The OLOID Blog
Insights on identity, access, and security for the modern frontline workforce.

Featured
HIPAA Access Control Checklist: A Practical Guide for 2026
The HIPAA access control checklist covers the technical, administrative, and physical safeguards that govern who can access electronic protected health information, under what conditions, and with full audit trail accountability. Most organizations underestimate where their access control program breaks down in practice, particularly around shared devices, over-privileged accounts, and access that outlasts employment or role changes. This guide covers what HIPAA's Security Rule requires for access controls, what real OCR enforcement cases reveal about the most common compliance gaps, and what compliant identity and access management looks like in clinical and frontline environments.
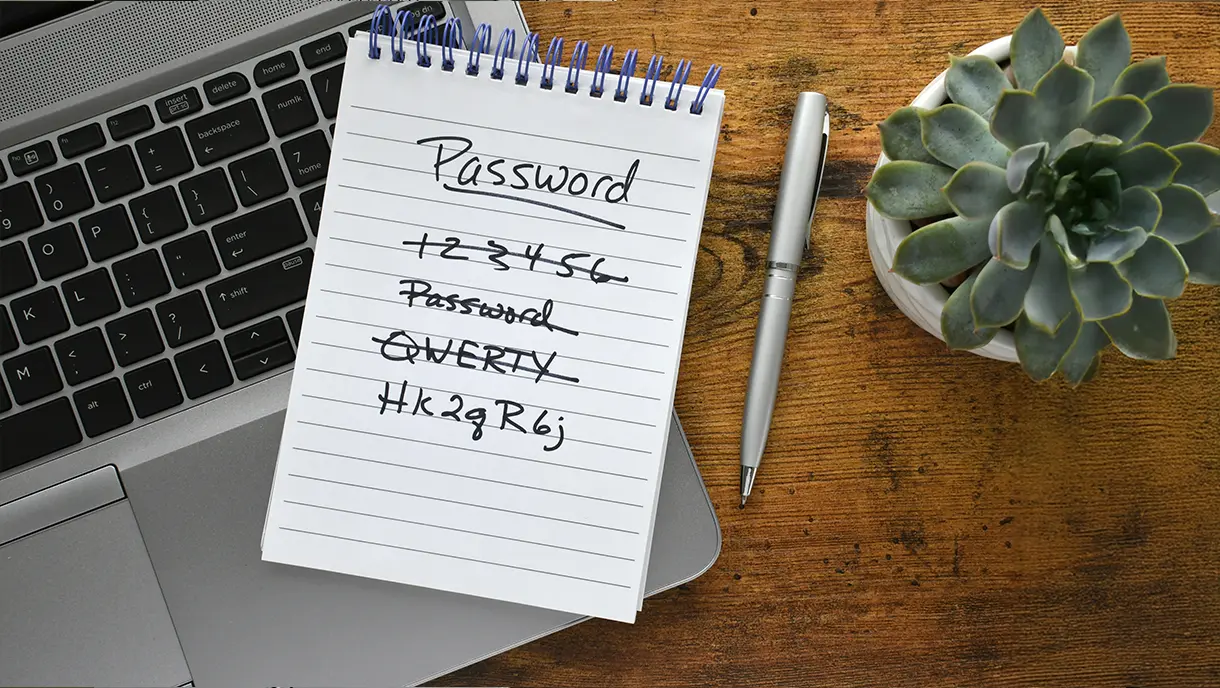
Top 10 Password Alternatives: What’s Replacing Passwords in 2026?
Organizations are shifting away from traditional passwords toward passwordless methods such as biometrics, passkeys, and SSO. This guide explores 10 leading password alternatives transforming authentication. Examine each alternative's security level, key highlights, and ideal use cases.

The Complete Guide to Healthcare Access Management
Healthcare access management protects patient data while ensuring clinical staff can access critical systems instantly. This guide explores how identity and access controls secure sensitive health information against breaches and insider threats. Learn about the core components that make access management work, from authentication methods to audit trails.

6 Types of Two-Factor Authentication (2FA) Methods
Two-factor authentication (2FA) serves as an additional security layer that prevents intruders from accessing your account even if they steal your credentials. This guide walks you through every major 2FA method, explaining how each works in real-life scenarios, where they are most effective, and how to choose the right protection for your specific situation.

Passwordless Authentication: What It Is and How It Works
Passwordless authentication replaces traditional passwords with secure, user-friendly methods like biometrics, passkeys, and magic links. This blog explores how it works, its key benefits, and why it’s becoming essential for modern identity security. Learn how platforms like OLOID enable seamless, password-free access across the workforce.
What Is Identity Orchestration? The Future of Unified, Passwordless, and Secure User Journeys
Identity orchestration is a framework that connects and automates multiple identity systems to create unified authentication experiences across enterprises. It eliminates fragmented login processes by coordinating SSO, MFA, directories, and authentication methods into seamless workflows. In this guide, you'll learn what identity orchestration is, how it works, and its key benefits.
A Complete Guide to Contactless Authentication for Modern Workplaces
Contactless authentication is reshaping how organizations secure access without compromising hygiene or user experience. This guide breaks down everything you need to know, from biometric technologies and mobile credentials to real-world applications across healthcare, manufacturing, and finance. Get practical insights on avoiding common pitfalls and implementing solutions that actually work.

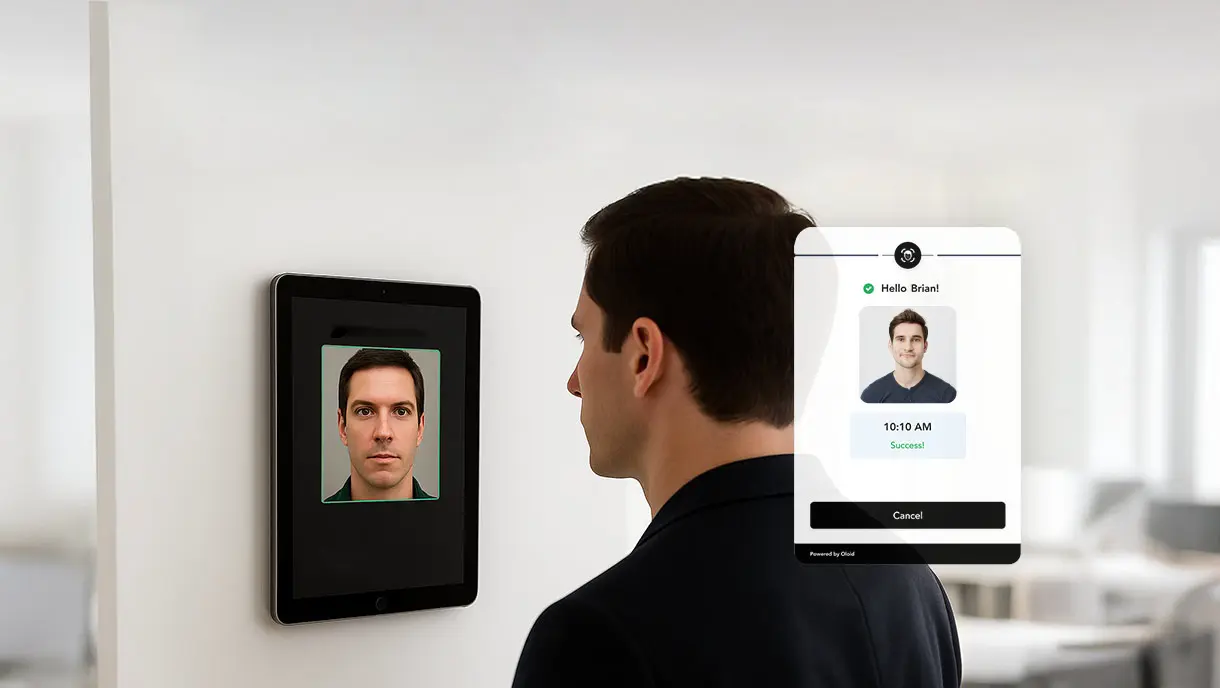
Importance of a Facial Recognition-based Time Clock
Facial recognition time clocks are redefining how organizations manage employee attendance by combining speed, accuracy, and security in a fully touchless process. This blog examines how facial recognition technology operates, its advantages over traditional punch-in systems, and its increasing role in reducing time theft and manual errors. Learn how businesses are adopting AI-powered, contactless attendance systems to streamline workforce management and ensure compliance.

Why Artificial Intelligence in Cybersecurity Is Essential for Modern Enterprises
Is your enterprise prepared for AI-powered cyberattacks? This complete guide examines how artificial intelligence strengthens cybersecurity defenses across every digital touchpoint. Learn how machine learning detects threats in milliseconds, how AI adapts to evolving attack patterns, and why automation reduces human error.

Workplace Security: How to Create a Safe and Secure Work Environment
Workplace security protects your people, assets, and data from evolving threats. This comprehensive guide covers everything you need to build effective security systems. Learn why security matters, common risks organizations face, and essential protection components.

Contactless Biometrics: The Future Of Secure And Hygienic Authentication
Struggling with hygiene risks, security vulnerabilities, and operational bottlenecks from traditional authentication systems? This guide explains how contactless biometrics solves these critical workplace challenges. Learn why leading organizations abandon touch-based fingerprint scanners for AI-powered facial recognition and palm vein technology.

Facial Authentication Explained: How It’s Transforming Digital Security
Facial authentication is transforming digital security by replacing passwords with secure biometric verification using AI-powered algorithms. This guide explains how facial authentication works, from detection to verification. Explores its benefits, including enhanced security, contactless convenience, and operational efficiency.

Enterprise SSO: The Key to Secure, Seamless Access Management for Modern Businesses
Enterprise SSO simplifies secure access by allowing employees to log in once and use multiple business applications without having to re-enter their credentials. This blog examines how Enterprise SSO operates, its key benefits for security, compliance, and productivity, and the challenges organizations encounter during implementation. It also outlines best practices and guidance on selecting the right SSO solution.
![10 Best SSO Solutions for 2026 [Expert Comparison]](https://cdn.prod.website-files.com/669022e11afe3d75b7a05794/69009aaea31a0ccf03076c62_sso-solutions.webp)
10 Best SSO Solutions for 2026 [Expert Comparison]
Modern Single Sign-On solutions deliver secure, seamless access across enterprise applications while reducing password fatigue and identity risks. This comprehensive comparison of the 10 best SSO platforms examines authentication protocols, integration capabilities, and real-world performance. From Okta to Microsoft Entra ID and OLOID, discover which SSO solution aligns with your organization's security, compliance, and user experience priorities.

Top 12 Industries Using Facial Authentication
Facial authentication is revolutionizing operations across various industries. This guide examines how sectors like manufacturing, healthcare, retail, banking, pharmaceuticals, and energy, among others, are leverage biometric technology. Explore specific use cases, implementation strategies, and tangible benefits, including enhanced security, fraud prevention, and operational efficiency.

What Is Buddy Punching and How to Prevent It?
Buddy punching occurs when employees clock in for absent coworkers, draining payroll budgets across industries. This comprehensive guide explains why traditional systems can't prevent time theft, the devastating impact on morale and compliance, and what you can do to stop it. Learn how AI-powered facial recognition, geofencing, and biometric authentication eliminate buddy punching while restoring workplace accountability.
![10 Best Multi-Factor Authentication Solutions of 2026 [Latest Rankings]](https://cdn.prod.website-files.com/669022e11afe3d75b7a05794/68f0bfd7e94d6540eb1a836a_multi-factor-authentication-solutions.webp)
10 Best Multi-Factor Authentication Solutions of 2026 [Latest Rankings]
Modern MFA solutions combine context-aware policies, biometric verification, and seamless integrations to prevent credential theft and unauthorized access. This detailed comparison of the 10 best MFA tools for 2026 examines each platform’s unique strengths, deployment options, and ROI. From Microsoft Entra ID to OLOID and Okta, you’ll discover which authentication solution aligns best with your organization’s growth, compliance, and Zero Trust security strategy.

Step-By-Step Guide to Seamless MFA Implementation
Effective MFA implementation is crucial for protecting organizations against password breaches and unauthorized access. This blog offers a step-by-step guide to deploying multi-factor authentication, from assessing infrastructure to training users and optimizing performance. Learn about common implementation pitfalls, their solutions, and best practices to simplify multi-factor authentication adoption while strengthening overall security.
Passwordless Authentication for Zero-Trust: Modern Security Without Compromise
Passwordless authentication is transforming enterprise security by eliminating passwords, reducing vulnerabilities, and enhancing user experience. This blog explores methods, implementation steps, and key considerations for adopting passwordless authentication while supporting Zero-Trust principles. OLOID’s platform offers a secure, scalable solution to help organizations modernize access management effectively.

What Is RFID Authentication and How Does It Work?
RFID authentication uses radio frequency technology to enable secure, contactless identity verification. It works through RFID tags and readers to grant quick and reliable access, making it a strong alternative to traditional methods like passwords or PINs. This blog explores how RFID authentication works, its applications, benefits, challenges, and best practices for effective implementation.

Phishing-Resistant MFA: Complete Guide to Modern, Secure Authentication
Traditional multi-factor authentication fails against modern phishing attacks. Phishing-resistant MFA uses cryptographic technology and hardware-bound credentials to eliminate vulnerabilities that attackers exploit. This guide covers how it works, key technologies like FIDO2 and security keys, implementation steps, and real-world attack scenarios it blocks. Learn the benefits, including faster logins and stronger security.

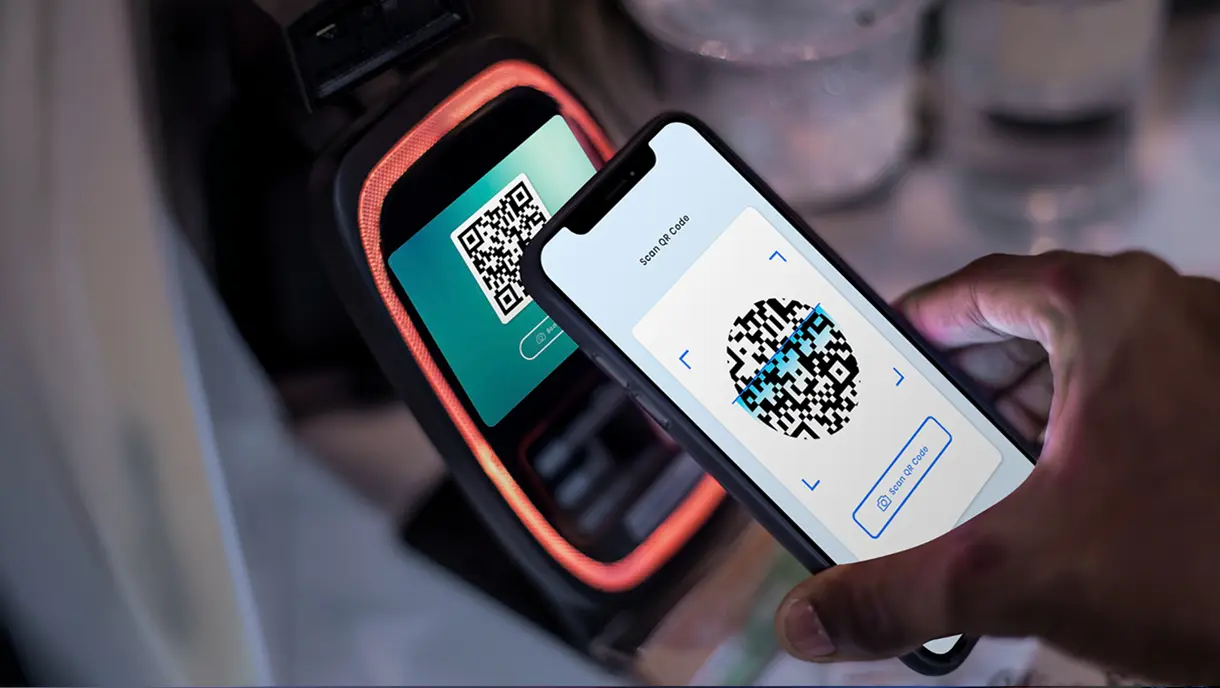
The Ultimate Guide to QR Code Authentication for Modern Security
QR code authentication revolutionizes organizational security by eliminating password vulnerabilities. This comprehensive guide covers passwordless authentication through scannable codes, comparing static versus dynamic implementations, and demonstrating superior security over traditional methods. Learn implementation methodology, security best practices, compliance requirements, risk management strategies, and real-world solutions for addressing modern authentication challenges.

NFC Authentication: Basics, Benefits, Models, and Implementation
NFC authentication revolutionizes workplace security by eliminating password vulnerabilities. It is a short-range wireless technology that verifies identity within a contactless interaction distance of four centimeters. This blog provides a comprehensive understanding of what Near Field Communication (NFC) authentication is, why it is a great alternative to traditional passwordless-based authentication, and how businesses can implement it.

PIN Authentication: How It Powers Modern Business Security
PIN authentication revolutionizes workplace security by eliminating password vulnerabilities while providing instant access for frontline workers using shared devices. This technology offers superior phishing resistance through local validation and integrates seamlessly with comprehensive passwordless solutions that combine biometric verification, badge access, and NFC cards. Explore how PIN authentication works and how it can improve your security in this detailed guide.

10 Key Passwordless Authentication Best Practices to Streamline Access Management
Passwordless authentication eliminates security vulnerabilities while improving user experience across organizations. This guide explores 10 essential passwordless authentication best practices. Following these proven strategies enables organizations to deploy secure, user-friendly authentication systems that reduce costs and enhance their security posture.

10 Best Identity and Access Management Tools for 2026
Choosing the right Identity and Access Management (IAM) solution is critical for securing systems, managing access, and ensuring compliance in today’s hybrid and cloud-driven environments. This blog reviews the 10 best IAM tools for 2026, highlighting their key features, strengths, and ideal use cases. It also addresses common challenges, evaluation criteria, and how IAM platforms can streamline security while improving user experience, helping organizations make informed decisions.
![10 Best Passwordless Authentication Solutions of 2026 [Latest Rankings]](https://cdn.prod.website-files.com/669022e11afe3d75b7a05794/68f236069554ac4369a98ae4_best-passwordless-authentication-solutions.webp)
10 Best Passwordless Authentication Solutions of 2026 [Latest Rankings]
Passwordless authentication has evolved from a security trend to a business necessity, with organizations seeking alternatives to traditional password-based systems that create vulnerabilities and operational inefficiencies. This comprehensive guide examined 10 leading passwordless authentication solutions, each designed for different organizational needs and use cases.

Workforce Authentication: The Key to Securing Modern Workplaces
Modern workplaces face unprecedented cyber threats, with traditional password systems creating massive security gaps. This comprehensive guide explores workforce authentication fundamentals, from traditional methods to cutting-edge passwordless solutions. Learn about implementation challenges, compliance requirements, and best practices for securing your workforce.
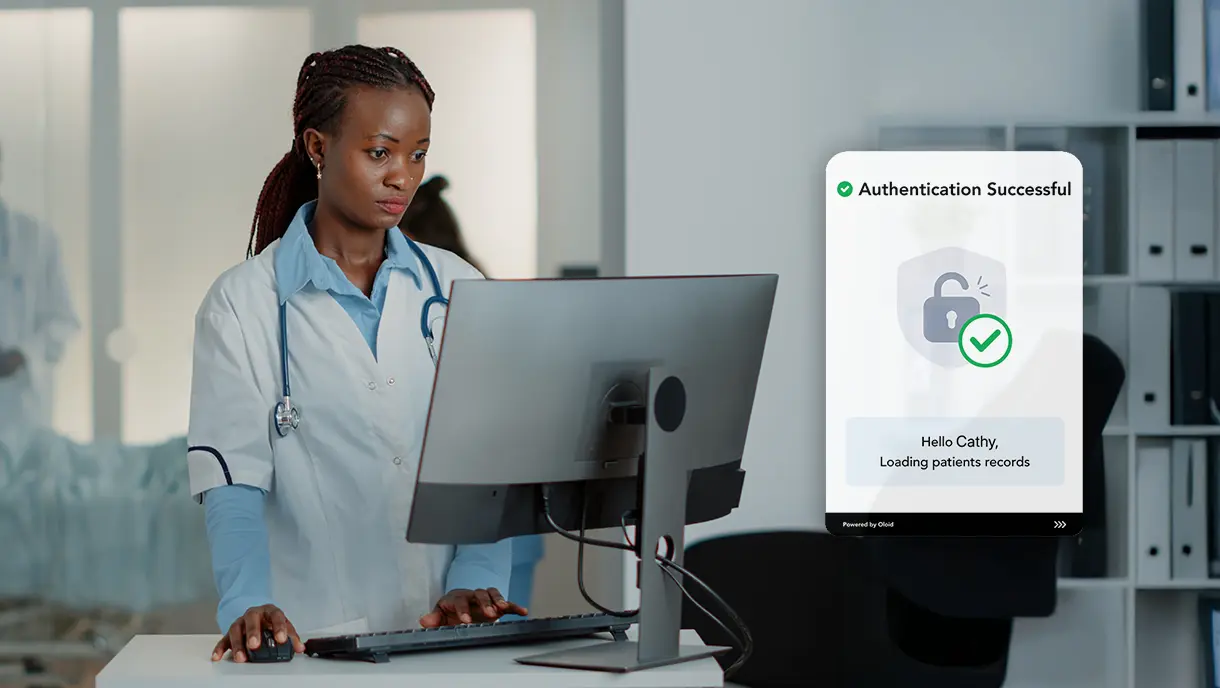
SSO for Healthcare: Simplifying Access While Strengthening Security
The write-up explains how Single Sign-On (SSO) simplifies access to multiple healthcare systems, reducing password fatigue, improving clinical efficiency, and strengthening data security. It highlights unique compliance needs, key features of healthcare-focused SSO, implementation best practices, and how OLOID’s passwordless authentication platform enhances security, streamlines workflows, and supports HIPAA and DEA EPCS compliance for modern healthcare environments.

Biometrics in Healthcare: Transforming Patient Security and Care
Biometric technologies like fingerprint, facial, iris, and voice recognition are revolutionizing healthcare by improving patient identification, security, and operational efficiency while ensuring regulatory compliance. This blog on biometrics in healthcare highlights real-world uses, implementation challenges, and how platforms like OLOID streamline passwordless authentication for safer, faster, and more patient-friendly care.

How Passwordless Login Solves Access Challenges for Factory Workers with Diverse Language Backgrounds
Multilingual factory teams struggle under English-only password systems that slow access, drive risky credential sharing, and overwhelm IT with resets. Passwordless login using facial recognition, badges, and QR codes transcends language barriers, delivering sub-second authentication, stronger security, improved worker productivity, better compliance, and lower IT costs while integrating seamlessly with existing factory systems across all shifts and facilities.
Making every day-in-the-life of frontline workers frictionless & secure!
Get the latest updates! Subscribe now!



