Single Sign-On (SSO) vs. Federation: A Complete Guide
Key Takeaways
- Single Sign-On allows users to access multiple applications using one set of credentials within a single organization.
- Federated Identity Management enables secure authentication across domains.
- SSO improves user experience and centralizes authentication control.
- Federation enables cross-organization collaboration through trusted identity providers.
- SSO and federation often work together in federated SSO architectures.
- Neither model alone solves shared-device authentication challenges.
- Zero Trust requires continuous validation beyond initial login.
- OLOID extends secure access enforcement to shared and frontline endpoints.
At 6:02 a.m., the night shift walks off the manufacturing floor. Three minutes later, the day shift approaches the same workstation. The device remains the same, but the users change. Each person needs secure access immediately, and each must authenticate before work begins.
Most discussions around SSO vs. federation assume one employee using one personal device for an entire workday. That assumption no longer reflects how identity operates across modern organizations. Identity is now the primary attack surface. The Verizon Data Breach Investigations Report found that 68 percent of breaches involve a human element, including stolen credentials and misuse. At the same time, distributed and frontline work models continue to expand, increasing shared devices and cross-domain access requirements.
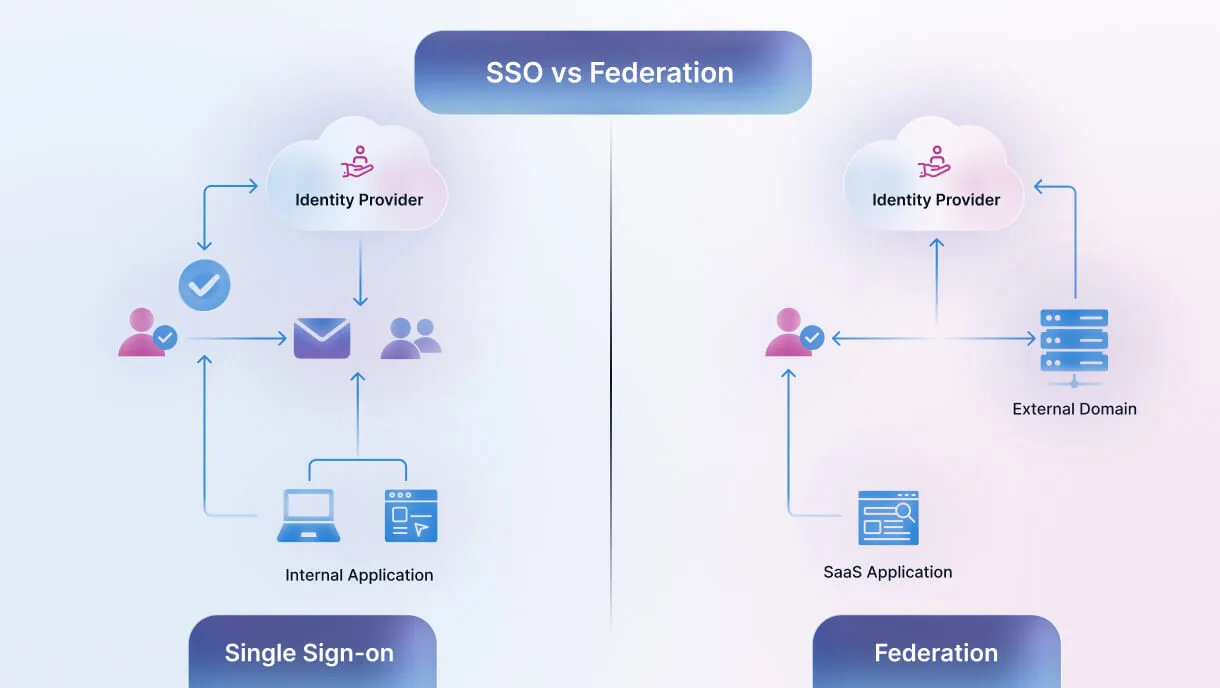
To understand SSO vs Federation clearly, we must separate user experience from trust architecture. One model simplifies login within a single organization. The other establishes trust across domains. Confusing the two leads to weak identity design decisions. Before going deeper, let’s define the terms precisely.
Single Sign-On (SSO) allows users to authenticate once and use a single set of credentials to access multiple applications within a single organization.
Federated Identity Management (FIM) allows one organization to trust and accept authentication performed by another organization across domains.
SSO improves internal user access efficiency. Federation enables identity trust across organizational boundaries. This is the foundational distinction in the SSO vs Federation discussion.
This guide explains the difference between SSO and federation, how they work together, where they fit in Zero Trust, and why traditional models break down in shared-device environments.
What is Single Sign-On (SSO) and How Does it Work?
Single Sign-On allows users to access multiple applications using one set of credentials. Instead of entering a password for every login, the user authenticates once through a central identity provider (IdP).
Here’s how it works:
The identity provider verifies the user’s credentials. Once authenticated, it issues a secure token. Connected service providers trust that token and grant access to applications without repeated logins. This allows users to access various internal systems such as email, HR platforms, and dashboards using a single set of credentials within a single organization.
Why Organizations Use SSO
SSO improves user experience by reducing password fatigue. It simplifies identity and access management policies and enables consistent enforcement of MFA controls. It also centralizes authentication monitoring within a single identity provider.
However, SSO centralizes risk. If a credential is compromised, attackers can gain access to multiple systems. That is why SSO must be implemented securely and monitored continuously.
What is the Federation?
Federation is a trust model that allows one organization to accept authentication from another. In a federated identity setup, a user authenticates with their home identity provider (IdP). That authentication is then trusted by an external system, often called the service provider. Authentication occurs in one domain, and access is granted in another.
For example, an enterprise employee logs into a SaaS platform using corporate credentials. The SaaS platform does not create a new username and password. Instead, it redirects the user to the enterprise identity provider. Once authenticated, the identity provider sends a secure assertion back to the SaaS application, which then grants access.
This cross-domain authentication model is formally known as Federated Identity Management (FIM), but in practice it is simply referred to as federation.
Federation typically relies on standards such as:
- Security Assertion Markup Language (SAML)
- OpenID Connect
- OAuth
These protocols securely exchange authentication data between identity providers and service providers, enabling secure access without duplicating accounts.
SSO vs Federation: Key Differences Explained
In the SSO vs Federation comparison, SSO determines how users access multiple applications after authentication, while federation determines which identity providers are trusted to authenticate users across domains.
They address different layers of identity architecture.
SSO and Federation: How They Work Together in Modern Identity Architecture
In enterprise environments, SSO and federation operate in complementary layers.
Federation establishes the trust relationship between identity providers across domains. It determines which external identity source is authorized to authenticate users. SSO delivers a seamless login experience once authentication succeeds, allowing users to access multiple applications without repeated prompts.
This combined approach is often referred to as federated SSO. In this model, federated authentication verifies identity through an external identity provider using standards such as SAML or OpenID Connect. Once verified, single sign-on manages session reuse within the service provider’s environment. Federation answers which domain is trusted to authenticate. SSO answers how authentication is reused efficiently within that trusted context.
In real deployments, SSO vs Federation decisions shape how identity scales across internal systems, partner ecosystems, and SaaS platforms.
Benefits of Federated Identity in Enterprise and SaaS Environments
Federation is often the deciding factor in enterprise SaaS adoption because large organizations require authentication through their own identity provider.
Federation reduces credential duplication by eliminating the need to create separate accounts in every external system. Users authenticate through their home identity provider, and the service provider grants access based on a trusted assertion. This reduces password sprawl and lowers the risk associated with unmanaged credentials. It also strengthens governance. Identity ownership remains with the originating organization, making user lifecycle management, role changes, and de-provisioning more controlled and auditable across domains.
For SaaS providers, supporting federation is often mandatory. Enterprise buyers frequently require SAML or OpenID Connect support before approving vendor access, making federation a contractual requirement rather than a convenience feature.
When to Use SSO and When Federation is Required
The SSO vs Federation decision depends on where identity trust must operate. Use SSO when you need to streamline access to applications within a single organization. It improves usability and centralizes authentication control under one identity provider.
Federation is required when identity must be recognized across organizational boundaries. This includes B2B collaboration, vendor portals, and enterprise SaaS integrations where authentication happens in one domain and access is granted in another. Most modern organizations require both. SSO simplifies internal user access. Federation enables secure cross-domain collaboration. Understanding SSO vs Federation in this context ensures identity architecture aligns with business structure rather than default tooling.
How to Implement SSO and Federation Securely
Secure implementation starts with a strong identity provider and clearly defined trust policies. Organizations should enforce MFA, validate SAML assertions, monitor OAuth token usage, and regularly review federation configurations. Logging should track authentication events across domains.
Trust relationships must clearly define which attributes are shared between identity provider and service provider. Session management policies should define timeouts and re-authentication triggers. In shared-device environments, implementation must also account for endpoint validation, device context, and rapid user transitions.
The Operational Identity Gap
Now return to that 6:05 a.m. workstation.
Shared devices are common across manufacturing floors, hospital stations, retail terminals, and warehouse scanners. Workers rotate by shift. Devices are reused continuously. Login speed directly affects productivity. Traditional identity and access management systems were designed for persistent sessions and named devices. They assume stable user-device relationships. Operational reality is different.
Authentication must happen quickly. Badge taps often replace typed passwords. Proximity can determine user access. Sessions may need to terminate automatically when a worker walks away. Federation solves cross-domain trust. SSO simplifies internal login. Neither was designed to continuously validate identity at shared endpoints. This is the operational identity gap.
Bridging that gap requires identity models that extend beyond login events and incorporate physical presence and device awareness. OLOID integrates with existing identity providers and federation frameworks to extend secure access controls to shared frontline devices. It enables badge-based, passwordless authentication and proximity-driven verification without disrupting workflow. SSO and federation establish digital trust. OLOID operationalizes that trust at the endpoint.
[[cta]]
SSO and Federation in Zero Trust
Zero Trust requires continuous verification. Trust is not granted based on network location or prior login. In a Zero Trust architecture, SSO vs Federation plays different roles in identity validation.
Federation enables secure identity validation across domains by establishing trusted authentication between identity providers. SSO centralizes authentication enforcement within an organization and simplifies user access once trust is established. However, Zero Trust also requires contextual evaluation. Identity assurance must consider device state, session duration, and behavioral signals before granting access to applications. In shared-device environments, identity must be validated continuously. Leaving a session active increases exposure, while forcing manual logout processes reduces efficiency.
Understanding SSO vs Federation is essential when designing Zero Trust enforcement across shared endpoints. The Federation establishes who is trusted to authenticate. SSO manages how access is reused. Zero Trust determines whether that access should continue. In operational settings, authentication models must align with workflow speed and endpoint context, not just login events.
Why Traditional SSO and Federation Break in Shared-Device Environments
In high-velocity environments, identity risks escalate. Password reuse becomes common. Session hijacking risks increase. Frequent login prompts cause fatigue. Badge sharing can occur when authentication feels cumbersome. MFA challenges that interrupt workflows are often bypassed.
Security controls that slow production lines or delay patient care do not last. Modern identity must be fast, context-aware, and passwordless where possible. It must integrate physical and digital access controls into one enforcement layer. Authentication must validate the right user, on the right device, at the right time, before granting access to applications.
Choosing the Right Identity Model for Your Organization
There is no universal identity model. SaaS companies require federation to support enterprise customers. SSO improves product usability and retention. Enterprise IT teams rely on centralized SSO to simplify identity and access management while using federation to collaborate securely across domains.
Industrial, healthcare, and frontline environments require shared-device authentication models that reduce password friction and incorporate physical context. Hybrid organizations require federation for cross-domain trust, SSO for internal efficiency, and endpoint-level controls for shared systems. Identity architecture must reflect how users actually access systems, not how diagrams assume they do.
Beyond SSO vs Federation: Securing Real-World Access
The SSO vs Federation discussion is foundational to modern identity architecture, but it does not end there. Single Sign-On allows users to access multiple applications within a single organization using one set of credentials. Federation enables identity trust across domains through standards such as SAML, OpenID Connect, and OAuth. Together, they form the backbone of secure digital collaboration.
However, the traditional SSO vs Federation model was built around stable user-device relationships. Shared-device and frontline environments introduce challenges these models were not originally designed to address. Zero Trust requires continuous validation, device context awareness, and secure access aligned with operational speed.
For organizations operating beyond office desktops, identity must extend to the endpoint. That is where operational identity solutions such as OLOID reinforce and extend existing federation and SSO frameworks. Identity must work where work happens.
FAQs
1. What is the difference between SSO and federation?
SSO allows users to log in once and access multiple applications within a single organization using one set of credentials. Federation allows one organization to trust authentication performed by another organization across domains. SSO simplifies internal access. Federation enables cross-organization trust.
2. What is federated SSO?
Federated SSO combines federated authentication with single sign-on. An external identity provider authenticates the user using standards such as SAML or OpenID Connect, and the service provider grants access across connected applications without repeated logins.
3. Can you implement SSO without federation?
Yes. Many organizations implement SSO within a single organization without establishing cross-domain trust. Federation becomes necessary when identity must be recognized across separate domains.
4. How do SSO and federation support secure access in Zero Trust?
Federation enables identity validation across domains, while SSO centralizes authentication enforcement. Zero Trust builds on both by requiring continuous verification and contextual access decisions.
5. Why are SSO and federation not enough for shared devices?
Both models assume stable user-device relationships. In shared environments, authentication must account for rapid user changes, device reuse, and physical presence. Additional endpoint-level controls are required to maintain secure access.


Get the latest updates! Subscribe now!


