The OLOID Blog
Insights on identity, access, and security for the modern frontline workforce.

Featured
HIPAA Access Control Checklist: A Practical Guide for 2026
The HIPAA access control checklist covers the technical, administrative, and physical safeguards that govern who can access electronic protected health information, under what conditions, and with full audit trail accountability. Most organizations underestimate where their access control program breaks down in practice, particularly around shared devices, over-privileged accounts, and access that outlasts employment or role changes. This guide covers what HIPAA's Security Rule requires for access controls, what real OCR enforcement cases reveal about the most common compliance gaps, and what compliant identity and access management looks like in clinical and frontline environments.
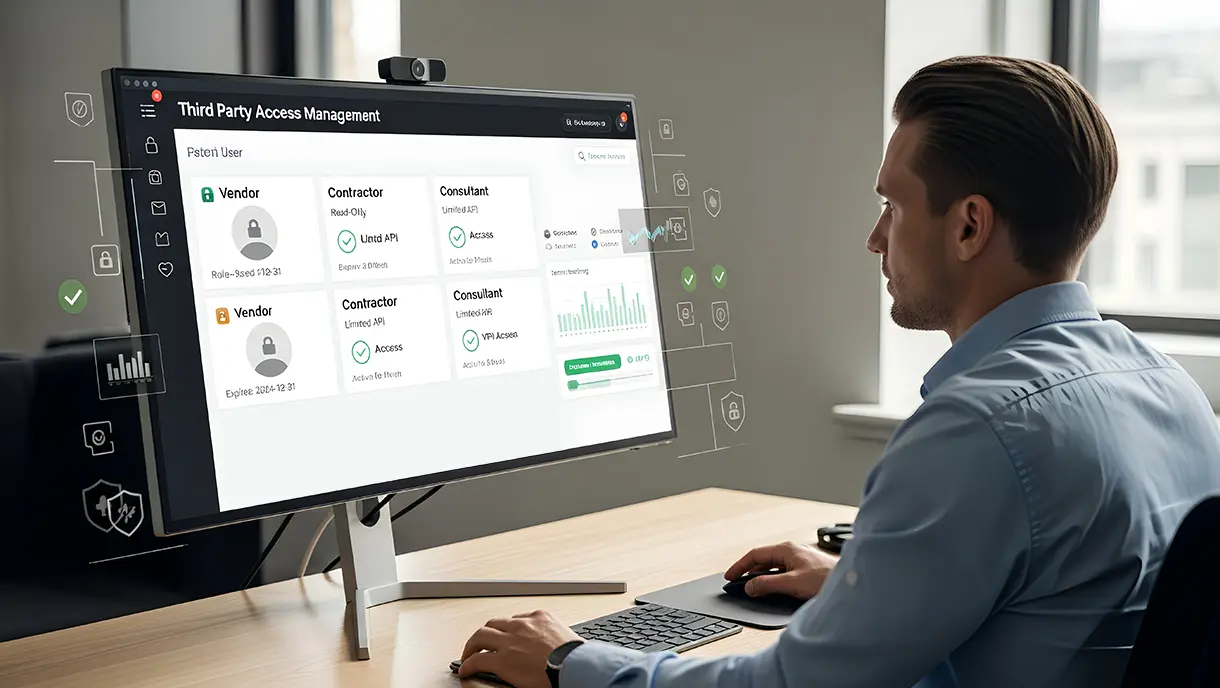
Third-Party Access Management: A Complete Guide to Secure Vendor Access
Third-party access management governs how external vendors, contractors, and partners access internal systems and data. Organizations face growing risks from uncontrolled vendor privileges, making structured access policies essential. This blog covers risk factors, implementation strategies, and security best practices. You'll learn how to balance business needs with robust protection for your critical assets.
2FA Bypass: How Attackers Break Two-Factor Authentication (And How to Prevent It)
Two-factor authentication adds an extra layer of security beyond passwords, but attackers continually develop methods to circumvent these protections. This guide explores standard 2FA bypass techniques, including phishing, SIM swapping, session hijacking, and push notification abuse. Learn why traditional 2FA methods fail and learn modern alternatives and prevention strategies using phishing-resistant authentication, biometrics, and passwordless solutions.

Understanding Authentication Protocols and How They Work
Authentication protocols establish secure communication between users, devices, and applications. These standardized frameworks verify identity before granting access to resources. Organizations use protocols like OAuth, SAML, and Kerberos across different environments. This guide explains how protocols work, their benefits, and practical implementation strategies for enterprises.

Zero-Trust Implementation Guide: Steps, Policies, & Best Practices
Zero-Trust Implementation transforms traditional security by continuously verifying every access request. Organizations adopt this model to protect against modern threats like credential theft and lateral movement. This guide provides practical steps, technical architecture insights, and real-world use cases. Enterprise security teams gain actionable frameworks for deploying Zero-Trust across hybrid environments.
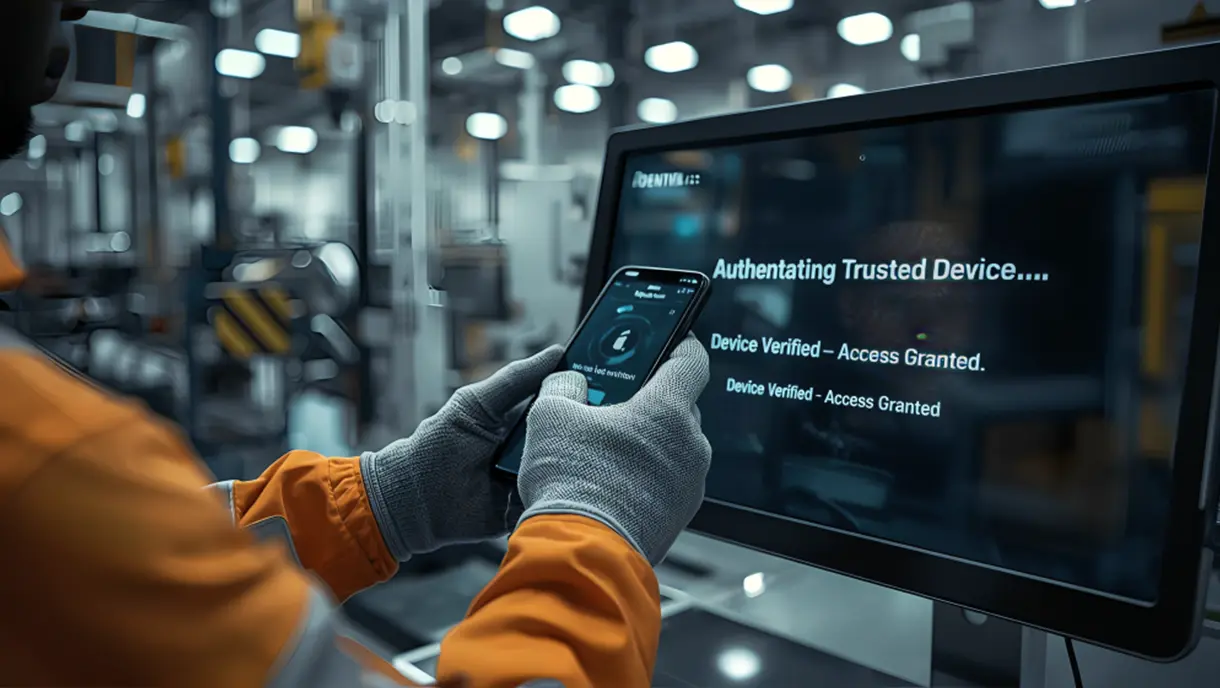
Device-Based Authentication: A Complete Guide for Modern Security
Device-based authentication links user access to trusted devices instead of passwords. This method uses cryptographic keys stored in secure hardware to verify identity. Organizations gain stronger security against phishing while eliminating the costs of password management. This blog covers definitions, technical workflows, business benefits, deployment strategies, and compliance requirements for modern authentication systems.

Touchless Access Control for Modern Facilities: A Complete Guide
Touchless access control is transforming workplace security by enabling fast, hygienic, and contactless entry. This guide explores touchless access control as a transformative security solution for modern workplaces. Learn how hands-free entry technologies improve hygiene, enhance security, and accelerate movement through facilities.

Credential Phishing: How Cybercriminals Steal Login Data and How to Stop Them
Credential phishing represents one of the most prevalent and damaging cyber threats facing organizations today. Attackers use deceptive emails, fake login pages, and social engineering tactics to steal usernames and passwords. This guide explains how credential phishing works, explores common attack variants, and examines advanced techniques that bypass traditional defenses. Learn about business impacts, prevention strategies, and phishing-resistant authentication methods that effectively protect organizations from credential theft.
.webp)
Authentication Logs: What They Are, How They Work, and Why They Matter
Authentication logs provide critical visibility into every access attempt across your digital infrastructure. These records capture login events, failed attempts, and user behavior patterns that reveal security threats. This blog explores what authentication logs capture, why they matter for security, and how to manage them effectively. Learn log types, analysis techniques, management best practices, compliance requirements, and tools that strengthen your security posture.

What Is MFA Fatigue and How to Prevent It: Tips and Strategies
Multi-factor authentication protects accounts by requiring additional verification beyond passwords. MFA Fatigue occurs when attackers exploit authentication systems by bombarding users with repeated push notifications until victims approve fraudulent login attempts. Learn how MFA fatigue attacks work, their devastating impact on organizations, and comprehensive defense strategies to protect against this social engineering threat.

2FA vs MFA: What's the Difference and Which Authentication Method Fits Your Organization
Access authentication determines how users verify their identity before accessing organizational resources. Two-Factor Authentication (2FA) requires exactly two verification methods, whereas Multi-Factor Authentication (MFA) requires two or more. This guide explains how each method operates, its security differences, and practical implementation considerations. Learn about real-world examples, detailed comparisons across security and usability, and decision frameworks for selecting between authentication approaches.

What Is Access Control? Definition, Workflow, Models & Real-World Use Cases
This comprehensive guide explores access control as a critical security framework for protecting digital and physical resources. It covers fundamental definitions, various control models like RBAC and ABAC, implementation workflows, and real-world applications. You'll discover best practices for secure deployment, common challenges organizations face, and emerging trends shaping the future of access management.

Continuous Authentication: What It Is, How It Works, Benefits & Best Practices
Continuous authentication represents a fundamental shift in identity security. Traditional login methods verify users once and grant lasting access. This approach leaves systems vulnerable to session hijacking and credential theft. This guide explores the definition, core components, implementation strategies, real-world applications, and best practices of continuous authentication. Learn how behavioral biometrics, contextual signals, and machine learning enable real-time identity verification.
HIPAA-Compliant Authentication: Requirements, Methods, Best Practices & Implementation
HIPAA-compliant authentication ensures secure identity verification before accessing protected health information. This guide explains the technical safeguard requirements and approved authentication methods for the security rule. Learn how to implement HIPAA-compliant authentication methods, best practices, and how modern solutions meet compliance obligations.

Smart Card Authentication: A Complete Guide
Smart card authentication delivers hardware-backed identity verification for high-security workforce access. This comprehensive guide examines the operation, architecture, and implementation considerations of smart cards. Learn the benefits, practical use cases, and implementation best practices for deploying smart card authentication.

Workforce Identity and Access Management Explained: Framework, Benefits, and Best Practices
Workforce Identity and Access Management (IAM) is the foundation of modern enterprise security. It controls how employees, contractors, and partners access digital resources. This guide covers core IAM components, architecture patterns, implementation strategies, and best practices. Learn how to automate identity lifecycles, enforce authentication standards, and meet compliance requirements.

Top 10 Challenges Faced by Frontline Workers and How to Overcome Them
Frontline workers encounter unique obstacles that impact their performance, satisfaction, and well-being. This comprehensive guide explores the top ten challenges faced by frontline workers across industries. It includes workplace stress, lack of recognition, limited resources, safety risks, and retention issues. Each challenge is accompanied by practical, actionable solutions organizations can implement to support their workforce and drive operational success.

Is Passwordless Authentication Safe for Modern Businesses? Expert Insights
Passwordless authentication replaces traditional passwords with cryptographic keys, biometrics, and device-based verification methods. Organizations adopt these systems to eliminate credential theft, reduce phishing attacks, and remove password management overhead. This guide explains how passwordless authentication is safer than traditional passwords. Get a comparison of different passwordless methods and learn which approach best suits specific use cases.

Access Control in Healthcare: Models, Best Practices, and Compliance Explained
Access control in healthcare manages who can access sensitive patient data, clinical systems, and physical facilities. This comprehensive guide explores both digital and physical access control strategies. It covers regulatory compliance requirements, implementation challenges, and emerging technologies. Learn how healthcare organizations protect data, ensure patient safety, and maintain operational efficiency through robust access management.

Complete Zero Trust Security Guide for Modern Businesses
Zero-Trust Security represents a fundamental shift in how organizations approach cybersecurity in today's digital landscape. This framework operates on the principle that no user or device should be trusted by default. The guide covers core zero-trust principles, compelling benefits, and practical implementation strategies for modern enterprises. Explore the real-world applications of Zero-Trust across remote work, cloud security, and compliance scenarios.

Role-Based Access Control (RBAC): A Complete Guide for Secure Access Management
Role-Based Access Control (RBAC) has become the foundation of modern access management for organizations worldwide. RBAC simplifies security by assigning permissions based on job roles rather than individual users. This guide explains how RBAC strengthens data protection, streamlines user management, and supports compliance requirements. Learn practical implementation approaches, industry-specific applications, and strategies for overcoming common obstacles.
What Is Single Sign-On (SSO) and How Does It Work?
Single Sign-On (SSO) transforms how organizations manage user authentication across multiple applications and services. This comprehensive guide explores what SSO is, how it works, and why it matters for modern enterprises. Learn about different SSO types, implementation protocols, and the key advantages of adopting SSO solutions. The guide also covers practical use cases, step-by-step implementation processes, and expert advice on choosing the right SSO provider.

What Is Biometric Authentication And How Does It Work?
Biometric authentication has transformed how organizations verify identity and secure access. This technology uses unique physical or behavioral traits like fingerprints, facial features, or voice patterns to replace vulnerable password-based systems. This guide covers the fundamentals of biometric authentication, including how the technology works and the various types available. You'll find practical implementation strategies, real-world industry applications, and key benefits for enterprises.

Attribute-Based Access Control (ABAC): A Complete Guide
Attribute-Based Access Control (ABAC) revolutionizes how organizations manage access by evaluating user, resource, and environmental attributes, rather than relying on fixed roles and permissions. This comprehensive guide explores what ABAC is, how it works, and why it matters for modern enterprises. Learn about the key components, top benefits, practical use cases, and best practices for implementing ABAC.

Final Thoughts on Two-Factor Authentication
Two-factor authentication (2FA) adds a critical security layer beyond passwords to protect your digital accounts. This comprehensive guide explores what 2FA is, how it works, and why it matters for both individuals and enterprises. Learn common authentication methods, key benefits, real-world applications, and best practices for implementation.

What Is Passwordless MFA? A Complete Guide to Secure and Frictionless Authentication
Passwordless MFA eliminates traditional passwords while maintaining multi-factor security through biometrics, security keys, and device-based authentication. This comprehensive guide explores what passwordless MFA is, its business benefits, implementation strategies, and best practices for overcoming common challenges. Learn how leading organizations are adopting passwordless multi-factor authentication to strengthen security, improve user experience, reduce IT costs, and meet compliance requirements.

Wage Theft vs Time Theft: Understanding the Difference and How to Prevent Both
Wage theft and time theft represent opposing workplace violations that erode trust and productivity. This guide clarifies the distinction between employer-driven wage violations and employee time manipulation. Explore common examples of each, understand their legal and ethical implications, and discover how they damage workplace culture.

Unified Identity Management Explained: How It Simplifies Enterprise Security
Unified Identity Management (UIM) consolidates digital identities into a single authoritative system, eliminating fragmentation across enterprise platforms. This comprehensive guide examines how centralized identity repositories function, the security benefits they offer, and their role in ensuring regulatory compliance. Explore implementation strategies, real-world applications across hybrid environments, and expert tips for successful deployment.

What Is Multimodal Biometric Authentication and How Does It Work?
Multimodal biometric authentication combines multiple biometric traits to create highly secure identity verification systems. This comprehensive guide examines how these advanced systems operate, their key advantages, and practical implementation strategies. Learn about different biometric modalities, fusion techniques, industry applications, and best practices for deployment.

RBAC vs ABAC: What’s the Difference and Which Access Control Model Fits Your Organization
Access control determines who can access organizational resources and under what conditions. Role-Based Access Control (RBAC) assigns permissions through predefined job roles, while Attribute-Based Access Control (ABAC) evaluates multiple attributes dynamically. Learn how each model operates, their architectural differences, and practical implementation considerations. The guide covers real-world examples, provides detailed comparisons across scalability and security, and offers decision frameworks for selecting between models.

A Step-by-Step Guide for Implementing Passwordless Authentication
How to move beyond passwords and implement passwordless authentication without disrupting users? What does it take to implement passwordless authentication securely and at scale? This blog breaks down a 7-step implementation process, common challenges enterprises face, and best practices for smooth adoption.
Making every day-in-the-life of frontline workers frictionless & secure!
Get the latest updates! Subscribe now!



