use Cases, and How to Choose the Right Approach
LDAP and ADFS represent fundamentally different approaches to enterprise authentication and identity management. LDAP provides directory-based authentication for on-premises systems, while ADFS enables federated identity with single sign-on capabilities. This guide compares architectural differences, protocol support, and use cases for both systems. Learn when each approach fits best and how modern identity platforms bridge traditional and cloud-native authentication requirements.

Credential Rotation: What It Is, Why It Matters, and How to Implement It
Credential rotation systematically replaces passwords, keys, and tokens to limit exposure from compromised credentials. Organizations face growing risks from static credentials that attackers exploit for unauthorized access. This guide explains rotation concepts, benefits, implementation steps, and automation strategies. Learn the best practices for rotating different credential types and building enterprise policies that strengthen security posture.
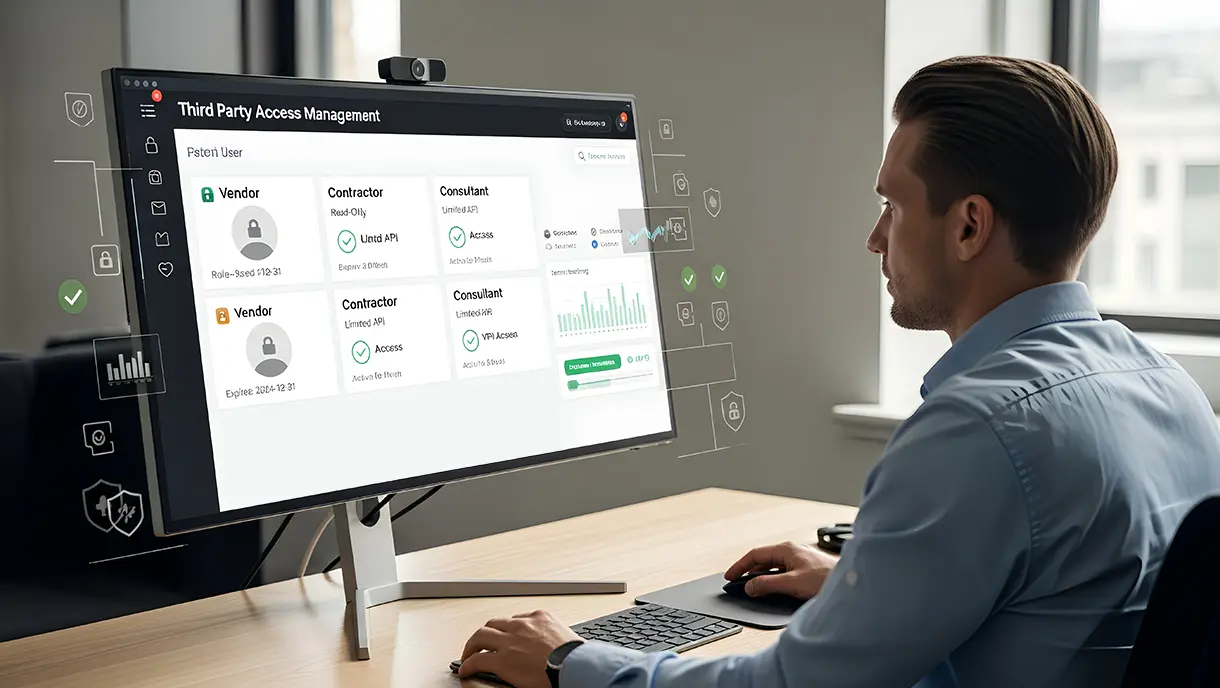
Third-Party Access Management: A Complete Guide to Secure Vendor Access
Third-party access management governs how external vendors, contractors, and partners access internal systems and data. Organizations face growing risks from uncontrolled vendor privileges, making structured access policies essential. This blog covers risk factors, implementation strategies, and security best practices. You'll learn how to balance business needs with robust protection for your critical assets.

Zero-Trust Implementation Guide: Steps, Policies, & Best Practices
Zero-Trust Implementation transforms traditional security by continuously verifying every access request. Organizations adopt this model to protect against modern threats like credential theft and lateral movement. This guide provides practical steps, technical architecture insights, and real-world use cases. Enterprise security teams gain actionable frameworks for deploying Zero-Trust across hybrid environments.
.webp)
Authentication Logs: What They Are, How They Work, and Why They Matter
Authentication logs provide critical visibility into every access attempt across your digital infrastructure. These records capture login events, failed attempts, and user behavior patterns that reveal security threats. This blog explores what authentication logs capture, why they matter for security, and how to manage them effectively. Learn log types, analysis techniques, management best practices, compliance requirements, and tools that strengthen your security posture.

What Is Access Control? Definition, Workflow, Models & Real-World Use Cases
This comprehensive guide explores access control as a critical security framework for protecting digital and physical resources. It covers fundamental definitions, various control models like RBAC and ABAC, implementation workflows, and real-world applications. You'll discover best practices for secure deployment, common challenges organizations face, and emerging trends shaping the future of access management.

Workforce Identity and Access Management Explained: Framework, Benefits, and Best Practices
Workforce Identity and Access Management (IAM) is the foundation of modern enterprise security. It controls how employees, contractors, and partners access digital resources. This guide covers core IAM components, architecture patterns, implementation strategies, and best practices. Learn how to automate identity lifecycles, enforce authentication standards, and meet compliance requirements.

Complete Zero Trust Security Guide for Modern Businesses
Zero-Trust Security represents a fundamental shift in how organizations approach cybersecurity in today's digital landscape. This framework operates on the principle that no user or device should be trusted by default. The guide covers core zero-trust principles, compelling benefits, and practical implementation strategies for modern enterprises. Explore the real-world applications of Zero-Trust across remote work, cloud security, and compliance scenarios.

Role-Based Access Control (RBAC): A Complete Guide for Secure Access Management
Role-Based Access Control (RBAC) has become the foundation of modern access management for organizations worldwide. RBAC simplifies security by assigning permissions based on job roles rather than individual users. This guide explains how RBAC strengthens data protection, streamlines user management, and supports compliance requirements. Learn practical implementation approaches, industry-specific applications, and strategies for overcoming common obstacles.

Attribute-Based Access Control (ABAC): A Complete Guide
Attribute-Based Access Control (ABAC) revolutionizes how organizations manage access by evaluating user, resource, and environmental attributes, rather than relying on fixed roles and permissions. This comprehensive guide explores what ABAC is, how it works, and why it matters for modern enterprises. Learn about the key components, top benefits, practical use cases, and best practices for implementing ABAC.

Unified Identity Management Explained: How It Simplifies Enterprise Security
Unified Identity Management (UIM) consolidates digital identities into a single authoritative system, eliminating fragmentation across enterprise platforms. This comprehensive guide examines how centralized identity repositories function, the security benefits they offer, and their role in ensuring regulatory compliance. Explore implementation strategies, real-world applications across hybrid environments, and expert tips for successful deployment.

RBAC vs ABAC: What’s the Difference and Which Access Control Model Fits Your Organization
Access control determines who can access organizational resources and under what conditions. Role-Based Access Control (RBAC) assigns permissions through predefined job roles, while Attribute-Based Access Control (ABAC) evaluates multiple attributes dynamically. Learn how each model operates, their architectural differences, and practical implementation considerations. The guide covers real-world examples, provides detailed comparisons across scalability and security, and offers decision frameworks for selecting between models.
What Is Identity Orchestration? The Future of Unified, Passwordless, and Secure User Journeys
Identity orchestration is a framework that connects and automates multiple identity systems to create unified authentication experiences across enterprises. It eliminates fragmented login processes by coordinating SSO, MFA, directories, and authentication methods into seamless workflows. In this guide, you'll learn what identity orchestration is, how it works, and its key benefits.

Workplace Security: How to Create a Safe and Secure Work Environment
Workplace security protects your people, assets, and data from evolving threats. This comprehensive guide covers everything you need to build effective security systems. Learn why security matters, common risks organizations face, and essential protection components.
Making every day-in-the-life of frontline workers frictionless & secure!
Get the latest updates! Subscribe now!



