Healthcare's Future in AI era Starts with Identity
ViVE showcased healthcare's AI ambition. HIMSS sharpened the urgency. And the Stryker cyberattack reminded the industry that innovation only scales when the trust layer underneath it is resilient.

At ViVE 2026 in Los Angeles, the conversations felt optimistic. At HIMSS26 in Las Vegas, they felt more urgent. Across both events, one theme kept surfacing: healthcare is ready to move. Leaders want to modernize infrastructure that has been stretched for decades, put AI to work in meaningful ways, and finally make technology less burdensome for clinicians.
INCIDENT · MARCH 11, 2026
In the middle of HIMSS, Stryker disclosed a cybersecurity incident causing global disruption affecting order processing, manufacturing, and shipping. By March 17, Reuters reported the attack had been contained and restoration was underway. No ransomware or malware was confirmed. Connected products were not impacted.
That moment captured the healthcare paradox in real time.
The industry wants AI, automation, better workflows, and more seamless digital experiences. But healthcare does not run on ambition alone. It runs on trust, continuity, and accountability. When those foundations wobble, the impact is immediate.
And that is why identity matters.
"Identity rarely gets keynote billing. But it is the layer that determines whether users, devices, applications, contractors, and increasingly AI agents can interact safely and reliably. In healthcare, identity is not just an IT function. It is infrastructure."
Healthcare Is Ready to Move Beyond the Legacy Tax
For years, healthcare has layered modern tools onto old foundations.
Electronic health records expanded digital workflows. Cloud services multiplied applications. Mobile devices changed where and how clinicians access information. Now AI is reshaping documentation, decision support, and operational workflows.
But underneath all that progress, many organizations still rely on fragmented identity systems, duplicated credentials, inconsistent access policies, and authentication models designed for a more static, office-based world.
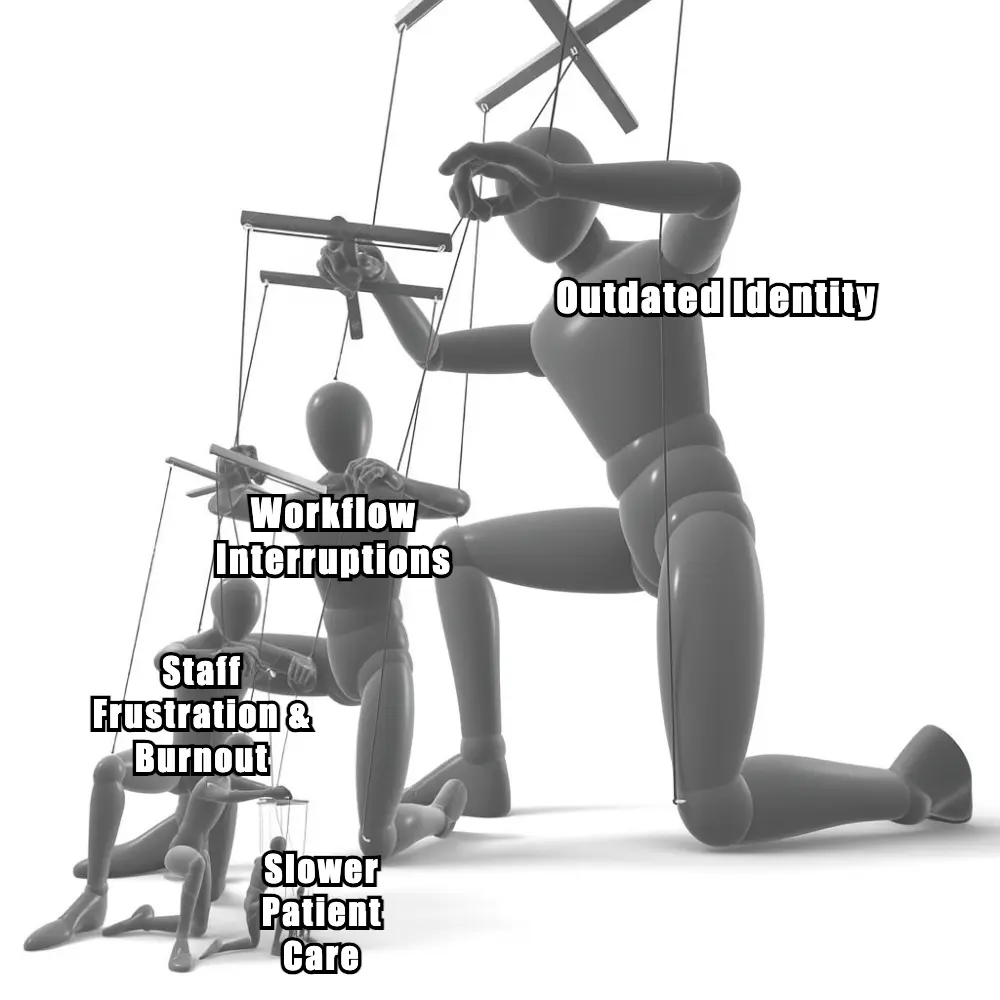
That creates a quiet but costly legacy tax.
Clinicians pay it in extra logins, repeated re-authentication, and broken workflow continuity. IT teams pay it in complexity. Security teams pay it in limited visibility and uneven governance. Everyone pays it in lost time.
Healthcare leaders increasingly recognize that modernization is not just about adding one more application or one more AI layer. It is about removing the small, constant points of friction that slow people down every day. And that friction often starts with authentication.

Friction Starts Small — Then Multiplies
In healthcare, workflow friction rarely shows up as one dramatic failure. More often, it arrives as a series of small interruptions:
- A nurse re-authenticates across multiple apps during a busy shift.
- A physician moves between inpatient, ambulatory, and specialty workflows and loses context along the way.
- A contractor needs short-term access, but provisioning takes too long or grants too much.
- A clinician at a shared workstation is forced into repeated logins because the access model was built for dedicated desktops, not dynamic care environments.
Each moment looks minor on its own. Together, they create drag.
That drag slows care, increases cognitive load, encourages workarounds, and weakens the user experience at exactly the point where healthcare can least afford it. In environments already dealing with staffing shortages and burnout, those "small" interruptions are not small at all.
This is why modern authentication matters. Fast, phishing-resistant, context-aware access is not a convenience feature. It is part of clinical workflow design.
The Stryker Incident Was Also a Lesson in Resilience
The Stryker incident was a timely reminder that cyber events in healthcare are rarely confined to the security team. They quickly become operational events.
Even when patient-facing services and connected products remain unaffected, disruption to internal systems can still ripple outward through ordering, manufacturing, shipping, support, and third-party dependencies. An incident does not need to touch a bedside device to matter to care delivery.
That is the bigger lesson.
Healthcare's digital ecosystem is deeply interconnected. A hospital may have strong internal controls, but it still depends on vendors, service providers, logistics systems, clinical platforms, and support teams operating reliably around it. When one important node is disrupted, the question becomes: how well can the rest of the system absorb the shock?
That is where modern identity infrastructure becomes part of resilience. Identity has to do more than verify a login. It has to help organizations understand who and what has access, enforce policy consistently, isolate risk faster, support temporary access when needed, and maintain continuity when parts of the environment are under stress.
In a sector where trust relationships stretch across clinicians, contractors, applications, devices, and vendors, resilience depends on having a clear trust model before disruption happens — not after.
AI Makes the Identity Challenge Bigger
AI dominated conversations at both ViVE and HIMSS. That momentum is real.
But AI does not float above infrastructure. It depends on it.
Before an AI assistant can summarize a chart, route a task, draft a response, or automate an administrative step, the organization has to answer a few non-negotiable questions:
- Who initiated the action?
- On whose authority is the action running?
- What systems and data can it access?
- Which policies apply in that moment?
- How is the activity being recorded for audit and accountability?
This is where identity becomes the control layer for healthcare AI.
And this is not just operational hygiene. The HIPAA Security Rule requires appropriate safeguards for electronic protected health information, and federal regulations specifically call for audit controls that record and examine activity in systems that contain or use ePHI.
If those identity questions are not answered clearly, AI becomes harder to trust, harder to govern, and harder to scale. Healthcare does not need AI that is merely impressive. It needs AI that is governable.
What Modern Identity Infrastructure Should Deliver
For healthcare organizations, a stronger identity foundation should enable five things at once:
Low-friction clinician access : Fast, secure authentication across shared workstations, mobile devices, and clinical applications.
Unified identity across humans and machines: Workforce users, contractors, service accounts, devices, bots, and AI agents governed within a coherent trust framework.
Context-aware access decisions: Access that reflects role, device, location, workflow, and risk — not just whether a password was entered.
Clear auditability and accountability: Reliable visibility into who accessed what, when, why, and under whose authority.
Operational resilience: Rapid provisioning, rapid revocation, and strong continuity planning when a vendor or internal system is disrupted.
When those capabilities are in place, the benefits compound. Clinicians lose less time. Security teams gain better visibility. Compliance teams get cleaner audit trails. And AI initiatives move forward with stronger guardrails.
Better Identity Can Also Mean Better Experience
One of the more encouraging shifts in healthcare is that identity is finally becoming more usable.
Secure mobile credentials, tap-to-login experiences, stronger phishing resistance, and more portable digital identity models can better match the reality of healthcare work: people moving constantly between rooms, devices, buildings, and systems. That opportunity extends to patients too.
Over time, better digital identity models can reduce check-in friction, improve consent workflows, and strengthen verification without turning every encounter into a paperwork relay race.
Healthcare has lived too long with the assumption that secure access must also be cumbersome. It does not.
"AI may be the headline act. Identity is the control plane."
The Real Foundation for Healthcare AI
The biggest takeaway from ViVE and HIMSS this year is not that healthcare lacks ambition. The ambition is already here.
What the industry needs now is the infrastructure that makes that ambition safe, usable, and resilient.
Modernize identity first. Simplify clinician access next. Then build the governance and trust layer that lets AI and automation operate responsibly at scale.
Healthcare does not have an AI enthusiasm problem. It has an identity maturity gap.
And if healthcare closes that gap, the result will not just be better security. It will be better workflows, stronger resilience, clearer accountability, and a much more durable foundation for the next decade of digital health.



Get the latest updates! Subscribe now!


