The OLOID Blog
Articles and Podcasts on Customer Service, AI and Automation, Product, and more

Featured
Why Shared Devices Break Traditional IAM (And What Comes Next)
Every IAM system sold in the last two decades was built on a quiet assumption: one person, one device. On the frontline, that assumption has never been true.

The Security Risks of Shared Passwords in Manufacturing and How Passwordless Prevents Them
Generic credentials and sticky-note passwords create massive security gaps in manufacturing environments. This comprehensive guide covers the business risks of shared logins, why they persist despite vulnerabilities, and how modern passwordless authentication delivers individual accountability while working seamlessly with existing industrial systems and workflows.

How Zero-Touch PACS Makes RFID Badge Authentication Seamless Across Enterprises
RFID badges are mostly used to handle only physical access, requiring separate digital logins. Zero-touch PACS integration changes this by automatically syncing badge credentials across all systems. This guide covers implementation benefits, technical architecture, and how enterprises achieve unified authentication without manual IT provisioning overhead.

The Complete Guide to Frontline IAM for Manufacturing
Manufacturing facilities struggle with shared passwords, authentication delays, and compliance gaps on factory floors. This guide explores specialized Frontline IAM solutions that enable seamless, secure access for industrial workers while integrating with OT systems and delivering measurable productivity gains.
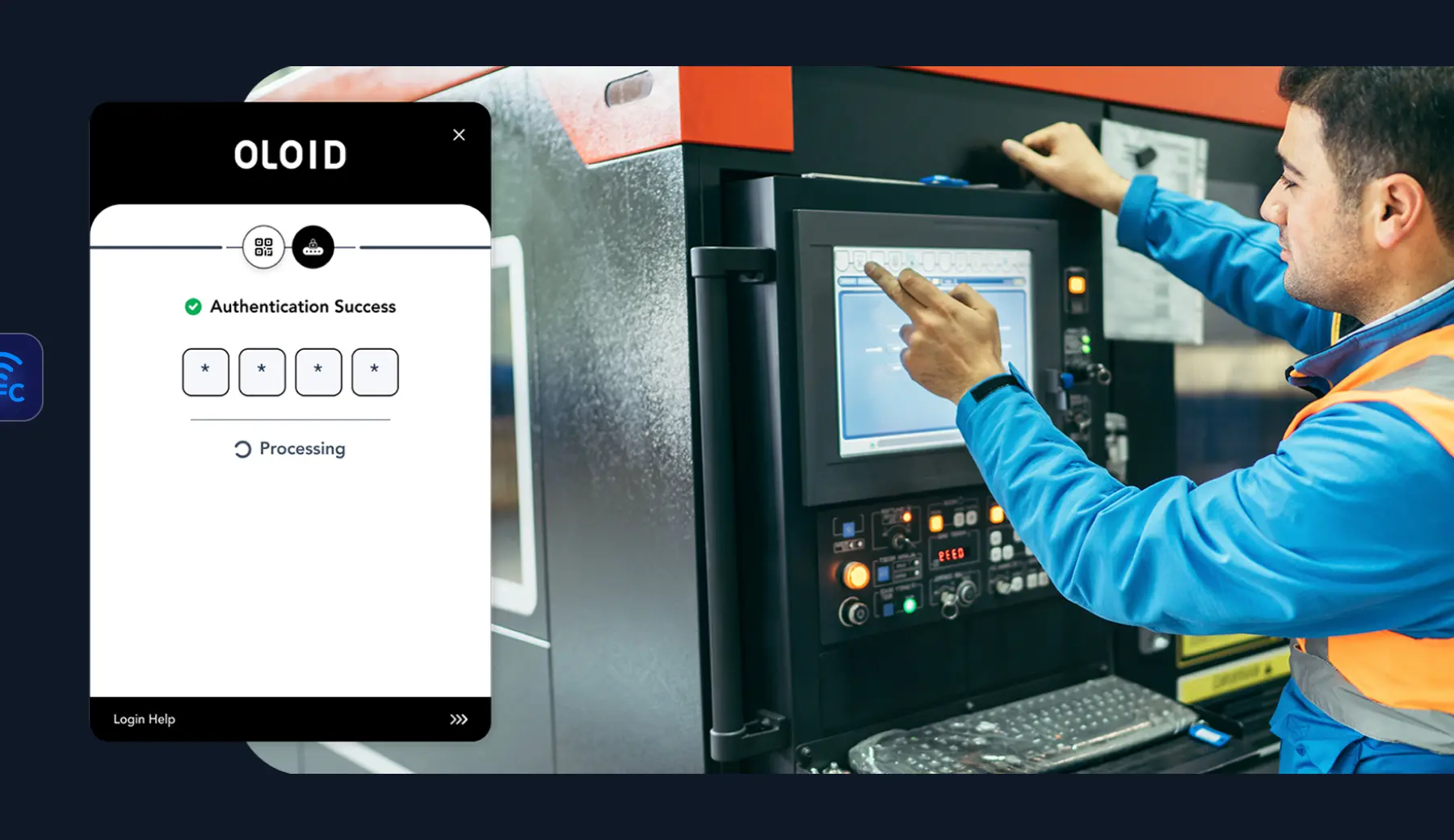
Securing Shared Devices Without Shared Passwords
Shared devices are vital in frontline work, but shared passwords and legacy MFA can’t meet the demands of shift-based, high-turnover environments. Modern security needs contactless, passwordless solutions that scale, ensuring secure access, individual accountability, and fast ROI.
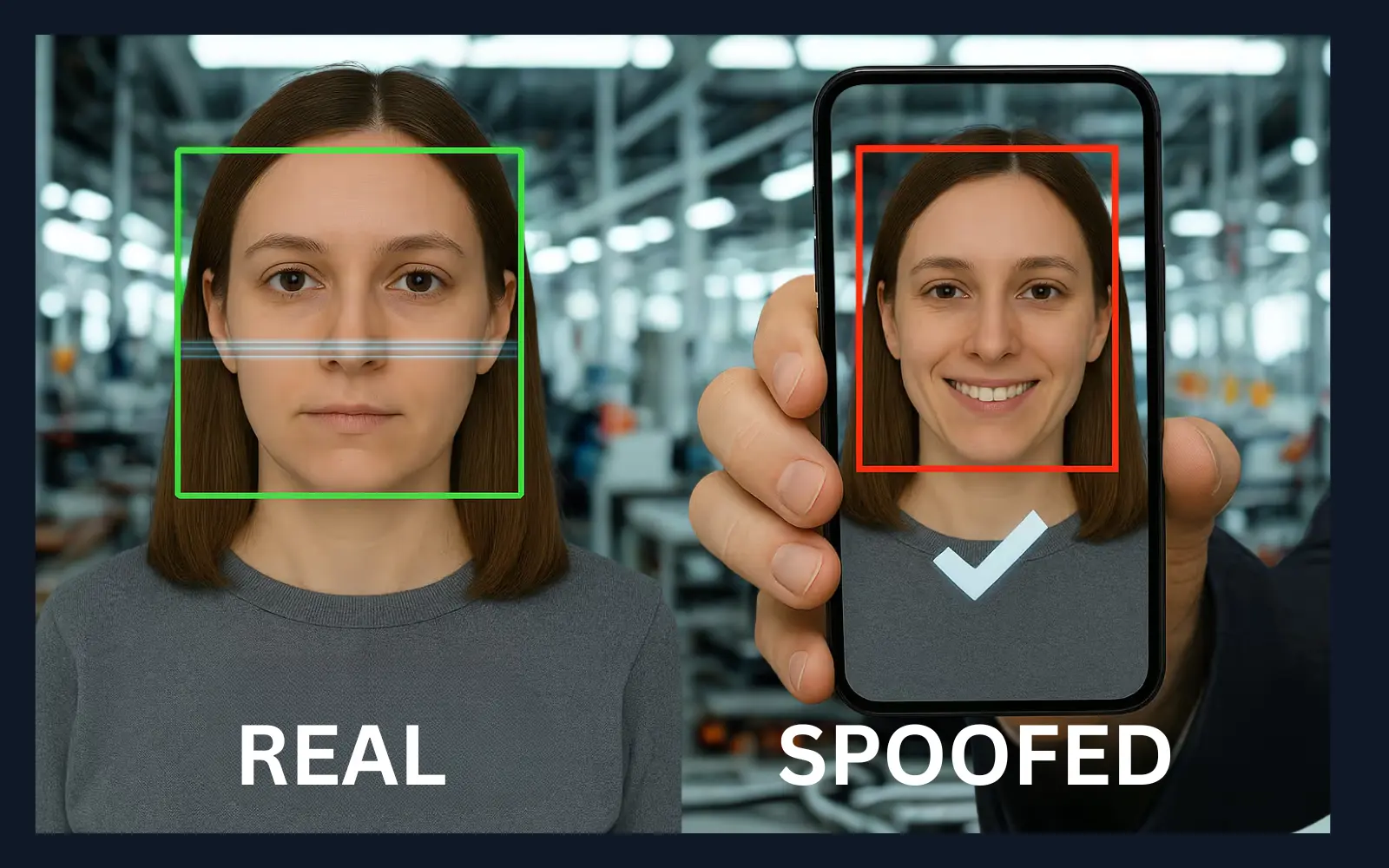
Liveness Detection Guide: Protecting Digital Identity 2026
Learn how liveness detection is revolutionizing digital identity verification in 2026. Discover the technology behind preventing spoofing attacks like deepfakes, photos, and masks. Understand its role in securing transactions, improving compliance, and enhancing security across industries such as finance, healthcare, and manufacturing.

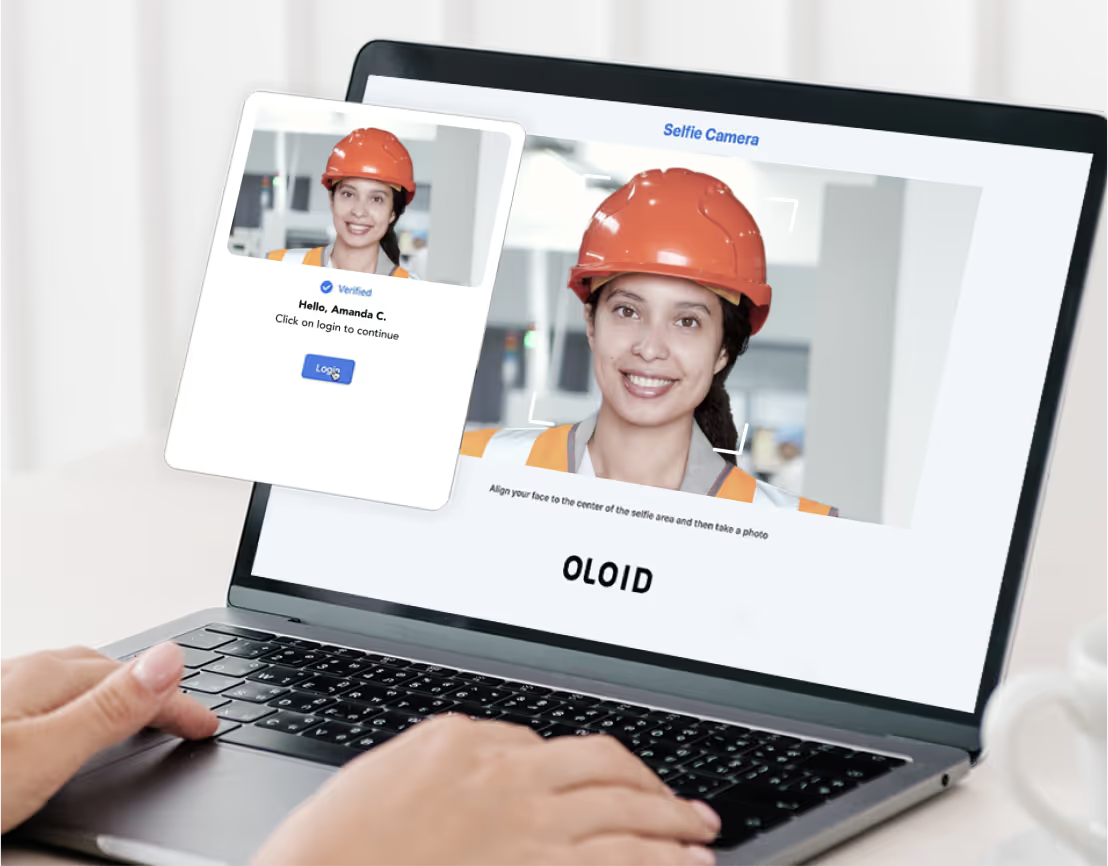
How OLOID Secures and Automates Manufacturing Access
The post explains how OLOID secures and automates access in manufacturing environments using modern identity and automation solutions. It highlights features like passwordless authentication, contactless time tracking, and workflow automation. Learn how OLOID boosts safety, efficiency, and compliance for frontline workers.

OLOID at Oktane 2024 in Las Vegas
Oktane 2024 is set to prove to be, once again, the biggest Identity event of the year, based on Okta’s standing as the world’s leading identity and access management company, and their industry-leading solutions and thought leadership, along with the participation of strategic partners such as OLOID, a leading provider of physical identity and access […]

OLOID at Workday Rising 2024 in Las Vegas
Workday Rising is set to prove to be, once again, the biggest Enterprise Management event of the year, based on Workday’s standing as the world’s leading Finance, HR, and Planning cloud software company, with their industry-leading solutions and thought leadership, along with the participation of innovation partners such as OLOID.

Biometrics by the Numbers: Trends, Adoption & Challenges
This post explores how biometric technologies are transforming identity verification and data security. It highlights key statistics on adoption, market growth, and consumer trust. Gain insight into privacy, accuracy, and regulatory challenges shaping the future of biometrics.

Passwordless vs Traditional Logins: Which Is Better?
As cyber threats grow more advanced, traditional password systems struggle to keep up due to vulnerabilities like phishing and password reuse. Passwordless authentication—using biometrics, security tokens, or one-time codes—offers stronger security, a better user experience, and reduced IT overhead. While traditional methods are simpler to implement, passwordless solutions scale better and future-proof organizational security. A hybrid approach can ease the transition. With support from tech giants, passwordless is rapidly becoming the new standard in cybersecurity.

Optimize Payroll with OLOID's Smart Time Clock Solution
Time theft costs U.S. businesses $50 billion annually, with buddy clocking alone accounting for $373 million in losses and manual time tracking creating error rates 8% higher than automated systems. OLOID Time Clock eliminates these costly inefficiencies through facial recognition with liveness detection, achieving sub-second authentication that prevents buddy clocking, reduces shift change congestion by 15 minutes per employee, and integrates seamlessly with existing payroll systems to deliver accurate, fraud-proof time tracking that drives immediate ROI.

Choosing the Right Time Clock for Payroll Accuracy
This post discusses how choosing the right time clock system can significantly improve payroll accuracy and efficiency. It outlines the key benefits of automated time tracking, such as reducing errors, ensuring compliance, and streamlining payroll processes. Learn the essential factors to consider—like deployment options, features, usability, security, and cost—to select a system that best fits your business needs.

Top 5 Benefits of Integrating a Time Clock with Payroll Systems
This post explores the advantages of integrating time clocks with payroll systems to enhance business efficiency and accuracy. It explains how automation reduces manual errors, improves compliance, prevents time theft, and streamlines payroll processing. Learn how this integration boosts productivity, ensures fair compensation, and provides data-driven insights for better workforce management.

OLOID's Facial Recognition for Ethical, Passwordless Access
OLOID’s facial recognition is more than just tech; it’s built around ethics, consent, and inclusivity. It solves real workplace access challenges while protecting privacy and avoiding bias. With a focus on fairness and future-proofing against regulation, OLOID ensures that authentication works for everyone, safely and securely.

Onboarding Deskless Workers: Go Passwordless for Security
This blog explores how going passwordless can transform the onboarding process for deskless workers by enhancing security and simplifying access. It explains the challenges traditional methods face—like limited device access, time constraints, and password vulnerabilities and how passwordless authentication solves them through biometrics, tokens, and multi-factor authentication. Learn the security benefits, ROI advantages, and best practices for implementing passwordless solutions to create a faster, safer, and more user-friendly onboarding experience.

MFA Compliance: Key U.S. Requirements & Regulations
Multi-Factor Authentication (MFA) has become a critical security requirement in the U.S. due to rising cyber threats and stricter regulations. It verifies user identity using two or more factors—like passwords, biometrics, or devices. Regulatory frameworks like HIPAA, GLBA, NIST, and PCI DSS encourage or mandate MFA to protect sensitive data. OLOID offers a passwordless, biometric MFA solution tailored for frontline workers, ensuring compliance, ease of use, and strong security. As threats evolve, passwordless and adaptive MFA are shaping the future of secure authentication.
How OLOID Supports Deskless Workers Daily
OLOID offers a passwordless and usernameless authentication platform tailored for deskless and frontline workers, helping CISOs and CIOs reduce insider threats, improve workforce productivity, and strengthen cybersecurity. The platform integrates with SSO systems, simplifies onboarding, enables secure shared device access, and supports multi-factor authentication without requiring phones or hardware keys. With solutions like Cloud Key for physical access and Time Clock for attendance, OLOID enhances operational efficiency, minimizes IT support costs, and ensures compliance. It's designed for high-turnover environments and industries with strict safety and hygiene standards.

Common Types Of Password Attacks and How to Defend Yourself
Password attacks—like brute-force, phishing, credential stuffing, password spraying, and keylogging—are growing threats that exploit weak, reused, or stolen credentials. Hackers use various techniques to steal login information, often targeting both individuals and businesses. To stay protected, users must adopt strong, unique passwords, enable multi-factor authentication (MFA), avoid phishing traps, and use antivirus software. Real-world breaches (Adobe, Yahoo, Equifax, Microsoft, Roku) highlight the devastating impact of poor password hygiene. Businesses should train employees, enforce strong password policies, and use security tools to monitor suspicious activity and reduce risk.

Top 11 Authentication Challenges Frontline Workers Face Using Shared Devices
Frontline workers in manufacturing, retail, healthcare, and other deskless environments often struggle with authentication challenges, including PPE interference, forgotten passwords, limited MFA options, language barriers, and fragmented admin systems. These issues slow down workflows, increase security risks, and reduce accountability on shared devices. OLOID solves these challenges with a frictionless, passwordless authentication approach using facial and palm biometrics, access badges, and passwordless SSO.

Why Passwords Are Obsolete and How Passwordless Works
This post explores why traditional passwords are becoming ineffective in protecting digital identities and how passwordless authentication is transforming security. It highlights the vulnerabilities and user frustrations tied to passwords while explaining modern alternatives like biometrics, security keys, and magic links. Learn how passwordless solutions enhance security, simplify access for frontline workers, and reduce IT overhead across organizations.

Secure Web Apps with Passwordless Authentication
This blog highlights the growing need for stronger security in web applications and introduces passwordless authentication as a superior alternative to traditional passwords. By using biometrics, magic links, or security tokens, it enhances security, user experience, and reduces IT costs. OLOID's deviceless MFA solution further extends these benefits to frontline workers using shared devices, offering secure access through face, PIN, access cards, or QR codes. The future of digital identity is passwordless—and OLOID is leading the way.

SSO vs MFA: What’s the Difference and Which One Do You Need?
This blog explains the key differences between SSO and MFA authentication technologies. SSO focuses on user convenience while MFA prioritizes security through multiple verification layers. Organizations achieve the best results by combining both technologies rather than choosing one over the other. Get practical implementation guidance and learn the combined benefits of enhanced security and improved user experience.

Shared Devices: How Frontline Workers Use Them to Authenticate
This post explains how frontline workers use shared devices like tablets, kiosks, and computers to access work systems securely. It highlights key authentication methods such as biometrics, smart cards, and role-based access control for convenience and safety. Learn how OLOID’s Passwordless Authenticator simplifies login with facial recognition and MFA, improving compliance and efficiency.

Advancing Security with Face-Based Authentication
Face-based authentication combines facial recognition with multi-factor authentication to offer a secure, convenient, and user-friendly login experience. By using unique facial features, it reduces the risks of password theft, improves user efficiency, and minimizes fraud. While it enhances security, organizations must also address privacy concerns, accessibility challenges, and accuracy limitations to ensure effective implementation.

Exploring FIDO vs FIDO2: Evolution in Secure Authentication
FIDO and FIDO 2 are modern passwordless authentication standards designed to replace traditional, vulnerable password systems. FIDO uses public-key cryptography and supports biometric and hardware key-based login, enhancing both security and user experience. FIDO 2 builds on this foundation with WebAuthn and CTAP, offering even greater interoperability, flexibility, and phishing resistance across devices and platforms. As cyber threats grow, adopting FIDO 2 helps organizations and individuals secure digital identities while simplifying access.

Integrating Passwordless Authentication into IT Strategy
This post explores the increasing significance of passwordless authentication in modern IT strategies as organizations seek stronger security and better user experiences. Discover different passwordless approaches, such as biometrics and cryptographic keys, along with their security, scalability, and cost-saving advantages, plus best practices for smooth integration. The post also details key challenges, emerging trends, and practical steps for enabling a secure and seamless authentication environment.

Application of Artificial Intelligence in Physical Security
The post explores how artificial intelligence is transforming physical security by enhancing surveillance, threat detection, and incident response. It explains the key ways AI strengthens safety measures through real-time monitoring, automated analytics, robotic patrols, and predictive maintenance. Learn about AI’s advantages, potential challenges like privacy and bias, and how responsible adoption can lead to smarter, safer environments.

What Is FIDO Authentication and How Does It Work?
Passwords are costing your organization millions in resets and breach risks. Learn how FIDO authentication eliminates these vulnerabilities with cryptographic, phishing-resistant security. Explore step-by-step implementation strategies, real-world use cases across industries, and the measurable benefits of one-tap biometric login.

Security Convergence: Integrating Physical Access Control and Cybersecurity
As physical and cyber threats increasingly intersect, organizations must move beyond siloed defenses and adopt a unified security strategy known as security convergence. By integrating physical access control systems, surveillance technologies, identity management, and cybersecurity tools, businesses gain better threat visibility, faster response, and reduced overall risk. This holistic approach also strengthens compliance, streamlines operations, and enables more informed security decisions. As connected technologies like IoT, cloud platforms, and AI continue to expand attack surfaces, security convergence becomes essential for building a resilient and future-ready security posture.

What does the future of digital identity look like?
The post explores how technological innovation, regulation, and security will shape the next era of identity verification. It highlights emerging trends such as passwordless authentication, AI-driven fraud detection, decentralized IDs, and evolving crypto regulations that are redefining trust and privacy in digital ecosystems. Gain insights into how businesses, governments, and users can collaborate to build secure, user-controlled digital identities that power the digital economy and metaverse.
Making every day-in-the-life of frontline workers frictionless & secure!
Get the latest updates! Subscribe now!
Thank you! Your submission has been received!
Oops! Something went wrong while submitting the form.



