Wellness Attestation Made Easy with Security Automation
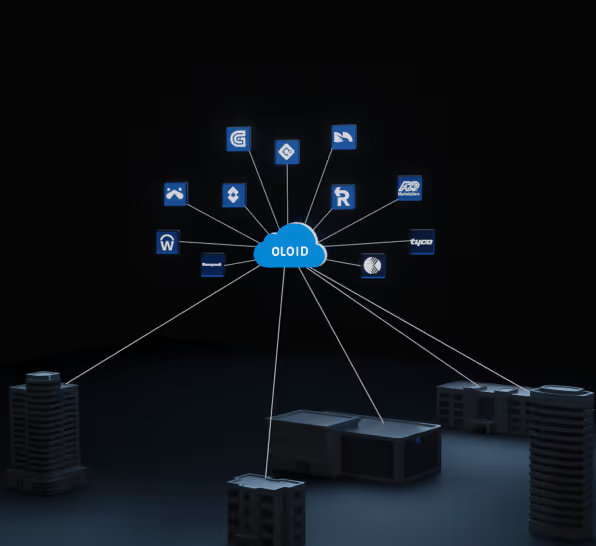
As healthcare networks grow, managing security manually becomes inefficient and risky. Automation helps hospitals streamline operations, secure endpoints, and manage wellness attestations efficiently. Technologies like RPA, SOAR, and XDR reduce breach risks, improve response times, and ensure compliance. OLOID’s automation solutions enhance both digital and physical security in healthcare, fostering a safer and more trusted environment.
The medical field is witnessing substantial network growth, making manual management of all network security points increasingly challenging. Moreover, overseeing a growing number of devices connected to a single network across various hospital departments is daunting.
In this environment, manual security operations can slow down the detection and remediation of issues, leading to resource configuration errors and inconsistent policy applications. Such lapses render the entire network of medical institutions vulnerable to cyber-attacks.
Implementing security workflow automation enables network administrators to streamline daily operations and integrate robust security measures. Automation allows hospitals to utilize hybrid cloud infrastructures and seamless API integrations, potentially reducing the average cost of network breaches by up to 95%.
This article explores the essential aspects of implementing automation in security workflows and its benefits in wellness attestation.
What Is Wellness Attestation and Why Does It Require Automation?
Wellness attestation is a mandatory form for all employees, staff members, and visitors entering a medical facility, requiring details about one’s health status, recent contacts, and medical clearances.
Managing the daily influx of individuals and organizing their details is strenuous, often leading to cumbersome rollouts of new wellness attestation forms. Automation facilitates this process, enhancing security and efficiency at entry points through user access control privileges. Modern healthcare passwordless authentication can seamlessly integrate wellness attestation workflows with identity verification, enabling contactless, secure entry without compromising security or adding friction for staff and visitors.
What Processes Can Be Automated in Security Workflows?
Threat Hunting
Automation in security workflows reduces the time and cost associated with threat detection and management, safeguarding sensitive medical data.
Rapid Response to Incidents
Automation ensures swift incident responses, potentially saving substantial amounts as cited in IBM reports and streamlining the remediation process across various platforms, applications, and tools.
Protection of Endpoints
Automated tools help establish Endpoint Protection Platforms (EPP), enhancing the security of endpoint devices, which are often prime targets for cyber-attacks.
Types of Automation in Security Workflows
Robotic Process Automation (RPA)
RPA is suitable for automating lower-level processes that do not require intelligent analysis, operating through a central program that commands virtualized computer systems.
Security Orchestration, Automation & Response (SOAR)
SOAR autonomously acquires data on security threats and responds to incidents, helping to standardize and automate response functions.
Extended Detection and Response (XDR)
XDR, an advanced version of endpoint detection systems, consolidates data from various security environments to identify elusive attacks, empowering administrators to respond effectively.
Choosing the Right Automation for Security Workflows
When considering automation in security workflows, ask:
- Is the process repeatable and consistent?
- Can an API furnish the necessary data for automation?
- Will automation streamline the workflow and save time?
Conclusion
Implementing OLOID’s security workflow automation not only simplifies the wellness attestation process but also brings a new level of efficiency and security to medical institutions. By leveraging automation, hospitals can ensure a safer and more secure operational environment, fostering trust among employees, patients, and visitors.
Moreover, focusing on occupational health and safety through automated security workflows translates to a workplace where employee safety is a priority. It aligns with the objectives of Occupational Health and Safety (OHS) standards, promoting a culture of safety at the workplace.
As we move forward in a technologically advanced era, the integration of such automation becomes not just beneficial but essential in maintaining the highest standards of security and safety. It is a step towards a future where technology and foresight work hand in hand to create environments that are not only secure but also foster well-being and trust.
Discover how OLOID is paving the way in security workflow automation, helping institutions stay one step ahead in ensuring safety and compliance. Dive deeper into the world of automated security workflows with OLOID and take a significant step towards a safer, more secure future.
FAQs
1. How can automation in healthcare benefit the wellness attestation process?
Wellness attestation, requiring health information and clearances for anyone entering a medical facility, can be streamlined through automation in healthcare. Automation can:
- Reduce manual data entry and verification tasks associated with wellness attestation forms.
- Enforce access control based on attestation status, ensuring only authorized individuals enter specific areas.
- Improve overall efficiency and security at entry points within healthcare facilities.
2. What specific security processes in healthcare can benefit from workflow automation?
Several security processes crucial for healthcare institutions can be optimized through workflow automation in healthcare. The blog highlights some key areas:
- Threat hunting: Automating threat detection reduces time and cost associated with safeguarding sensitive patient data in healthcare facilities.
- Incident response: Implementing automated responses to security incidents can save significant resources and streamline remediation processes across various platforms used in hospitals.
- Endpoint protection: Automated tools can establish and manage Endpoint Protection Platforms (EPP) to secure devices vulnerable to cyberattacks, enhancing overall security in healthcare environments.
3. What are the different types of automation used in healthcare security workflows?
The blog explores three main types of automation used in automated security workflows within the healthcare industry:
- Robotic Process Automation (RPA): Ideal for repetitive tasks like data entry in wellness attestation forms, RPA operates through a central program controlling virtual systems.
- Security Orchestration, Automation & Response (SOAR): SOAR automates security incident data management and response within healthcare facilities, helping standardize and streamline response functions to security threats.
- Extended Detection and Response (XDR): An advanced form of endpoint detection, XDR gathers data from various security environments in hospitals to identify complex attacks and enable effective responses, bolstering overall security.



Get the latest updates! Subscribe now!


