The OLOID Blog
Articles and Podcasts on Customer Service, AI and Automation, Product, and more

Featured
Why Shared Devices Break Traditional IAM (And What Comes Next)
Every IAM system sold in the last two decades was built on a quiet assumption: one person, one device. On the frontline, that assumption has never been true.

How do RFID cards work?
This guide explains what RFID cards are and how they function as contactless tools for secure identification and access. It covers the working principles of RFID cards, their benefits over traditional password-based systems, and common real-world applications across industries. Learn how to choose the right RFID card solution, compare them with mobile access, and explore their role in enhancing security and efficiency.

The Evolution of Authentication: Embracing Passwordless Security
This blog discusses the shift from traditional password-based authentication to passwordless security methods as a response to growing cybersecurity threats. Learn why passwords are now considered inadequate, how technologies like biometrics and multi-factor authentication offer safer alternatives, and the benefits of adopting these advanced solutions. Gain insights into practical steps for implementing passwordless systems and highlights their advantages in terms of security, user experience, and operational efficiency.

Facial Recognition in Law Enforcement: Security vs Privacy
This post explores the use of facial recognition technology in law enforcement, focusing on the debate between enhancing security and protecting privacy. It covers how the technology aids crime prevention, investigations, and public safety, while also addressing challenges like bias, privacy invasion, and regulatory gaps. The article emphasizes the need to balance these concerns and highlights innovative solutions that aim to align security with individual rights protection.
Wellness Attestation Made Easy with Security Automation
As healthcare networks grow, managing security manually becomes inefficient and risky. Automation helps hospitals streamline operations, secure endpoints, and manage wellness attestations efficiently. Technologies like RPA, SOAR, and XDR reduce breach risks, improve response times, and ensure compliance. OLOID’s automation solutions enhance both digital and physical security in healthcare, fostering a safer and more trusted environment.

Understanding Time-Clocking Systems: Benefits and Challenges
This post explains what time-clocking systems are and how they help businesses track employee work hours with greater accuracy and efficiency. It outlines key benefits such as improved payroll processing, enhanced attendance monitoring, legal compliance, and increased accountability, while also highlighting challenges like trust issues, system inaccuracies, and data security concerns. Gain practical insights into selecting, implementing, and managing these systems to maximize efficiency while maintaining a positive workplace culture.

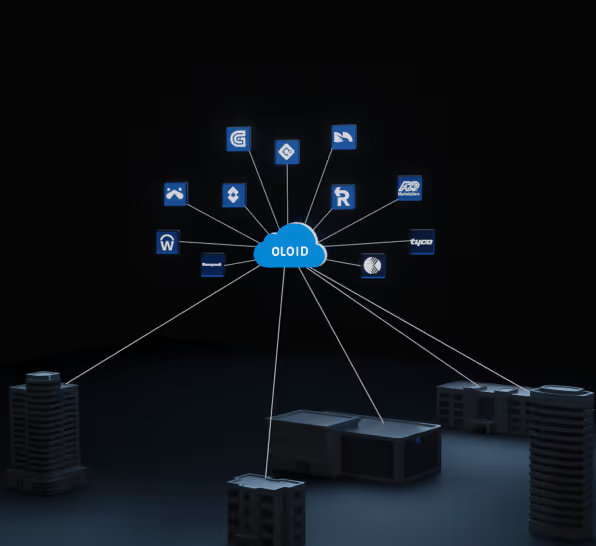
System Integrators: Role in the Access Control Industry
System integrators design and manage seamless access control systems by combining hardware and software from multiple vendors. They enable secure, scalable, and efficient security setups tailored to each organization’s needs. Modern platforms like Oloid support low-code integration, biometrics, and cloud-based management. This unified approach enhances security, reduces costs, and prepares businesses for future growth.

Everything You Must Know About Security Shell (SSH)
This post explores what SSH (Secure Shell) is and how it enables secure communication between devices over a network. It explains the working principles of SSH, including encryption methods, authentication processes, and tunneling features that help protect data in transit. Learn about the key benefits and limitations of SSH, helping them understand when and how to use it effectively for secure remote access and file transfers.

What is an Integrated Workplace Management System?
An Integrated Workplace Management System (IWMS) is a software platform that centralizes and streamlines various workplace functions like facility management, space optimization, asset tracking, and sustainability initiatives. This blog explains IWMS in detail, covering its key features, benefits, differences from other facility management tools, and considerations for successful implementation. Gain insights into how IWMS can improve efficiency, reduce costs, enhance decision-making, and learn about the top IWMS tools available in the market.

What Is a Visitor Management System?
A visitor management system (VMS) is a digital solution that helps organizations register, track, and manage visitors entering their premises to enhance security and efficiency. This blog explains how a VMS works, its key features, types, and policies that ensure streamlined visitor experiences and data protection. Gain insights into how implementing a modern VMS can improve safety, compliance, and overall visitor satisfaction across industries.

Enhancing Visitor Management Through Security Workflow Automation
This post explores how automating security workflows can significantly enhance visitor management by replacing traditional manual processes with efficient, technology-driven solutions. Learn about the risks of manual systems, the core features and advantages of automated visitor management tools, and best practices for successful implementation.

The Future of Identity Management: Key Trends Transforming Access Control
Identity management is evolving with trends like biometric authentication, multi-factor authentication, decentralized identity (DID), AI integration, zero trust security, and user-centric models. These innovations enhance security, privacy, and user control while reducing fraud and operational inefficiencies. Businesses must adapt to these trends to stay secure and future-ready.

Facial Recognition and Data Privacy: Striking the Right Balance
This blog explores the growing role of facial recognition technology and the pressing need to balance its benefits with data privacy concerns. It examines major privacy risks such as biometric data misuse, misidentification, and lack of consent while highlighting innovative strategies like anonymization, privacy-by-design, and strong regulatory compliance. Gain insights into how businesses and policymakers can adopt responsible practices to ensure facial recognition technology is both effective and ethically implemented.

Which One is Better: Cloud-Based Security or On-Premise Security?
This blog explores the critical debate between cloud-based security and on-premise security, focusing on which approach is better for modern businesses in a digital world. Learn about the pros, cons, and practical trade-offs for each solution, including cost, control, scalability, and security considerations. The article helps companies assess their specific needs and provides guidance on selecting the right security strategy for their unique requirements.

Blockchain-Based Access Control: 10 Points You Must Know
Blockchain-based access control uses decentralized ledger technology to manage digital identities securely, transparently, and without relying on central authorities. This blog outlines essential concepts such as decentralized identity management, immutable records, smart contracts, and interoperability that showcase how blockchain can enhance security, privacy, and efficiency in access control systems. Gain insights into current trends, industry applications, and future prospects, equipping them to understand and explore the transformative potential of blockchain in cybersecurity.

Time Clocks: Desk Workers vs. Frontline - One Size Fits All?
This blog explores whether a single time clock solution can effectively serve both desk workers and frontline employees. It compares different types of time-tracking systems, analyzing their suitability for various work environments and job roles. Learn how choosing tailored time clock solutions can enhance accuracy, productivity, compliance, and overall workforce efficiency.

What Is Zero Trust Architecture?
Zero Trust Architecture (ZTA) is a security model that eliminates implicit trust by verifying every user and device before granting access. It enforces least privilege access, microsegmentation, and continuous authentication to prevent breaches. ZTA improves security, compliance, and user experience across modern, hybrid IT environments.

Integrate Time & Attendance with PACS: Pros & Challenges
Research shows 45% of employees view access control systems as vital for workplace security, yet most organizations manage physical access and time tracking separately, creating inefficiencies and data accuracy issues. This practical guide examines the benefits and challenges of integrating PACS with time and attendance systems, from streamlined operations and reduced labor costs to implementation hurdles and training requirements. Learn proven strategies for successful integration that enhance security, improve data accuracy, and boost employee satisfaction.

RFID vs NFC vs BLE: Best Access Tech for Your Business
This post explores the differences between RFID, NFC, and BLE technologies to help businesses choose the best access and connectivity solution. It explains how each technology works, compares their range, speed, security, and cost, and highlights ideal use cases for various applications. Gain insights into which option suits your needs for asset tracking, payments, IoT devices, or long-range communication.

Unifying Physical & Cyber Identities for Workplace Security
Organizations managing physical and cyber identities separately create dangerous security gaps that hackers and malicious insiders can exploit. This post explores how unified Identity and Access Management solutions bridge this divide, combining badge access and digital credentials into a single integrated system. Learn how identity unification strengthens security posture, simplifies employee lifecycle management, enhances user experience with single sign-on capabilities, and ensures compliance with regulations like HIPAA and GDPR.
Multi-Factor Authentication (MFA): A Complete Guide to Strengthening Security
Multi-Factor Authentication (MFA) enhances cybersecurity by requiring users to verify their identity through multiple methods—like biometrics, access cards, or PINs—making it harder for attackers to gain access. MFA reduces phishing risks, protects against password fatigue, improves compliance, and builds user trust. While challenges like user resistance, integration effort, and cost exist, the benefits far outweigh them. OLOID’s passwordless MFA solution offers a seamless, secure login experience—especially for frontline and mobile workers—by combining physical and digital authentication methods.

20 Stats To Consider About the Physical Access And Identity Management Industry
Physical Access and Identity Management (PIAM) solutions have become more affordable and essential for organizations of all sizes, especially with the rise of remote work. They help manage who can access physical spaces and sensitive systems by verifying identities, assigning roles, and protecting data. The industry is growing rapidly, with projections reaching $34.5 billion by 2028. Key stats highlight rising cyber threats, credential theft, and the need for secure access controls, making PIAM a critical investment for modern security and compliance.

Commercial Property Owner's Guide to Enhancing Tenant Experience
This blog discusses how property owners can improve satisfaction, retention, and reputation by focusing on tenant needs. It explores actionable strategies such as maintaining buildings, offering modern amenities, ensuring safety and accessibility, and strengthening communication. Gain insights into creating a thriving and profitable property environment by prioritizing tenant comfort and engagement.

What Is a Proxy Server? How to Secure Proxy Connections
This blog explains what a proxy server is and why securing proxy connections is vital for online privacy and safety. Discover the different types of proxy servers, their benefits for security and performance, and essential best practices for minimizing risks. Gain practical guidance for choosing and configuring proxy servers to enhance security, privacy, and network efficiency.

What Are the Common Data Governance Mistakes & How to Fix Them
This blog post discusses the most common mistakes organizations make when implementing data governance and why addressing these pitfalls is critical for business success. Learn about nine specific challenges, such as lack of strategy, poor data quality management, and inadequate executive support, along with practical solutions to avoid these errors. By following the guidance provided, organizations can strengthen their governance frameworks, boost compliance, and unlock greater value from their data assets.

On-Premise to Cloud Migration: A Guide to a Successful Transition
This blog offers a comprehensive guide for businesses transitioning from on-premise systems to cloud infrastructure, highlighting both opportunities and challenges. Learn best practices for preparing, executing, and optimizing a migration, including guidance on security, cost management, and minimizing downtime. The article also provides actionable steps and expert insights to ensure a smooth and successful migration, enabling organizations to fully harness the benefits of the cloud.

How to Manage Multi-Site Access Control From a Centralized Platform
Managing multi-site access control can be simplified through centralized management, clear policies, and the right technology. Best practices include using multi-factor authentication, visitor management systems, and regular security audits. These steps improve efficiency, enhance security, and ensure compliance across all locations.

How Does OLOID Time Clock Help in Your Workforce Management?
OLOID Time Clock helps organizations streamline workforce management by automating accurate tracking of employee attendance, shift times, and identity verification. Discover how digital time clock systems like OLOID boost productivity, increase security, and simplify payroll by seamlessly integrating with HR systems and preventing time theft. This article also explains OLOID’s advantages, from contactless authentication and easy onboarding to eco-friendly practices that cut costs and improve business efficiency.

What is Cyber Insurance? 10 Things You Must Know About It
This blog explains what cyber insurance is—a specialized coverage designed to protect organizations from financial and reputational damage caused by cyber incidents. Discover the key benefits of cyber insurance, such as financial protection, coverage for various types of attacks, and incentives for adopting better cybersecurity. learn what to consider before choosing a policy, with practical guidance to help businesses select and get the most out of their cyber insurance coverage.
Biometrics vs Face Recognition for Identity Authentication
This blog explores the differences between biometrics and facial recognition technologies for identity authentication in modern access control systems. It explains how organizations are adopting these technologies for security, convenience, and contactless access in workplaces and industries. Gain insights into the strengths, limitations, and best-use cases of each approach to determine the most suitable authentication method for your organization.

Time & Attendance Tracking with Security Workflow Automation
Security workflow automation is transforming time and attendance tracking by improving accuracy, saving time, reducing costs, and enabling real-time insights. With features like biometric logins and seamless integration, it helps businesses boost productivity and streamline workforce management.
Making every day-in-the-life of frontline workers frictionless & secure!
Get the latest updates! Subscribe now!
Thank you! Your submission has been received!
Oops! Something went wrong while submitting the form.



